Tokenized Bandwidth Explained: Can You Really Earn Crypto by Sharing Your Connection?

TL;DR
What is Tokenized Bandwidth anyway?
Ever wondered why you pay for a 1Gbps fiber line but only use a fraction of it while you're at work or sleeping? It’s like paying for a whole loaf of bread every day and only eating one slice, while the rest just sits there getting stale.
Tokenized bandwidth is basically a way to rent out that "stale bread"—your idle upload capacity—to people who actually need it. Instead of your ISP just pocketing your monthly fee while your router sits quiet, you turn your hardware into a tiny node in a global network.
- Sharing idle capacity: Most home connections are asymmetrical, but even that 20-50Mbps upload often sits at 0% usage. (Why are asymmetrical internet connections so common in ... - Quora) You're just letting others tunnel through your IP.
- Blockchain as the ledger: Since there's no central boss, a blockchain tracks exactly how many packets you routed. It ensures you get paid in tokens without needing to trust a shady middleman.
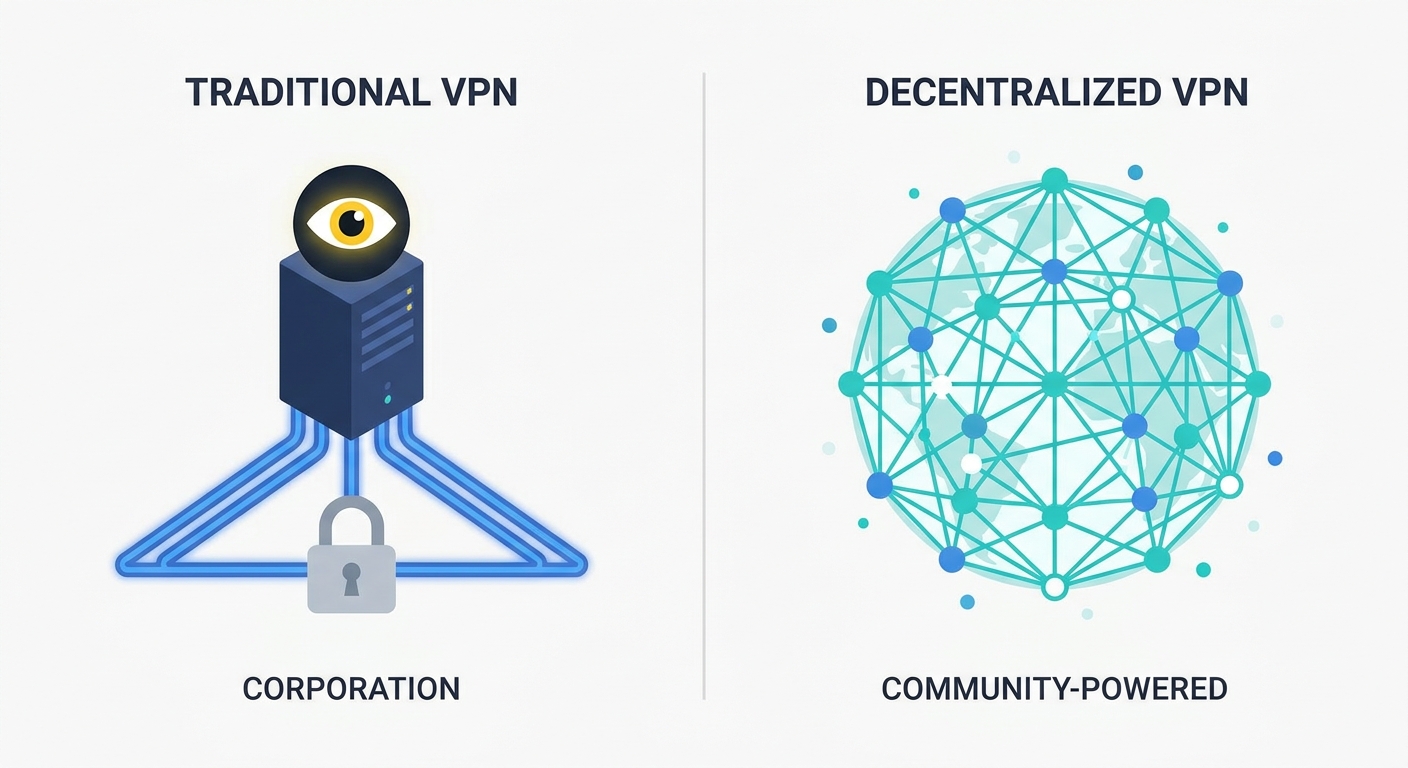
- P2P vs Centralized: Traditional VPNs own massive server farms (centralized). In a dVPN, the "servers" are just regular folks like you and me.
This isn't just for hobbyists anymore. In healthcare, researchers use these networks to move massive genomic datasets without hitting the bottlenecks of traditional corporate pipes. Even in finance, some firms look at p2p setups to avoid the prying eyes of standard isp logging.
According to a 2023 report by Messari, the DePIN sector (which includes bandwidth) is growing because it cuts infrastructure costs by over 70% compared to big cloud providers. It’s a massive shift in how we think about "owning" a connection.
But how do we actually move the data without the isp catching on? We use specific tunneling protocols and obfuscation tricks to hide the fact that you're sharing your line.
How the tech works under the hood
Think about your router for a second. It's basically a tiny computer that spends most of its life idling, just waiting for you to click a link. In a DePIN (Decentralized Physical Infrastructure Network) setup, we turn that lazy hardware into a functional node that earns its keep.
The whole idea behind depin is moving away from big server farms owned by giants and using "the edge"—aka, your living room. When you join a dVPN, your node advertises its availability to the network.
The Tunneling Secret Sauce
To keep your ISP from freaking out and cutting your service, these networks use advanced protocols.
- WireGuard & OpenVPN: These are the industry standards for encryption. They wrap your data in a secure layer so nobody can see what’s inside.
- Shadowsocks: This is a high-performance proxy that’s great at bypassing firewalls. It’s super popular in places with heavy censorship because it looks like normal web traffic.
- Obfuscation: Some nodes use "pluggable transports" which basically scrambles the metadata. It makes your vpn traffic look like a regular zoom call or a netflix stream so the isp doesn't throttle you.
Verification and Slashing
- Node Registration: Your device joins a p2p directory. It’s not like a normal VPN where everything goes to one company; here, traffic is routed through thousands of individual points.
- Smart Contract Escrow: Payments aren't handled by some guy in an office. According to research from Messari (2023), smart contracts automate the whole thing, so you get paid the second the data transfer is verified.
You might think people would just lie and say they shared 10GB when they did nothing. That's where "Proof of Bandwidth" protocols come in. The network sends tiny "heartbeat" packets to check your latency and throughput.
If your node drops packets or tries to spoof its location, the protocol slashes you. This isn't just a bad review—it usually involves a financial penalty where the network takes a portion of the tokens you "staked" (put up as collateral) to join. If you don't have a stake, you just lose all your pending rewards and future work. It’s a bit like a constant, automated audit.
Can you actually make money or is it a scam?
So, is this actually a way to make rent or just another crypto pipe dream? Honestly, it’s somewhere in the middle, but you aren't going to buy a private island by sharing your home fiber just yet.
Geographic Demand & Use Cases
The reality is that your "earnings" are basically a function of supply and demand in your specific zip code.
- Retail and localized testing: Companies in retail use these nodes to see how their websites look from different zip codes. They check if their localized pricing or ads are showing up right. If you live in a high-demand market like London or NYC, your node gets "pinged" more often and you make more.
- Web Scraping: ai companies need massive amounts of data to train their models. They use these networks to scrape the web from "clean" residential IPs so they don't get blocked by anti-bot tools.
There’s a few other things that actually dictate if you see green in your wallet:
- Token Volatility: You might earn 100 tokens today worth $50, but by the time you swap them on an exchange, they could be worth $5. It’s the classic crypto roller coaster.
- Hardware & Power: If you're running a beefy server 24/7, you gotta calculate if the token rewards actually cover your electricity bill. Most people just use a lightweight plug-and-play device to keep overhead low.
A 2024 report by Depin Ninja (which tracks these decentralized infra projects) explains that the top 10% of providers earn significantly more because they maintain 99.9% uptime. If your router resets every time someone uses the microwave, your reputation score tanks and so do your payouts.
SquirrelVPN provides great insights on how vpn tech is evolving and what users should look out for in this space, especially regarding how these protocols handle the "proof of work" without killing your cpu.
But what about the legal side? If someone uses your IP to do something shady, are you the one getting the knock on the door? Let's dig into the security risks.
The Privacy and Security Catch
Ever thought about what actually happens when some stranger in another country uses your home IP to browse the web? It’s a bit like giving a spare key to your house to a random person—sure, they might just want to watch Netflix, but they could also be raiding the fridge or worse.
The biggest headache with sharing bandwidth is the "exit node" problem. When you act as a node, your IP address is the one that shows up in server logs. If a user on the network decides to download pirated movies or hit a government site, the trail leads straight back to your living room.
- Legal Liability: Most ISPs have strict terms against reselling your connection. If they see weird traffic patterns, they might just throttle you or kill your account entirely.
- Malicious Traffic: Even if the user isn't a criminal, they might be running bots that get your IP blacklisted from sites like Google or Amazon, making your own browsing a nightmare of captchas.
- Snooping Risks: While most dVPNs encrypt data, if the protocol has a flaw, a sophisticated attacker could try to sniff packets on your local network.
To fix this, developers use something called "sandboxing" or containerization. Basically, the traffic from the dVPN is kept in a separate digital "tube" that can't talk to your home laptop or printer.
Many networks now use multi-hop routing. Instead of one person going through your IP, the data is split. You might only handle a tiny, encrypted chunk of a file, so you never actually "see" the whole request. End-to-end encryption handles the actual data privacy, while some networks use zero-knowledge proofs (ZKP) for compliance. In healthcare, ZKPs allow a node to prove it meets security standards or identity requirements without actually revealing sensitive patient info or the node owner's personal details.
Honestly, the trade-off is simple: you’re trading a bit of your digital footprint for those tokens. Is the risk worth a few bucks a month?
Let's look at where this is all heading and if these networks can actually survive the long haul.
Future of the Decentralized Internet
So, is this whole p2p bandwidth thing actually gonna kill off the big ISPs? Honestly, probably not next week, but we are definitely seeing a shift toward a more decentralized internet where you own your "exit."
Right now, these networks face some real technical hurdles that keep them from going totally mainstream.
- Latency issues: Routing packets through a guy’s basement in Berlin and then a laptop in Tokyo adds serious lag, which is a nightmare for real-time communication or video conferencing where every millisecond counts.
- Censorship resistance: In countries with heavy firewalls, tokenized networks are a godsend because there’s no single ip for the government to block.
- Economic sustainability: According to a 2024 analysis by CoinGecko, the longevity of depin projects depends on real-world utility—like companies buying bandwidth for ai scraping—rather than just speculative token farming.
It’s a messy, exciting frontier. Whether you’re a privacy nut or just want to earn a few tokens, the bandwidth sharing economy is finally making the web feel like it belongs to us again. Just watch those data caps, yeah?