Decentralized Autonomous Routing for Global VPN Nodes

TL;DR
Introduction to Autonomous Routing in dVPN
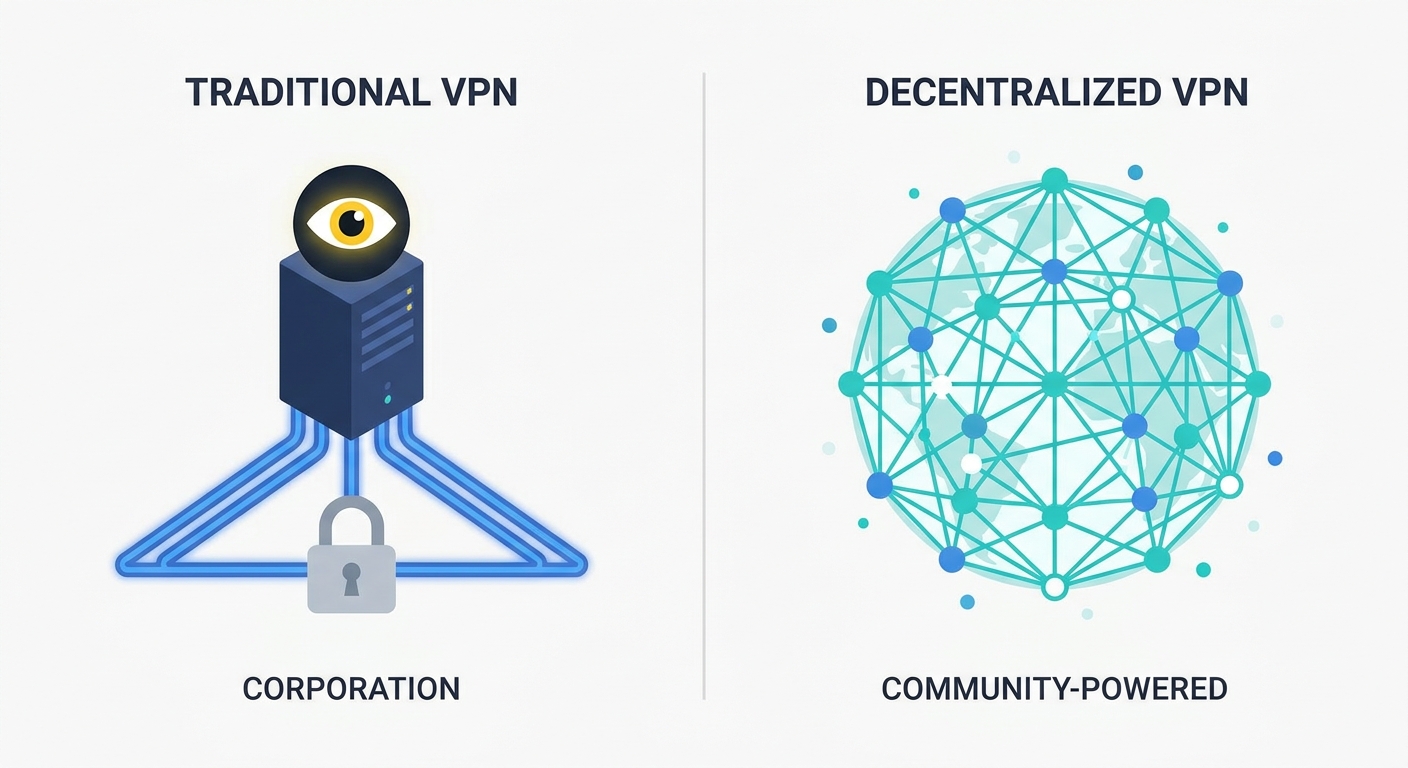
Ever wonder why your "no-logs" VPN still feels like a black box controlled by some random company in a tax haven? Honestly, the traditional model is broken because it relies on us trusting a single entity not to peek at our packets.
In a standard setup, you connect to a server owned by a provider. In a dVPN, we're talking about Autonomous Routing, where the network itself figures out how to move data without a central boss. It’s the shift from manual server management to p2p node discovery.
Instead of a ceo deciding where a new server goes, the network uses depin (Decentralized Physical Infrastructure Networks) to let anyone share their extra bandwidth. This is made possible by protocols like IP-over-P2P (IPOP), which uses a Distributed Hash Table (dht) to map IP addresses to p2p identifiers.
According to GroupVPN.dvi, a 2010 paper from the University of Florida, this allows for "self-configuring virtual networks" that don't need a central coordinator to function.
- Automated Discovery: Nodes find each other using a structured overlay (like a chord or symphony ring) instead of a hardcoded list of servers.
- Dynamic Scaling: The network grows naturally as more people join; there's no "capacity limit" set by a corporate budget.
- Resilience: If one node goes down, the routing algorithm just bypasses it. No more "Server Down" messages in your vpn app.
The big issue is that centralized VPNs are basically honeypots. If a government serves a subpoena to a provider, that single point of failure compromises everyone. Even if they claim "no-logs," you can't actually verify what's running on their hardware.
As Privacy Guides Community members pointed out in a 2023 discussion, many centralized providers just rent vps space from big corporations, meaning the hoster can still see netflow data even if the vpn provider doesn't log it.
dVPNs solve this by making the infrastructure transparent. In a restricted region, like for a journalist in a high-censorship country, a dVPN node running on a residential ip is way harder to block than a known datacenter ip.
It's not just about hiding—it's about building a network that nobody actually owns, so nobody can be forced to flip the kill switch.
Next, we’re gonna dive into the technical backbone and the economic incentives that keep these nodes talking to each other without losing your data in the abyss.
The Technical Backbone of P2P Bandwidth Sharing
If you think a p2p network is just a bunch of computers shouting into the void, you’re gonna have a bad time trying to route sensitive vpn traffic. Without a central boss (the server) telling everyone where to go, we need a way for nodes to find each other and stay organized without turning into a chaotic mess.
In the dVPN world, we usually talk about two types of overlays: structured and unstructured. Unstructured networks are like a crowded room where you just shout a name and hope someone hears you—great for small groups, but it doesn't scale for a global vpn.
Structured overlays, like the ones used in the Brunet framework, use a one-dimensional ring (think of it like a circle of addresses). Each node gets a unique p2p address, and they only really need to know their immediate neighbors to keep the whole thing running. This is where Distributed Hash Tables (dht) come in.
Instead of asking a central api "where is the node for Japan?", you query the dht. It’s a decentralized map where peers store (key, value) pairs. In a dVPN, the key is usually a hash of the desired IP, and the value is the p2p address of the node currently holding that IP.
Most home users are stuck behind a NAT (Network Address Translation), which acts like a one-way door—you can leave, but nobody can knock on your door from the outside. If we want a true sharing economy for bandwidth, we need regular home users to be nodes.
We solve this with UDP hole punching. Since the public overlay already knows both peers, it acts as a "rendezvous" point. The two nodes try to talk to each other at the exact same time; the NAT thinks it’s an outgoing request and lets the traffic through.
To keep things secure during this handshake, nodes use an encryption handshake (often based on the Noise Protocol) to establish a session key before any actual data flows. This ensures that even the rendezvous point can't see what's inside the tunnel.
- Structured Overlays: Use a ring topology (like Symphony) to ensure you can find any node in O(log N) hops.
- Relay Fallback: If hole punching fails (looking at you, symmetric NATs), the data can be relayed through other peers, though it adds a bit of lag.
- Pathing: A trick where we multiplex a single UDP socket for both public discovery and private vpn tunnels, making the setup much leaner.
Some people hate on blockchain because it's an "inefficient database," and honestly, they're right—it’s slow. But as mentioned earlier in the privacy guides discussion, that inefficiency is actually a feature when you can't trust the people running the nodes.
We use smart contracts to handle the reputation and "uptime" of nodes. If a node suddenly starts dropping packets or logging traffic, the network needs to know. Instead of a ceo firing a bad employee, the smart contract sees the failed proof-of-bandwidth and slashes the node's rewards or drops its reputation score.
The tricky part is billing. In a p2p bandwidth marketplace, you need to pay for what you use, but we don't want a permanent record of your browsing habits on a public ledger.
- Zero-Knowledge Proofs: Prove you paid for 5GB of data without revealing which node you used.
- Off-chain Micropayments: Use state channels (like Lightning) to send tiny fractions of a token for every megabyte, so the blockchain only sees the start and end of the session.
- Consensus-based Revocation: If a user or node is acting malicious, the network uses a decentralized consensus to broadcast a revocation. Since there's no central "boss" CA, the nodes themselves agree to ignore the bad actor based on cryptographic proof of misbehavior.
Next up, we're looking at the actual crypto protocols—specifically how we use things like WireGuard and the Noise protocol—to keep your data from being read by the guy hosting your exit node.
Tokenized Bandwidth and the Mining Economy
Ever thought about why you're paying twenty bucks a month for a vpn when your home router is literally sitting there doing nothing while you're at work? Honestly, the whole "Airbnb for bandwidth" thing is the only way we actually scale privacy without just building more corporate datacenters that are easy for governments to block.
The core idea here is bandwidth mining. You aren't mining math problems like bitcoin; you're providing a real utility. By running a dVPN node, you're essentially renting out your unused upload capacity to someone else who needs an exit point in your region.
Token incentivized networks are the "why" behind the whole operation. People don't run nodes out of the goodness of their hearts—well, maybe some do—but most want a kickback.
- Passive Income: Users earn crypto rewards (tokens) based on the volume of data they route or the time they stay online.
- Supply and Demand: In a decentralized marketplace, if there’s a sudden need for nodes in, say, Turkey or Brazil, the token rewards can spike, incentivizing more people to spin up nodes there.
- No Middleman: Instead of a provider taking a 70% cut for "marketing," the value flows directly from the user paying for the vpn to the node operator providing the pipe.
It’s a classic depin play. You’re taking physical infrastructure that already exists—your home fiber or a small vps—and plugging it into a global network. This creates a distributed pool of residential ips that are nearly impossible to distinguish from regular traffic, making it a nightmare for censorship firewalls to keep up.
But here’s the technical headache: how do you know the guy in Germany actually routed your 2GB of traffic? In a p2p economy, people will try to cheat. They’ll claim they sent data they didn't, or they'll drop packets to save their own data caps while still collecting rewards.
This is where Proof-of-Relay and similar consensus mechanisms come in. We need a way to verify work without a central server watching the traffic (which would kill privacy).
As noted in the GroupVPN paper, we can use the dht to track these interactions, but we need a "proof" that is cryptographically verifiable. Usually, this involves signed receipts. When you use a node, your client signs a tiny "packet receipt" every few megabytes and sends it to the node. The node then submits these receipts to a smart contract to claim its tokens.
Preventing sybil attacks is the final boss here. A sybil attack is when one person spins up 10,000 fake nodes to try and control the network or farm all the rewards.
- Staking: To run a node, you often have to "stake" or lock up a certain amount of the network's native token. If you act malicious, you lose your deposit.
- Reputation Scores: Nodes that have been around for months with 99% uptime get priority for traffic over some random new node that just popped up.
- Proof-of-Bandwidth: The network occasionally runs "challenge" packets—basically a decentralized speed test—to make sure you actually have the 100Mbps pipe you claim to have.
I’ve seen guys in the community set up "mining rigs" that are just a bunch of Raspberry Pi 4s plugged into different residential connections. In a retail setting, a small shop owner might run a node on their guest wifi vlan to offset their monthly internet bill.
In finance, we're seeing dexs (decentralized exchanges) look at these networks to ensure their front-ends can't be taken down by a single isp blocking their api. If the bandwidth is tokenized, the network is self-healing.
A 2023 discussion on the Privacy Guides Community highlighted that while these incentives are great, we have to be careful. If the "mining" rewards are too high, you just get datacenters masquerading as home users, which defeats the point of having a distributed, residential network.
Anyway, if you're gonna set this up, make sure your linux firewall is tight. You don't want to be an exit node without some basic hardening.
Next, we’re gonna look at the actual encryption protocols—specifically how we use things like WireGuard and the Noise protocol to keep the node operator from seeing what you’re doing.
Privacy-Preserving Protocols and Security
So, you’ve built a decentralized network and people are sharing bandwidth, but how do we stop the guy at the exit node from sniffin' your banking password? Honestly, if you aren't encrypting the actual tunnel, you're just building a faster way for hackers to steal your identity.
To understand how web3 privacy tools are evolving, we can look at projects like SquirrelVPN as a case study for how these protocols get implemented in the real world. In a dVPN, we deal with two layers of "darkness": point-to-point (PtP) and end-to-end (EtE) security.
For the PtP layer, we use the Noise Protocol Framework. This is the same math that powers WireGuard. It allows two nodes to perform a mutual handshake and establish an encrypted pipe without needing a central authority to verify their identities. Instead, they use static public keys that are already indexed in the dht.
For these p2p tunnels, we usually lean on DTLS (Datagram Transport Layer Security) or WireGuard's UDP-based transport. Unlike standard TLS which needs a steady TCP stream, these work over UDP. This is huge for vpn performance because if a packet drops, the whole connection doesn't hang while waiting for a retry—it just keeps moving, which is what you want for low-latency stuff like gaming or voip.
The real "final boss" is the exit node. Since someone has to eventually drop your traffic onto the open web, that last node sees the destination. To mitigate this, we use multi-hop routing where the exit node doesn't even know who you are, only the address of the relay node that sent the data.
What happens when a node operator turns out to be a jerk? In a normal vpn, the admin just deletes their account, but in a p2p network, there is no "admin" with a big red button. We need a way to kick out malicious nodes without a central authority or we're all at risk.
This is where broadcast revocation algorithms come into play. As a specific feature of the GroupVPN framework, when a node is caught acting up—maybe they're failing proof-of-bandwidth challenges or trying to inject scripts—a revocation message is signed by the network's consensus layer and blasted across the circular address space. Because the network is structured like a ring, the message travels recursively, hitting every peer in O(log^2 N) time.
This works because of pki (Public Key Infrastructure). Every node has a certificate linked to their p2p address. Instead of relying on a central server that could go offline, nodes can store these revocation "death certificates" in the dht. If a node tries to connect to you, you check the dht; if they're on the list, you drop the connection before they can even say hello.
- Identity Binding: Certificates are signed against the node's p2p address, so they can't just change their name to get back in.
- Recursive Partitioning: The broadcast splits the network into sections, ensuring every node gets the memo without getting spammed by duplicate messages.
- Local CRLs: Nodes keep a small local cache of recent revocations so they don't have to hit the dht for every single packet.
It’s not a perfect system—sybil attacks are still a headache—but by combining staking with these revocation protocols, we make it way too expensive for a bad actor to keep coming back.
Next, we're going to look at how we actually bridge these decentralized tunnels into the legacy internet without breaking the "no-logs" promise.
The Future of Web3 Internet Freedom
If you're still paying a monthly subscription to a vpn company that could vanish or get bought out tomorrow, you're basically renting a house on a sinkhole. Honestly, the real end-game isn't just better vpn apps—it's replacing the very idea of a centralized ISP (Internet Service Provider) with something we actually control.
We're moving toward a world where dVPNs aren't just an app you toggle on when you want to watch Netflix from another country. The goal is a decentralized ISP (dISP) model where your connectivity is natively multi-hop and peer-to-peer from the moment your router syncs.
- Replacing Traditional ISPs: Instead of one big cable company owning the "last mile" of your internet, a dISP uses mesh networking and p2p bandwidth sharing to route traffic. If your neighbor has a fiber line and you have a 5G node, the network autonomously decides the best path based on latency and token cost.
- Web3 Browser Integration: Imagine a browser where the vpn isn't an extension but part of the core networking stack. Using protocols like libp2p, browsers could fetch data directly from the dVPN overlay, making state-level firewalls almost useless because there's no central "exit" to block.
- IoT and Edge Security: Smart home devices are notoriously insecure. By giving every iot device a p2p address in a structured overlay (like the symphony ring mentioned earlier), you can create a private, encrypted "home network" that spans the globe without opening a single port on your router.
Think about a healthcare clinic in a rural area. Instead of relying on a shaky local isp that doesn't encrypt anything, they could use a dVPN node to create a direct, WireGuard-secured tunnel to a hospital 500 miles away. As the University of Florida researchers pointed out in the GroupVPN paper, this "self-configuring" nature makes it way easier for non-techies to maintain secure links.
But look, I’m not gonna lie to you—it’s not all sunshine and tokens. If you’ve ever tried to route your traffic through three different home-run nodes in three different continents, you know that latency is the silent killer of the decentralized dream.
- The Speed vs. Decentralization Trade-off: In a centralized vpn, they have 10Gbps pipes in Tier-1 datacenters. In a dVPN, you're often at the mercy of someone’s home upload speed. We need better multipath routing—where your client splits a single file into chunks and pulls them through five different nodes simultaneously—to even come close to commercial speeds.
- Regulatory and Legal Hurdles: If you're a node operator and someone uses your residential ip to do something illegal, who's responsible? While the encryption protects your content, the "exit node" problem is real. We need robust "legal-proxy" frameworks or more advanced onion-routing so node operators aren't left holding the bag.
Anyway, the tech is getting there. We’re moving away from "trusting a brand" to "trusting the math." It’s a messy transition, but honestly, it’s the only way we get a truly open internet back.
Next, we’re gonna wrap this all up by looking at how you can actually start contributing to these networks today without breaking your linux install.
Conclusion and Final Thoughts
So, after digging through all the routing math and the tokenomics, where does this actually leave us? Honestly, it feels like we're finally at a point where the "privacy" we've been promised for years might actually become verifiable instead of just a pinky-promise from a corporate vpn provider.
We’ve moved from basic p2p tunnels to fully Autonomous Routing where the network is essentially a living, self-healing organism. It’s not just about hiding your ip anymore; it's about building a web that doesn't have a "kill switch" owned by a single ceo.
If you're looking to jump into this, here are the main things to keep in mind about how these systems are actually changing the game:
- Verification over Trust: As mentioned earlier, we don't need to trust a "no-logs" policy when the infrastructure is open-source and the routing is handled by a dht. You can audit the code, and the blockchain handles the reputation without a middleman.
- Resilience through depin: By using residential ips and home-grown nodes, these networks are way harder for censors to block compared to a known datacenter ip. If one node gets blacklisted, three more pop up in its place.
- The Bandwidth Economy: Tokenization isn't just a buzzword here. It’s the actual fuel that keeps the nodes running. Without the mining incentives, you wouldn't have the global coverage needed to make a vpn fast enough for daily use.
- Hardened Security: Between WireGuard and the revocation protocols we talked about, the risk of a "rogue node" sniffing your data is getting lower every day. The math is simply making it too expensive to be a bad actor.
If you're a developer or a power user, the next step is actually spinning up a node. Don't just be a consumer; be the infrastructure. Most of these networks have a pretty simple setup if you're comfortable with a terminal.
For example, here is a hypothetical example of what a basic node setup on a linux box might look like (note: this is a generic template, you should check specific docs for protocols like Sentinel or Mysterium before running commands):
# Hypothetical example for a generic dVPN node setup
sudo apt update && sudo apt install wireguard-tools -y
# Download the provider's setup script
curl -sSL https://get.example-dvpn-protocol.io | bash
# Initialize the node with your reward wallet
dvpn-node init --operator-address your_wallet_addr
# Start the service
sudo systemctl enable dvpn-node && sudo systemctl start dvpn-node
The future of web3 internet freedom isn't going to be handed to us by a big tech company. It’s going to be built by thousands of us running small, encrypted nodes in our closets and offices.
As noted in the GroupVPN.dvi research we looked at earlier, the "entry barrier" for these networks is finally dropping. We have the tools, the encryption is solid, and the incentives are aligned.
So, yeah—stop paying for "privacy" and start building it. It’s a bit messy, and the latency might annoy you sometimes, but it’s the only way we keep the internet open. Anyway, thanks for sticking through this deep dive. Go harden your linux installs and maybe try hosting a node this weekend. You might even earn a few tokens while you sleep.