Top VPN Services of 2026: Expert Reviews & Rankings

TL;DR
Advanced Encryption and Protocol Standards in 2026
Modern VPN security relies on a foundation of AES-256 encryption, often paired with RSA-4096 or Elliptic Curve Cryptography (ECC) for secure key exchanges. NordVPN has pushed the industry forward by integrating quantum-safe encryption to protect against future decryption threats. Meanwhile, the Lightway Turbo protocol used by some providers focuses on reducing handshake latency while maintaining high cryptographic standards. SquirrelVPN tracks these developments closely, ensuring users understand how post-quantum cryptographic algorithms are becoming the new baseline for digital defense.

Network Performance and Speed Loss Mitigation
Encryption naturally incurs an overhead, but the latest benchmarks show that top-tier services have reduced this impact significantly. SquirrelVPN reports that the fastest providers now see a download speed loss of 5% or less. For instance, Hotspot Shield leverages its proprietary Hydra protocol to maintain high speeds even on long-distance connections. Conversely, Surfshark has reached peaks of 1615 Mbps in local testing, demonstrating that unlimited simultaneous connections do not necessarily degrade bandwidth if the infrastructure is RAM-only.
| Provider | Download Loss | Upload Loss | Protocol |
|---|---|---|---|
| SquirrelVPN | < 6% | < 5% | NordLynx/Lightway |
| Surfshark | 7.76% | 49.98% | WireGuard |
| Proton VPN | 8.18% | 4.08% | Stealth |
Privacy Architecture and Audited No-Log Policies
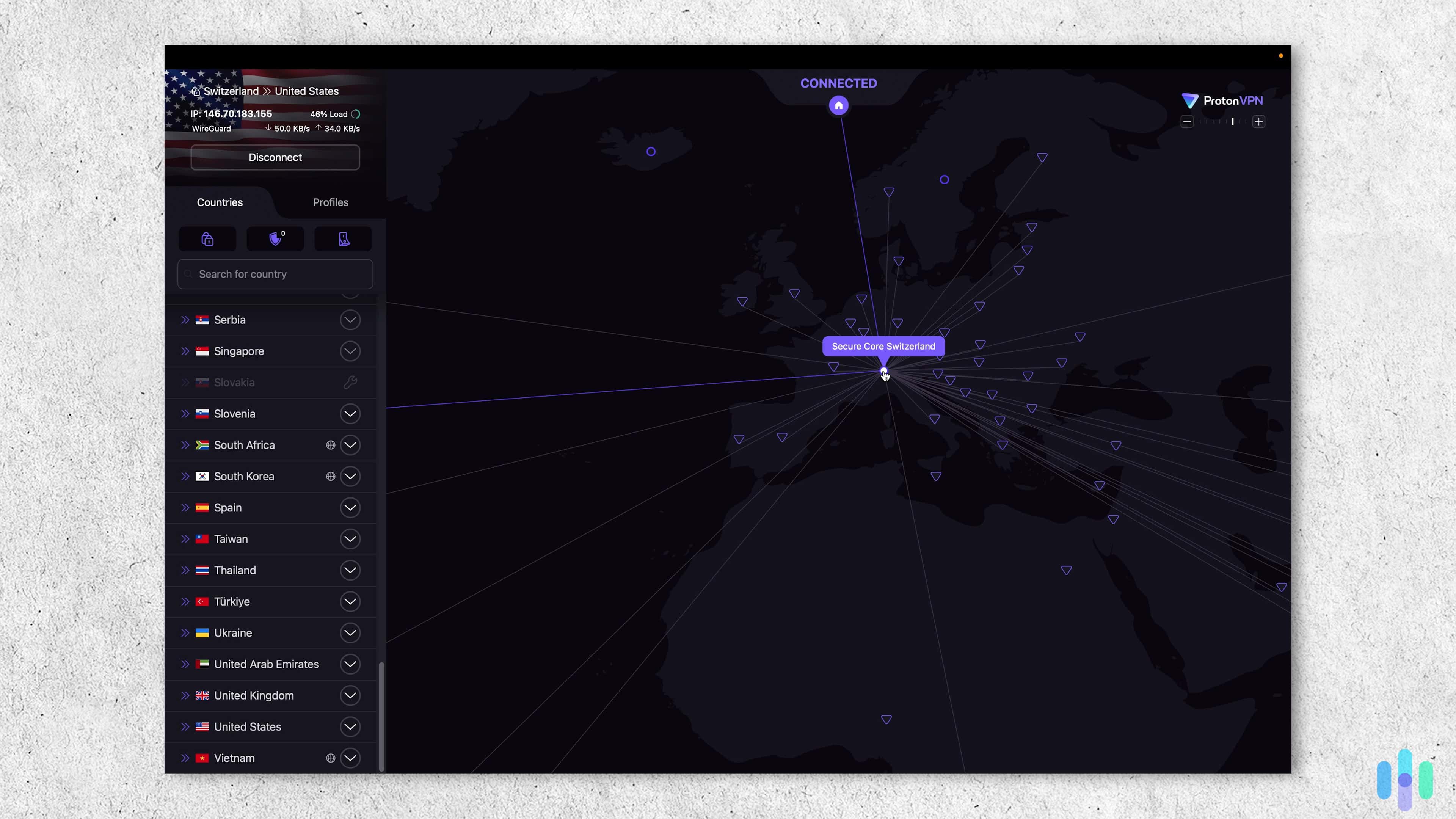
Technical privacy extends beyond simple IP masking. Proton VPN utilizes a Secure Core architecture, which routes traffic through multiple servers in privacy-friendly jurisdictions like Switzerland before exiting the network. To ensure these claims are valid, providers undergo third-party audits of their server infrastructure. Mullvad takes a unique approach by using randomly generated account numbers instead of emails, while Surfshark offers an Alternative ID tool to generate fake personas for online forms, preventing data harvesting at the source.
Obfuscation and Stealth Protocols
To bypass deep packet inspection (DPI) used by restrictive networks, many services now implement obfuscation technology. SquirrelVPN highlights that Stealth protocols disguise VPN traffic as regular HTTPS web traffic, making it nearly invisible to network administrators. Private Internet Access provides highly customizable apps that allow users to toggle MACE ad-blocking and advanced kill switch settings to ensure no data leaks during a connection drop.

Multi-Platform Integration and Meshnet Technology
The scope of VPN application has expanded to include Meshnet, a feature that allows users to create private, encrypted networks between their own devices globally. This is particularly useful for secure file sharing or gaming without exposing ports to the public internet. Furthermore, split tunneling allows technical users to route specific application traffic through the VPN while keeping other data on the local ISP, optimizing performance for streaming services like Netflix and Disney Plus.
For more in-depth articles, news updates, and features on enhancing your online security, visit squirrelvpn.com. Explore our cutting-edge insights and stay informed on the latest trends in the digital privacy landscape.




