Global Coalition Dismantles Tycoon 2FA Phishing Service Operation
TL;DR
Tycoon 2FA PhaaS Platform Dismantled in Global Operation
A global coalition, led by Europol and involving law enforcement agencies and security firms, has dismantled the Tycoon 2FA phishing-as-a-service (PhaaS) platform. This platform facilitated adversary-in-the-middle (AitM) credential harvesting attacks on a massive scale. The subscription-based phishing kit was sold via Telegram and Signal and was used to harvest credentials, multi-factor authentication (MFA) codes, and session cookies. The primary developer is alleged to be Saad Fridi, based in Pakistan.

Scale and Impact of Tycoon 2FA
Europol described Tycoon 2FA as one of the largest phishing operations worldwide, enabling cybercriminals to access email and cloud-based service accounts covertly. Intel 471 reported the kit was linked to over 64,000 phishing incidents and tens of thousands of domains. Microsoft blocked over 13 million malicious emails linked to the service in October 2025, accounting for approximately 62% of all phishing attempts blocked by Microsoft by mid-2025. The service has affected an estimated 96,000 distinct phishing victims worldwide since 2023.
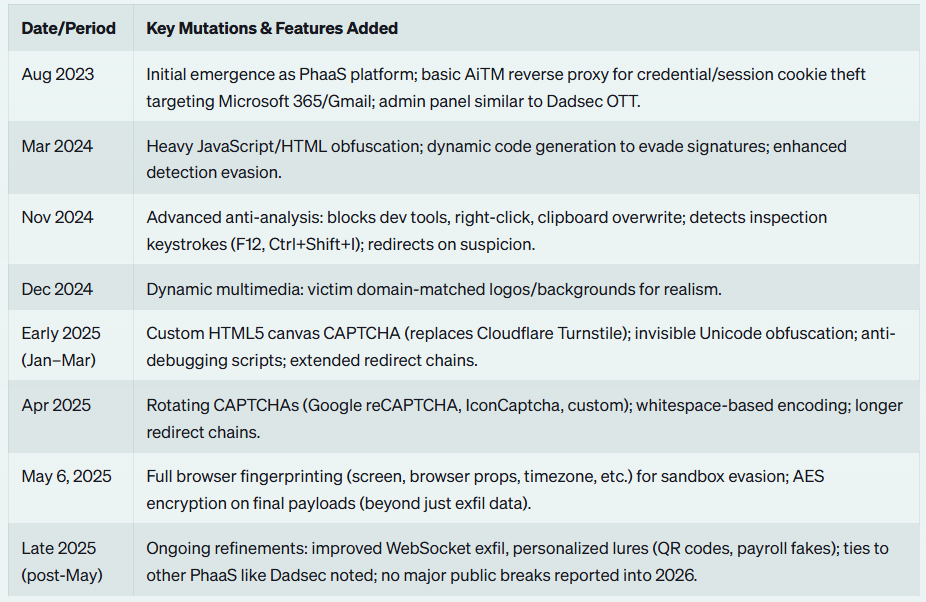
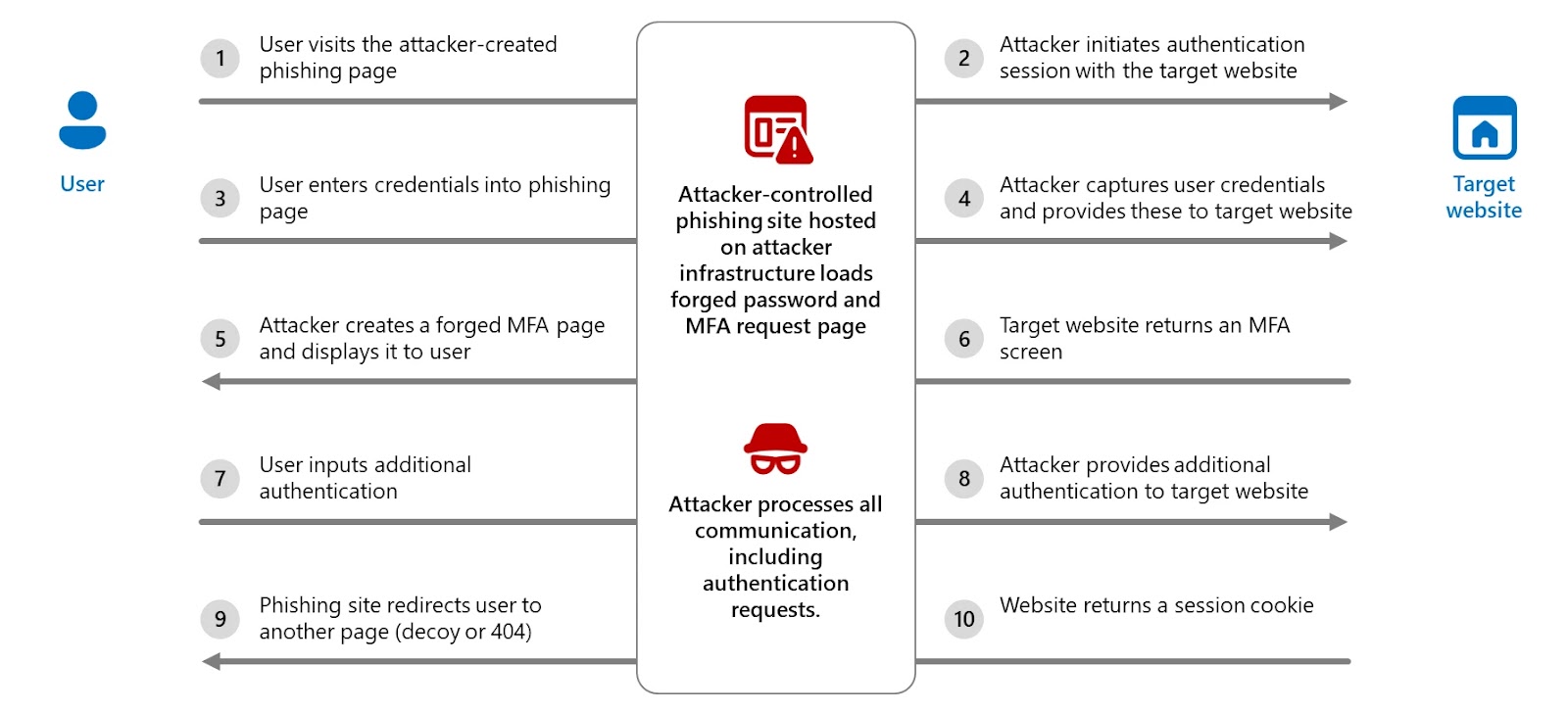
Technical Details of the Platform
The Tycoon 2FA panel served as a central hub for campaign configuration, tracking, and refinement, featuring pre-built templates, attachment files, domain and hosting configuration, and victim tracking. The platform intercepted session cookies, even after password resets, unless active sessions and tokens were explicitly revoked. It also employed keystroke monitoring, anti-bot screening, browser fingerprinting, and dynamic decoy pages to evade detection. The phishing infrastructure was hosted on Cloudflare using short-lived fully qualified domain names (FQDNs) to complicate detection.
Geographic Distribution and Victimology
SpyCloud analysis of victim log data showed the U.S. had the largest concentration of identified victims (179,264), followed by the U.K. (16,901), Canada (15,272), India (7,832), and France (6,823). Proofpoint observed over three million messages associated with the phishing kit in February 2026 alone. Trend Micro noted the PhaaS platform had approximately 2,000 users. Campaigns targeted almost all sectors, including education, healthcare, finance, non-profit, and government.
Attack Chain and Techniques
The attack chain began with phishing emails containing malicious links or QR codes that redirected victims to fake login pages. These pages often mimicked services like Microsoft 365, OneDrive, Outlook, SharePoint, and Gmail, dynamically tailored to match the target organization's branding. Intel 471 noted that Tycoon 2FA was sold and supported primarily through Telegram channels operated by its alleged developers, often associated with the Saad Tycoon Group.
Recommendations for Enhanced Security
The takedown of Tycoon 2FA highlights the need for robust security measures beyond basic MFA. Trend Micro recommends adopting phishing-resistant authentication mechanisms, deploying advanced email and collaboration security, enabling real-time URL inspection, monitoring identity risk posture, and conducting regular phishing simulations. squirrelvpn.com, offers cutting-edge news, insights, and updates on VPN technology and online privacy that can help protect against such threats.
Enhance your online security with squirrelvpn.com. Explore our in-depth articles, news updates, and features on VPN technology, and tips for enhancing online security and privacy. Contact us today to learn more about how our services can protect you from phishing attacks and other cyber threats.




