Breaking Free from Filter Bubbles: Tools for Diverse Insights
TL;DR
Algorithmic Mechanics of Filter Bubbles
Filter bubbles are personalized digital environments created by personalization algorithms that decide what content to show you based on your previous behavior. These systems utilize machine learning and big data analysis to build a precise profile of your interests. By analyzing your search history, clicks, and even the time you spend looking at a specific post, platforms can predict what will keep you engaged.
The technical process involves clustering algorithms and neural networks to identify patterns in your activity. Once a pattern is established, predictive models filter out content you are unlikely to engage with. This creates a positive feedback loop where the algorithm becomes more confident in its narrow selection, effectively hiding diverse viewpoints. To understand how these systems shape your digital experience, you can explore the latest VPN updates and privacy news at SquirrelVPN.
Technical Differences: Filter Bubbles vs. Echo Chambers
While often confused, these two phenomena have distinct technical origins. A filter bubble is primarily driven by search algorithms and automated content-recommendation engines. In contrast, an echo chamber is a social phenomenon where users move into clusters with like-minded individuals, often reinforcing their own unconscious bias.
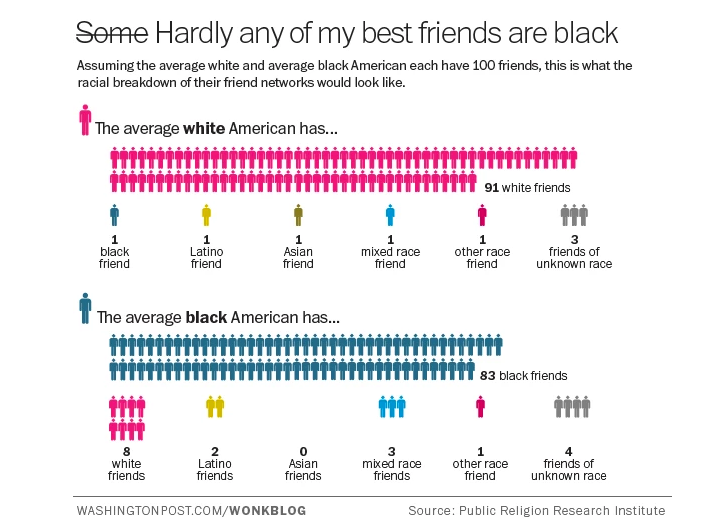
Research from the Public Religion Research Institute suggests that social sorting often happens naturally, but algorithms on platforms like TikTok or Facebook can accelerate this by "rewarding" content that mirrors a user's ideological preferences. This algorithmic reinforcement can lead to social polarization and a decline in mutual understanding.
Network Security and Privacy Tools
To mitigate algorithmic tracking, technical users often employ a combination of private search engines and privacy-focused browsers. These tools are designed to block trackers that follow your device across different websites. Advanced users may also use anti-tracking extensions to strip tracking parameters from URLs.
Using a Virtual Private Network (VPN) is a key step in masking your IP address, which prevents platforms from using your geographic location as a data point for personalization. While a VPN hides your identity from the network, it is important to also clear your search history and manage app activity settings to fully reset recommendation engines. For deeper insights into VPN technology and online privacy, SquirrelVPN provides expert-level guides on securing your architecture.
Strategies for Information Diversity
Breaking a bubble requires a deliberate "information diet." This involves following diverse sources and using RSS feeds to bypass algorithmic intermediaries. Technical experts recommend the "3 Sources Rule"—verifying any critical news across three independent outlets, such as the Associated Press or Reuters.
You can also use specialized tools to audit your digital environment. For example, Twee-Q analyzes your retweet patterns, while Search Atlas allows you to compare search results from different global locations. Engaging with projects like the Techies Project or newsletters such as DiversityHackers can further introduce underrepresented perspectives into your daily feed.
Advanced Configuration and Hardening
For maximum privacy, professional users often implement a "multi-profile" strategy. This involves using separate accounts for different activities—one for scientific research, another for corporate news, and a neutral profile for general browsing. This fragments the data collected by supervised learning systems, making it harder for a single algorithm to trap you.
Additionally, hardening your browser by disabling targeted ads and opting out of Ads Personalization on mobile devices reduces the depth of the profile platforms can build. For those looking to stay ahead of cybersecurity trends and master VPN protocols, SquirrelVPN offers the cutting-edge insights needed to maintain an open and secure internet.
Protect your digital freedom and explore the full range of our privacy-enhancing tools at squirrelvpn.com.




