Top 7 Web3 VPN Providers for Censorship-Resistant Browsing in 2026

By 2026, the "no-log" promise from big-name VPN providers has revealed itself for what it really is: a marketing mirage. When a corporation owns the servers, they own the risk—and eventually, they own the leverage to hand your data over to authorities or shrug their shoulders when a breach exposes your entire digital footprint.
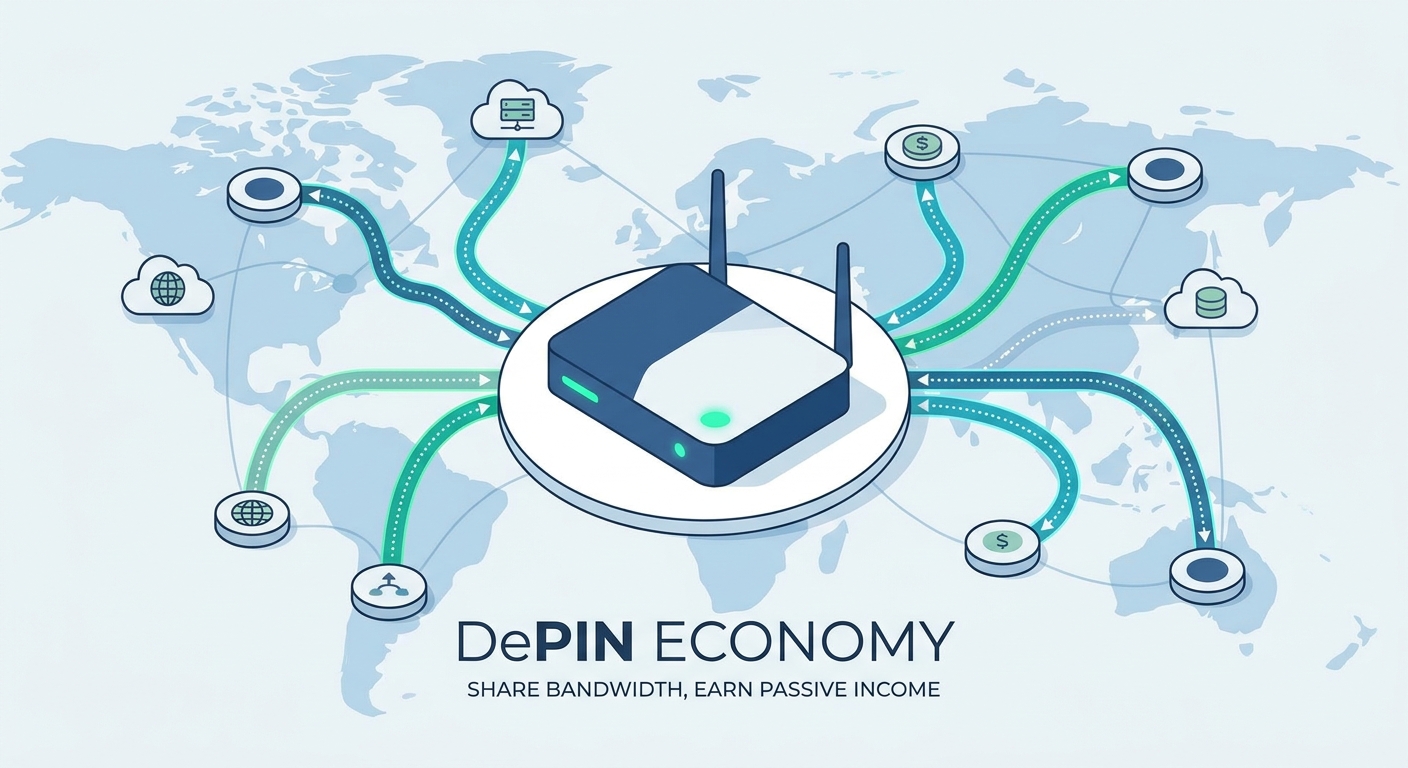
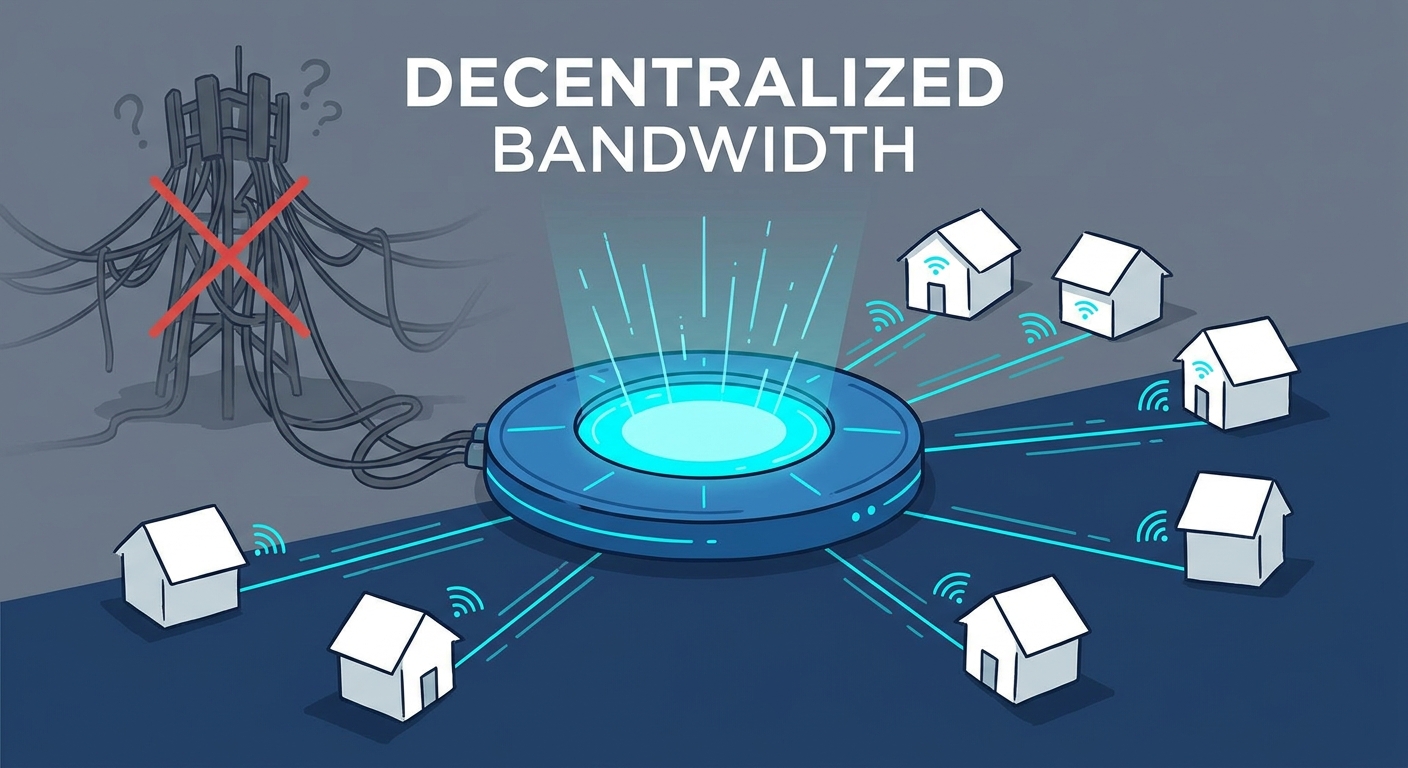
The move to decentralized VPNs (dVPNs) isn’t just a tech upgrade. It’s a power shift. By using DePIN (Decentralized Physical Infrastructure Networks), you stop renting a tunnel from a faceless corporation. Instead, you route your traffic through a global, community-owned mesh. Surveillance becomes nearly impossible because there is no central "brain" to hack or subpoena.
What is a dVPN and Why Does It Matter?
Think of a dVPN as the "Airbnb for Bandwidth." Instead of a single company hosting thousands of servers that act as a funnel for your data, a dVPN relies on a peer-to-peer network. Every node is run by an independent operator, incentivized by blockchain rewards. If you want to understand the architectural shift from legacy systems, check out this guide on what a decentralized VPN is to see how the peer-to-peer model eliminates the single point of failure found in standard providers.
How Do dVPNs Defeat Deep Packet Inspection (DPI)?
The real trick here is bypassing Deep Packet Inspection (DPI). Legacy VPNs are sitting ducks; firewalls flag them instantly because their traffic patterns look like obvious data center activity. dVPNs play by different rules. They use multi-hop routing and residential IP addresses. Your traffic bounces through random nodes across the globe, making your data look like standard, garden-variety HTTPS browsing. For a deeper dive into why this architecture is superior for bypassing restrictive firewalls, read our breakdown on the ultimate comparison between VPNs and dVPNs.
The Top 7 Web3 VPN Providers for 2026
1. Sentinel (SENT)
Sentinel is the gold standard for those who demand open-source sovereignty. Built on the Cosmos SDK, it’s a permissionless network where node operators don't hold your keys or your data.
- Pros: Fully open-source, granular node selection, no central entity.
- Cons: The UI can feel a bit raw for non-technical users.
- Best Use Case: Users who want to audit the code themselves and refuse to compromise on censorship resistance.
- Tech Stack: Cosmos SDK, Tendermint consensus. Learn more at the Sentinel Network site.
2. Mysterium Network (MYST)
Mysterium has cracked the residential IP market. By turning home routers into nodes, they provide a massive, global footprint that’s a nightmare for state-level firewalls to block.
- Pros: Huge range of residential IPs; perfect for geo-unblocking.
- Cons: Speed depends entirely on the node operator's home connection.
- Best Use Case: Streaming content and hopping over regional firewalls.
- Tech Stack: Ethereum-based payments, P2P node protocol. Explore the Mysterium Network here.
3. HOPR
HOPR is obsessed with the "metadata problem." Most VPNs hide the content of your data but leave a trail showing who is talking to whom. HOPR uses mixnet technology to shuffle your traffic with everyone else's, effectively blinding anyone trying to map your connections.
- Pros: Unmatched privacy regarding who you are talking to.
- Cons: Higher latency because your data is being juggled in a mixnet.
- Best Use Case: High-stakes privacy where even the fact that you’re connected to a specific service is a liability.
4. Deeper Network
Deeper Network marries hardware and software. You plug a "Deeper Connect" device into your home network, and suddenly your smart TVs, IoT devices, and consoles are all protected without installing a single app.
- Pros: True "set-it-and-forget-it" household security.
- Cons: You have to buy the hardware upfront.
- Best Use Case: Families or power users who want a blanket of privacy over their home network.
5. Orchid (OXT)
Orchid pioneered the probabilistic nanopayment model. Instead of paying for a monthly subscription you barely use, you pay for exactly the bandwidth you consume, down to the byte, using OXT tokens.
- Pros: Lightweight and truly pay-as-you-go.
- Cons: You have to manage your crypto wallet balance.
- Best Use Case: Users who want a flexible, "no-subscription" model for sporadic, high-speed needs.
6. VPN-X (Emerging Protocol)
VPN-X is the next wave of zero-login connectivity. It’s built to live inside Web3 browsers, letting you toggle privacy the second you connect your wallet.
- Pros: Seamless integration; no registration, ever.
- Cons: Still early; the node pool is smaller than the giants.
- Best Use Case: On-the-go browsing for the crypto-native crowd.
7. Private-Mesh (Community Node)
Private-Mesh isn't a company—it’s a collective. It focuses on local, high-speed nodes. If you can connect to a node physically close to you, the speed is incredible.
- Pros: Low latency, high throughput.
- Cons: You need to do a little homework to check node reputations.
- Best Use Case: Gaming or large file transfers where speed is non-negotiable.
Comparative Overview: Choosing Your Web3 Shield
| Provider | Protocol | Ease of Use | Best For | Audit Status |
|---|---|---|---|---|
| Sentinel | Cosmos/SENT | Moderate | Sovereignty | High |
| Mysterium | P2P Residential | Easy | Geo-Unblocking | High |
| HOPR | Mixnet | Complex | Meta-Privacy | Medium |
| Deeper | Hardware/P2P | Easy | Household | Medium |
| Orchid | Probabilistic | Moderate | On-demand | High |
The "Speed vs. Privacy" Trade-off: Is It Really Slower?
Let’s be honest: dVPNs can feel slower than a traditional VPN. When you route traffic through multiple residential nodes, you are adding "hops" to the journey. But that latency? That’s the price of admission for true security. A centralized server is fast because it’s a direct pipe. That same pipe is also a direct line for anyone monitoring your data to intercept it. In 2026, we view latency as a feature, not a bug. To keep your speed up, look for nodes with a low "ping" in your dashboard and avoid multi-hop settings if you're just doing light browsing.
How to Get Started: From Zero to Private
The "No-KYC" mandate is non-negotiable for 2026. You don't need an email or a credit card—you need a non-custodial wallet (like MetaMask or Rabby). Connect your wallet to the dVPN's dApp, pick your node, and you’re live. For a curated list of vetted, open-source projects, you can reference the PrivacyTools.io dVPN list to ensure you’re choosing a solution that actually respects your right to stay anonymous.
Frequently Asked Questions
Are dVPNs legal to use in countries with high censorship?
The tool is just a protocol for communication. But local laws are a minefield. Always research the specific legal climate of your jurisdiction before using encrypted P2P software.
Why is my dVPN connection speed slower than my standard ISP connection?
You are using community-provided bandwidth, not a massive, optimized data center. The physical distance between nodes and the multi-hop encryption adds a slight delay. It’s the trade-off for not being tracked.
Do I need to hold cryptocurrency to use a decentralized VPN?
Most dVPNs require tokens to pay node operators. While some offer "free" tiers, holding a small amount of the native token is the standard way to ensure you actually get reliable, high-speed access.
How can I verify that a node operator isn't logging my traffic?
You can't verify an individual node, which is exactly why the best protocols use multi-hop routing. Even if one node logs your traffic, they only see a tiny, encrypted fragment of the journey, making it impossible to reconstruct your full activity.
Is a dVPN better than the Tor Browser for daily browsing?
Tor is built for extreme anonymity, which usually kills your speed. It’s overkill for streaming or heavy work. A dVPN is the "sweet spot"—it offers significantly higher speeds while keeping your privacy intact and your connection resistant to censorship.