What Your ISP Can See Without a VPN and How to Protect Privacy

TL;DR
ISP Visibility and Data Harvesting Mechanisms
Your Internet Service Provider (ISP) acts as the gateway to the digital world, handling every bit of data that passes through your connection. Without a VPN, your provider can see a significant amount of your online activity. If you use your ISP’s default Domain Name System (DNS) servers, they can log every domain request you make. Even when a website uses HTTPS encryption, your provider can still see the domain names you visit, such as your bank or a healthcare portal.
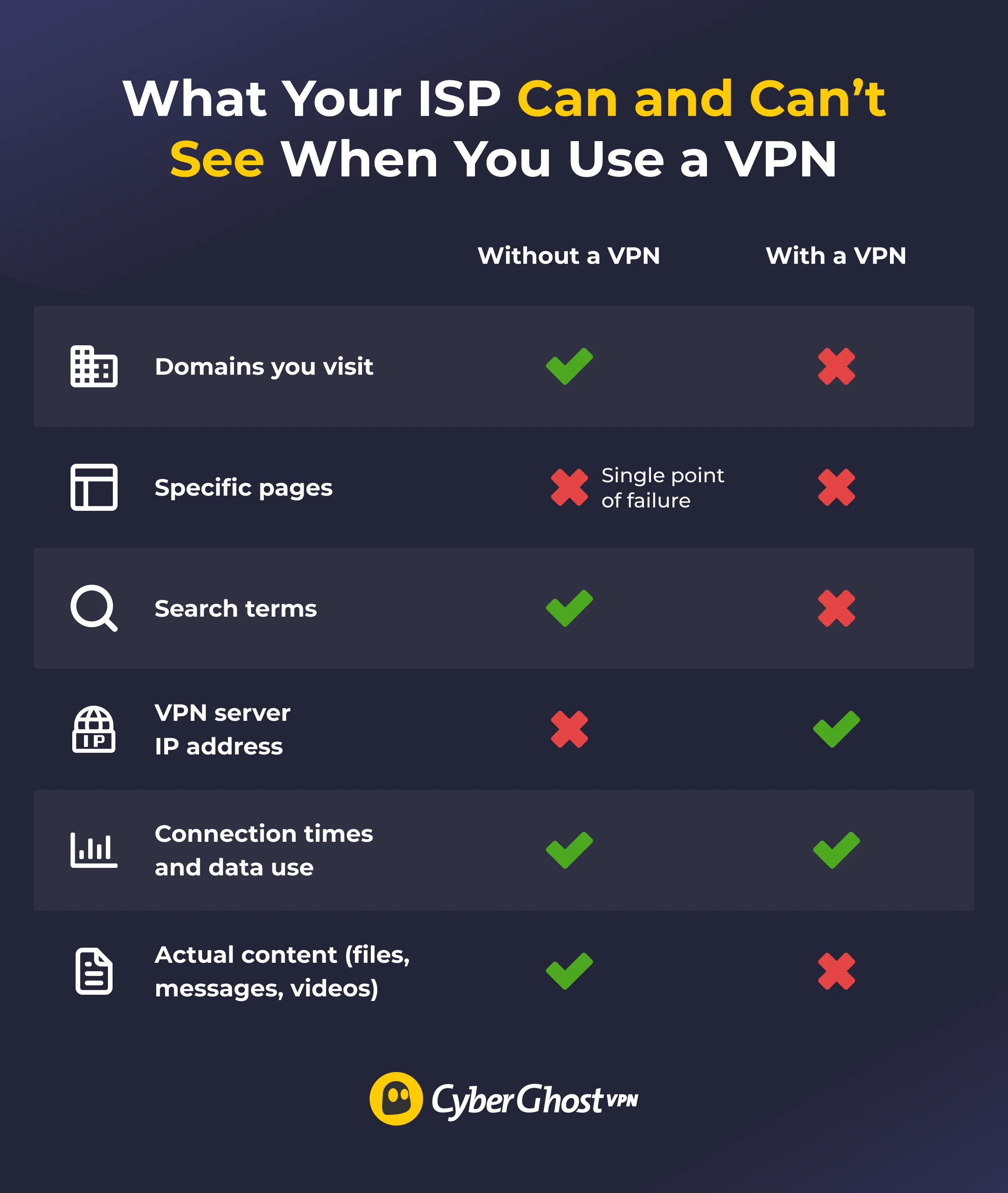
Beyond just the addresses, ISPs track connection metadata. This includes when you connect, how long you stay online, and your IP address and location. In some regions, providers are legally required to store this browsing history for set periods, making it accessible to authorities. Furthermore, some ISPs monetize this data by selling anonymized aggregate piles to third parties for advertising and data insights.
The Impact of Encryption on Provider Monitoring
When you switch on a VPN service, your traffic undergoes a fundamental shift. The software encrypts your data before it leaves your device, making it unreadable to the ISP. While the provider can no longer see the specific websites you visit or your search history, they can still identify that you are using an encrypted tunnel.

ISPs can detect VPN usage through several markers:
- Known IP Addresses: Providers often recognize the public IP ranges used by VPN servers.
- VPN Protocols: Specific protocols like WireGuard or OpenVPN use distinct ports and data patterns.
- Deep Packet Inspection (DPI): Advanced DPI analysis tools can detect the presence of an encrypted tunnel even if they cannot see the content inside.
Throttling, P2P, and Content Access
ISPs often use traffic shaping and throttling to manage network congestion. By identifying the type of service you are using—such as streaming platforms or gaming—they can artificially slow down your connection. A VPN can bypass this by hiding the nature of your traffic, though some ISPs may apply a blanket throttle to all VPN traffic if they detect it.
For users involved in torrenting or P2P file sharing, a VPN is a critical tool to obfuscate traffic. Without it, ISPs can easily identify P2P patterns and may send warnings regarding the download of dubiously sourced content. Additionally, location spoofing allows users to bypass regional licensing deals, though streaming services and VPN providers often engage in a "cat-and-mouse" game of IP blocking.
Technical Safeguards Against Data Leaks
Even with a VPN, privacy is not absolute unless specific technical features are active. A DNS leak occurs when your device sends requests outside the encrypted tunnel, allowing the ISP to see your destination. To prevent this, users should look for services that provide DNS leak protection and an automatic kill switch, which halts all internet traffic if the VPN connection drops.

Advanced users may also utilize obfuscated servers to make VPN traffic resemble standard HTTPS web browsing. This is particularly useful in jurisdictions with strict international privacy regulations or where VPN use is restricted. For comprehensive home protection, configuring a VPN directly on your router ensures every connected device is shielded, while split tunneling allows specific apps to bypass the VPN for better performance in gaming or local casting.
To stay ahead of evolving digital threats and maintain your right to digital sovereignty, explore the latest in encryption technology and privacy news at squirrelvpn.com.




