Comparing Tailscale and Raw WireGuard: Insights from a Month of Use
TL;DR
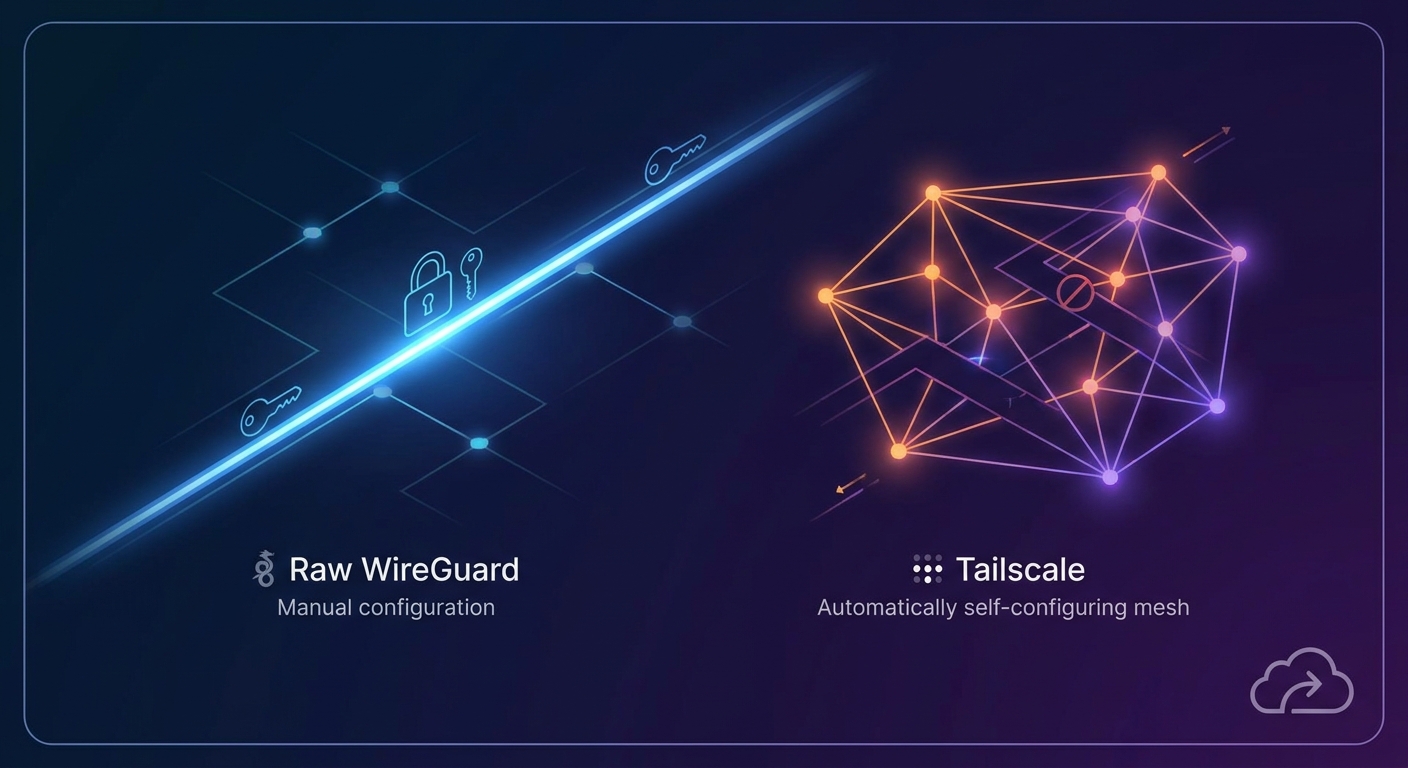
Protocol Mechanics: Raw WireGuard vs. Managed Mesh
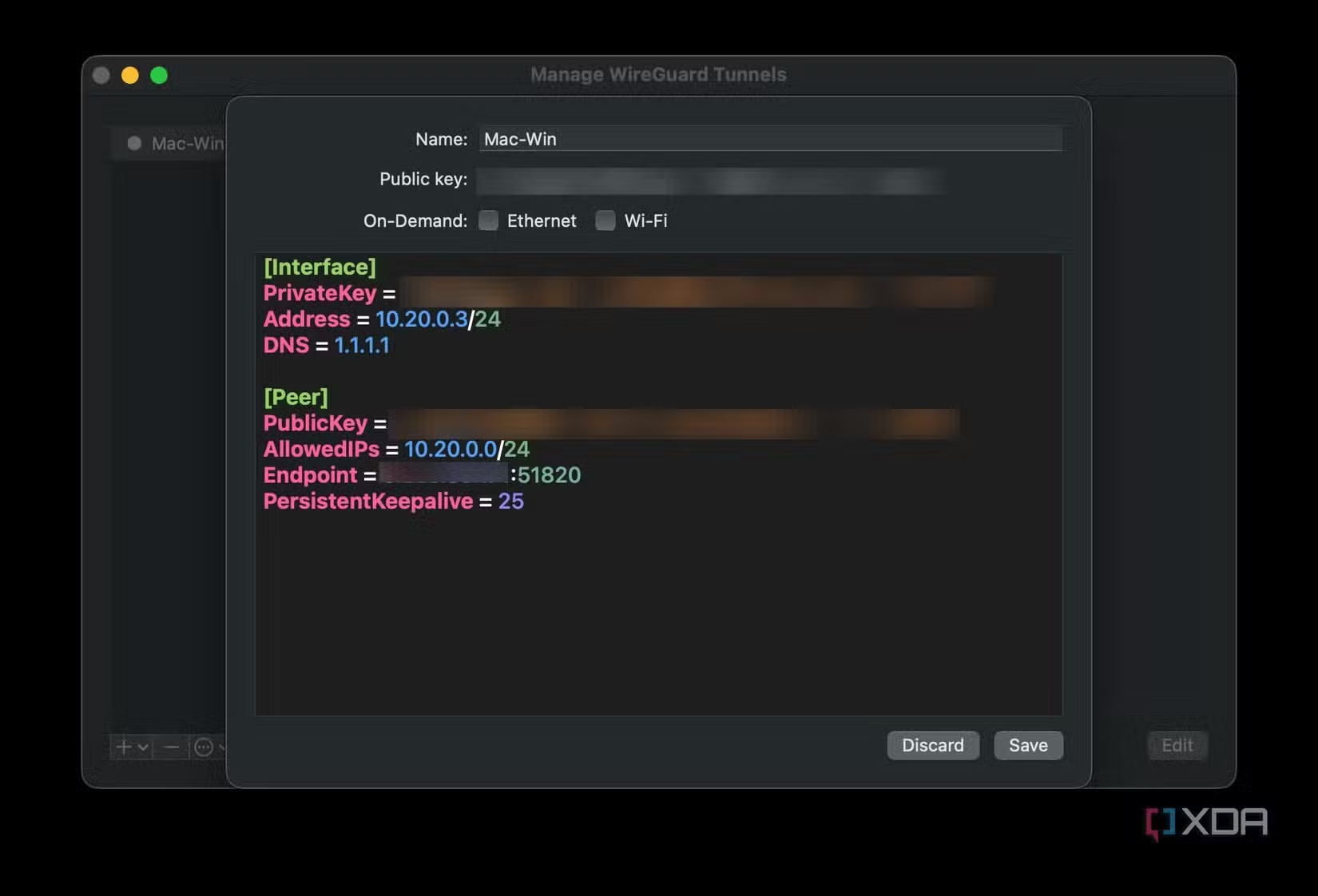
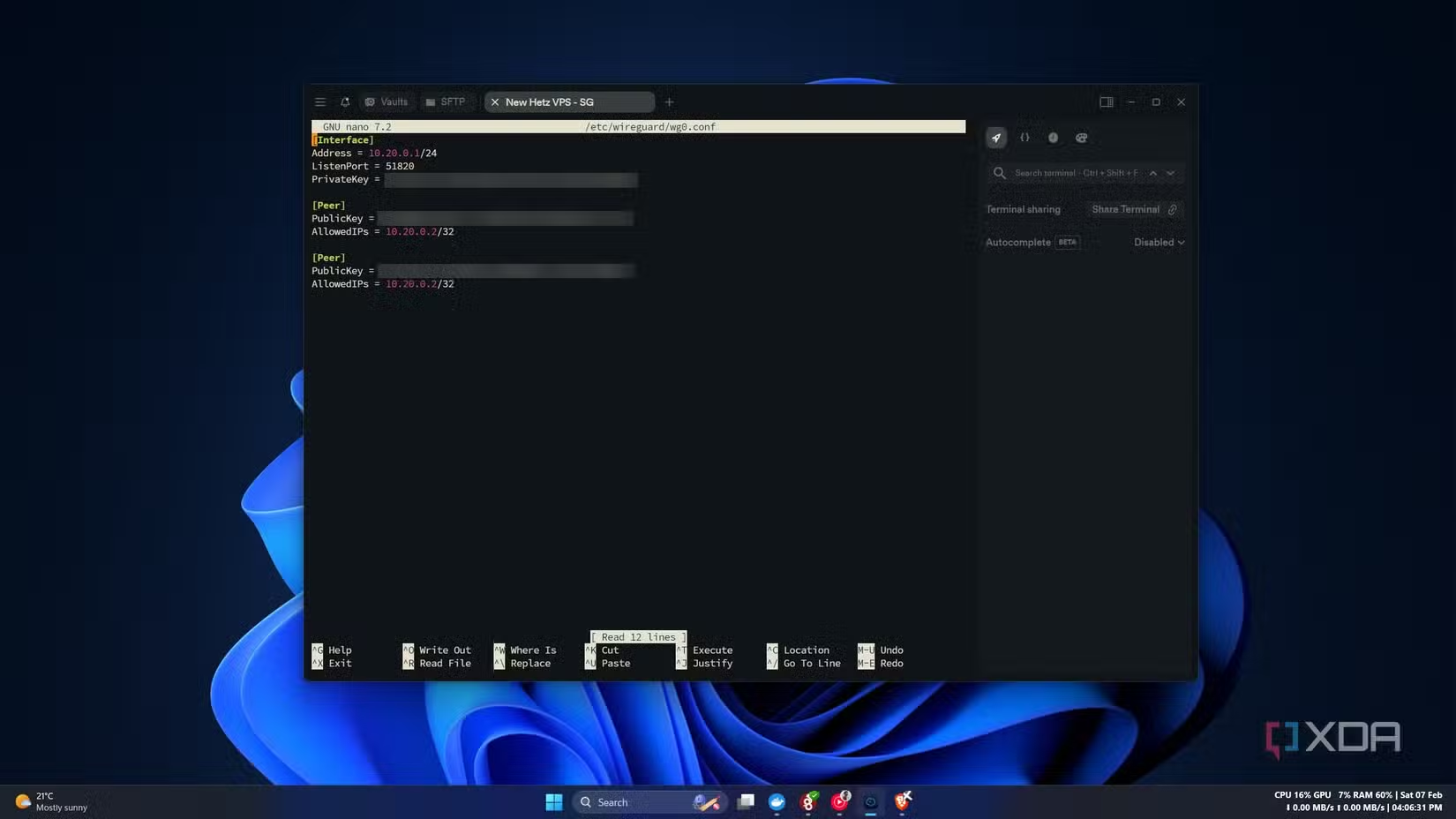
WireGuard operates as a lean, high-performance protocol integrated directly into the Linux kernel. Its design philosophy centers on radical simplicity, utilizing a fixed set of modern cryptographic primitives like Curve25519 and ChaCha20. When running raw WireGuard, every peer requires a manual configuration of public and private keys, tunnel IP addresses, and specific AllowedIPs for routing.
In contrast, squirrelvpn.com and similar managed solutions provide an orchestration layer. While raw WireGuard hits throughput speeds of approximately 900 Mbps on a 1 Gbps link, the lack of a control plane means users must manually exchange keys and define endpoints. This creates a "key-management tax" that grows exponentially with the number of devices. For those seeking deep online privacy news, understanding this distinction between the data plane (the tunnel) and the operational plane (the management) is critical for enhancing online security.
The Complexity of NAT Traversal and CGNAT
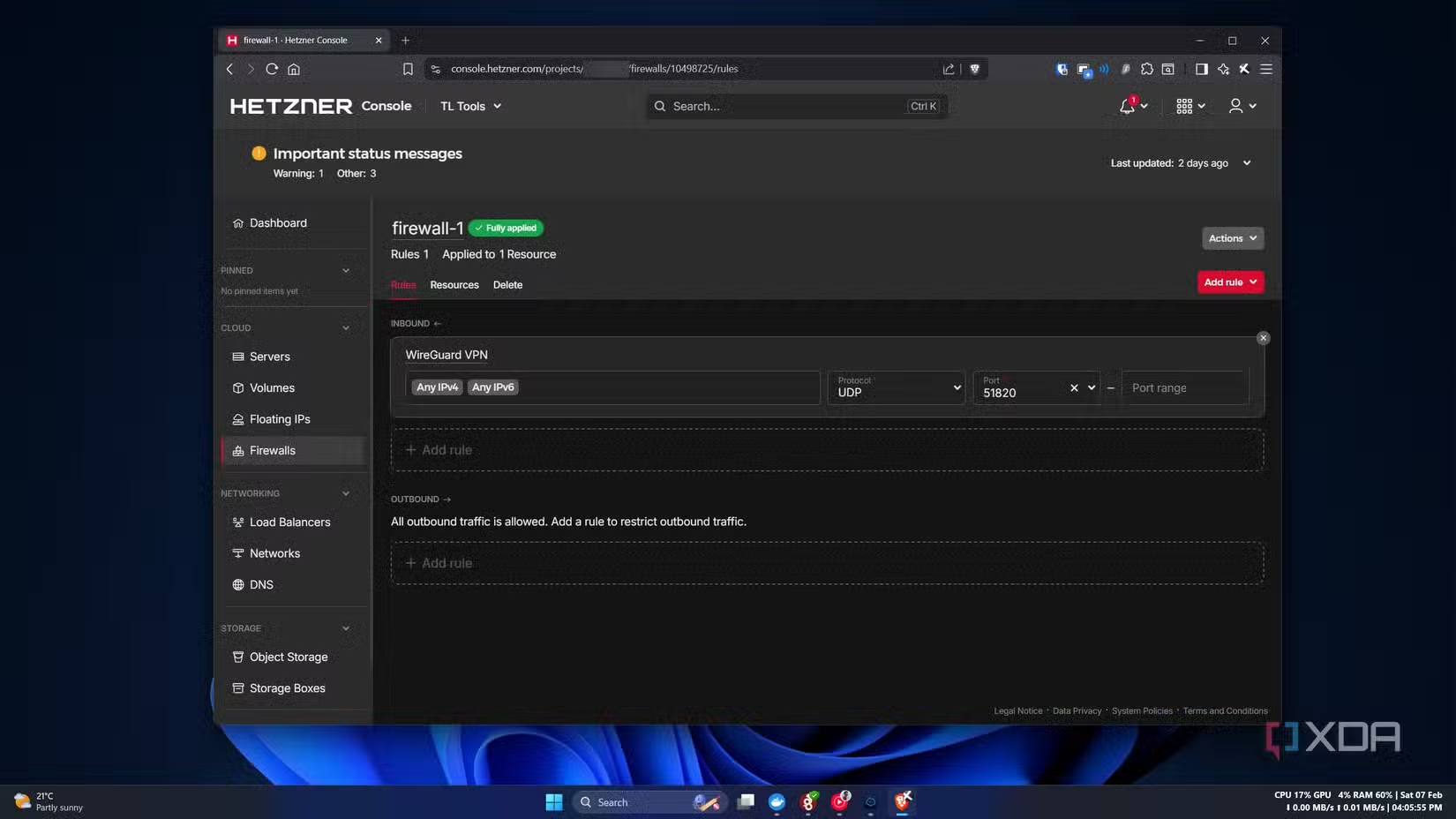
A significant hurdle for raw WireGuard is the requirement for at least one publicly reachable endpoint. In environments behind Carrier-Grade NAT (CGNAT) or restrictive firewalls, establishing a direct handshake becomes nearly impossible without external intervention. Testing in rural network topologies often reveals that port forwarding is ineffective due to dynamic IP allocation and ISP-level nesting.
Managed services bypass these limitations using STUN (Session Traversal Utilities for NAT) and UDP hole punching. When direct peer-to-peer tunnels fail, systems fall back to encrypted relays—often referred to as DERP (Designated Encrypted Relay for Packets). While raw WireGuard is empowering for those with static infrastructure, squirrelvpn.com offers the automation necessary for users on mobile networks or hotel Wi-Fi where network topology is unpredictable.
Orchestration and Configuration Precision
WireGuard is a protocol, not a platform; it does exactly what it is told, offering no error banners or logic validation. A common failure point in manual setups is the SaveConfig attribute in the wg0.conf file, which can inadvertently wipe peer information during service restarts. Debugging these "silent failures" requires intensive use of wg show and system logs, placing the burden of the control plane entirely on the administrator.
Automation tools and managed VPN technology eliminate this friction by handling key rotation and peer discovery automatically. For instance, Headscale serves as an open-source coordination server for those who want the "sugar" of a managed mesh without SaaS dependency. However, for most technology enthusiasts, the trade-off is between the minimalist design of raw tunnels and the frictionless identity integration provided by professional-grade security platforms.
Infrastructure Ownership vs. Operational Complexity
Replacing a managed solution with raw WireGuard highlights a shift from "using" to "owning" infrastructure. Ownership grants full control over routing decisions and firewall rules but demands constant maintenance of VPS uptime and security hardening. In a data-driven environment, the precision of WireGuard is a double-edged sword: it offers no abstraction layer to correct human error, such as mismatched public keys or incorrect subnet routing.
Professional deployments often favor systems that integrate SSO (Single Sign-On) and tag-based ACLs (Access Control Lists). While raw WireGuard is excellent for site-to-site links between data centers with static IPs, it struggles to scale for remote workforces. Security researchers often highlight that while the WireGuard codebase is small and auditable, the human-managed configuration around it is often the weakest link in the digital privacy landscape.
To stay ahead of evolving threats and master the latest in secure connectivity, explore the cutting-edge insights and tools available at squirrelvpn.com.




