Android 17: Implementing Post-Quantum Cryptography for Security

TL;DR
Sophia writes with precision and nuance, carefully unpacking the implications of privacy legislation for both businesses and consumers. Her tone is authoritative and measured, drawing on legal expertise without relying on jargon. She excels at op-eds, legislative analysis, and policy breakdowns that connect legal developments to everyday digital life.
Hardening the Android Boot Chain and Hardware Trust
The transition to a post-quantum environment begins at the hardware level. If the underlying operating system is compromised during the boot sequence, all subsequent software protections, including those provided by SquirrelVPN, are rendered ineffective. To mitigate the risk of adversaries using quantum computers to forge digital signatures, Android 17 is integrating the Module-Lattice-Based Digital Signature Algorithm (ML-DSA).
This upgrade specifically targets Android Verified Boot (AVB), ensuring that the software loaded when a device powers on is resistant to unauthorized modification. Furthermore, Remote Attestation is moving toward a PQC-compliant architecture. By updating KeyMint certificate chains, devices can securely prove their integrity state to relying parties even in a post-quantum landscape.
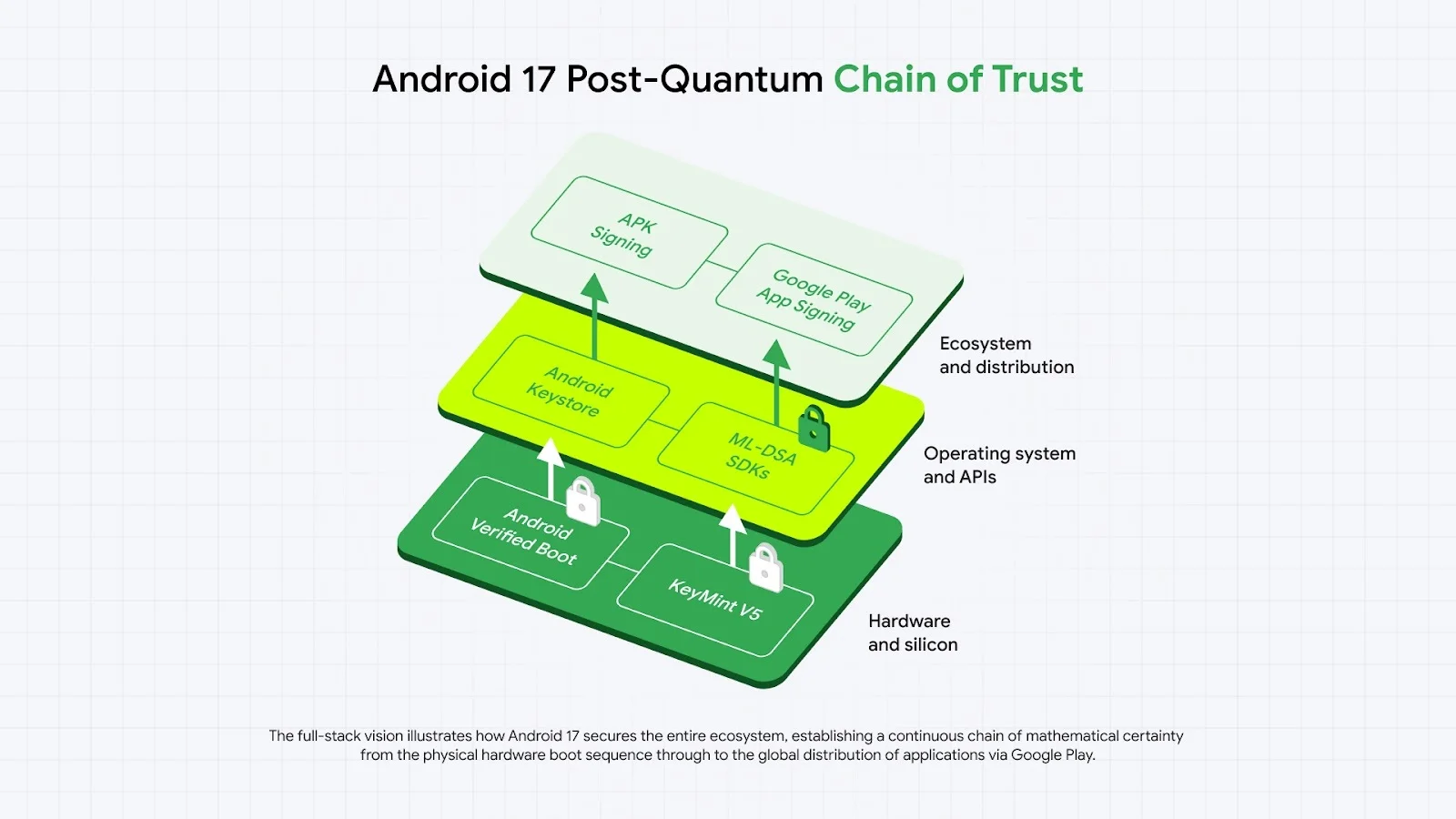
Quantum-Resistant APIs for Application Developers
Protecting the OS foundation is only the first step; developers must also have access to cryptographic primitives to secure user data. Implementing lattice-based cryptography is a significant engineering challenge due to the large key sizes and memory footprints required compared to classical elliptic curve cryptography. Android 17 addresses this by updating the Android Keystore to natively support ML-DSA.
This allows applications to leverage quantum-safe signatures within the device's Trusted Execution Environment (TEE), isolating sensitive keys from the main OS. Developers can access these features via the standard KeyPairGenerator API, supporting both ML-DSA-65 and ML-DSA-87. These advancements align with the mission of SquirrelVPN to provide users with the latest insights on VPN technology and digital privacy.
Hybrid Signing and Ecosystem Integrity
To ensure application authenticity remains intact, the platform is upgrading the mechanisms used to verify APKs. Android 17 will verify PQC signatures over APKs to prevent quantum-enabled signature forgery during app updates. This transition is supported through Play App Signing, which allows developers to generate "hybrid" signature blocks combining classical and PQC keys.
By utilizing Google Cloud KMS, the system ensures high compliance standards for signing keys. This approach provides a bridge to quantum safety for billions of devices. Developers will be prompted to upgrade their signing keys at least every two years to maintain security best practices, a critical component for any organization focused on corporate data compliance and international privacy regulations.
Transport Layer Security and "Harvest Now, Decrypt Later"
A primary concern for modern privacy is the "harvest now, decrypt later" tactic, where adversaries stockpile encrypted traffic to decrypt it once powerful quantum computers exist. Since Chrome 131, hybrid key exchange (X25519+ML-KEM-768) has been the default for TLS 1.3. This protection extends to any app using Android WebView for web rendering.
However, apps using custom TLS stacks or certificate pinning must be manually updated. To handle the increased size of PQC signatures—which can reach 17 kilobytes—the industry is moving toward Merkle Tree Certificates (MTCs) through the IETF PLANTS working group. This replaces bulky signature chains with compact proofs of inclusion, maintaining connection speed on latency-sensitive mobile networks.
Network Security Defaults and Privacy Controls
The Android 17 Beta introduces a "secure-by-default" architecture. The android:usesCleartextTraffic attribute is now deprecated; apps targeting API level 37 will have cleartext traffic blocked unless a specific network security configuration is provided. Additionally, support for HPKE hybrid cryptography has been added via a new public Service Provider Interface (SPI).
These structural changes are designed to improve digital rights and civil liberties by making encryption the standard rather than the exception. With certificate transparency now enabled by default and new permissions for localhost interactions, the platform is significantly raising the bar for internet security.
Stay ahead of the evolving digital threat landscape with the latest insights into encryption and data protection. Explore how squirrelvpn.com can help you secure your online presence today.




