Zero-Knowledge Proofs for P2P Metadata Privacy

TL;DR
The Metadata Problem in Decentralized Networks
Ever wonder why your "private" crypto wallet still feels like someone is watching? It’s because even if nobody knows your name, the network sees your every move through metadata—the digital breadcrumbs we leave behind.
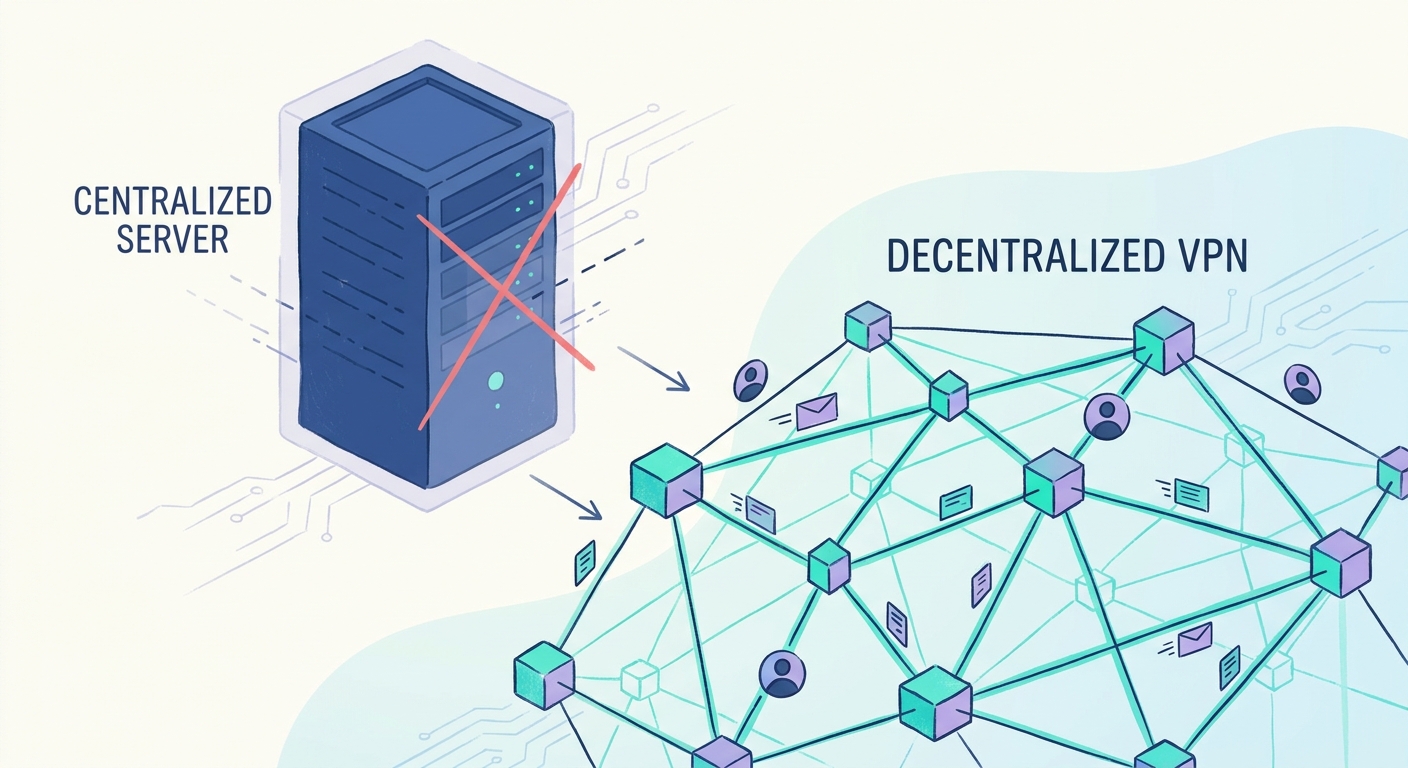
Most people think being pseudonymous on a p2p network is the same as being invisible, but that's a dangerous lie. As noted by Hiro, blockchains and decentralized networks usually offer pseudonymity, where your actions are tied to an address rather than a name, but those actions remain 100% traceable. (Crypto Isn't Anonymous: Understanding Pseudonymity - Nominis)
- Transactional Linkability: Your packets aren't isolated events. If you’re using a dvpn to access a retail site or a healthcare portal, an observer can link those timing patterns to your node's IP.
- Traffic Analysis: Even with encryption, the size of your data packets and how often they're sent creates a "fingerprint." While zkps hide the "who" and "what" on-chain, they don't naturally hide packet timing. You still need network-level tricks like packet padding or onion routing to stop someone from guessing what you're doing based on data bursts.
- The ISP Factor: Your local provider still sees you connecting to a known dVPN entry node, which is often enough to flag your activity in certain jurisdictions. (Q: Can my employer see geographical location when ...)
Metadata is basically the "envelope" of your data. It says who sent it, where it’s going, and how heavy it is. In a p2p setup, this is a goldmine for anyone trying to deanonymize you.
For example, if you're a developer pushing code to a decentralized repo, the api calls you make have distinct sizes. An attacker watching the network doesn't need to see the code; they just need to see a 50kb burst followed by a 2mb pull to guess what you're doing.
Next, we’ll look at how zero-knowledge proofs actually fix this mess.
Understanding Zero-Knowledge Proofs for Privacy
So, how do you actually prove you have the right to access a network without handing over your whole digital identity? It sounds like a paradox, but that's exactly what Zero-Knowledge Proofs (zkps) handle.
Think of it like this: you're trying to enter a 21+ club. Instead of showing an ID that has your home address, height, and full name, you have a magic card that just glows green to prove you're old enough. The bouncer learns zero about who you are, only that you meet the requirement. In the world of decentralized bandwidth, this is huge.
At its core, a zkp is a cryptographic method where a "prover" (you) convinces a "verifier" (the node) that a statement is true without sharing the underlying data. As explained in the classic color-blind friend experiment, you can prove you see a difference between two objects without ever saying what that difference is.
For a zkp to be legit, it needs three things:
- Completeness: If you're telling the truth, the protocol always works.
- Soundness: If you're lying, the math makes it almost impossible to fake the proof.
- Zero-knowledge: The verifier learns nothing except that the statement is true.
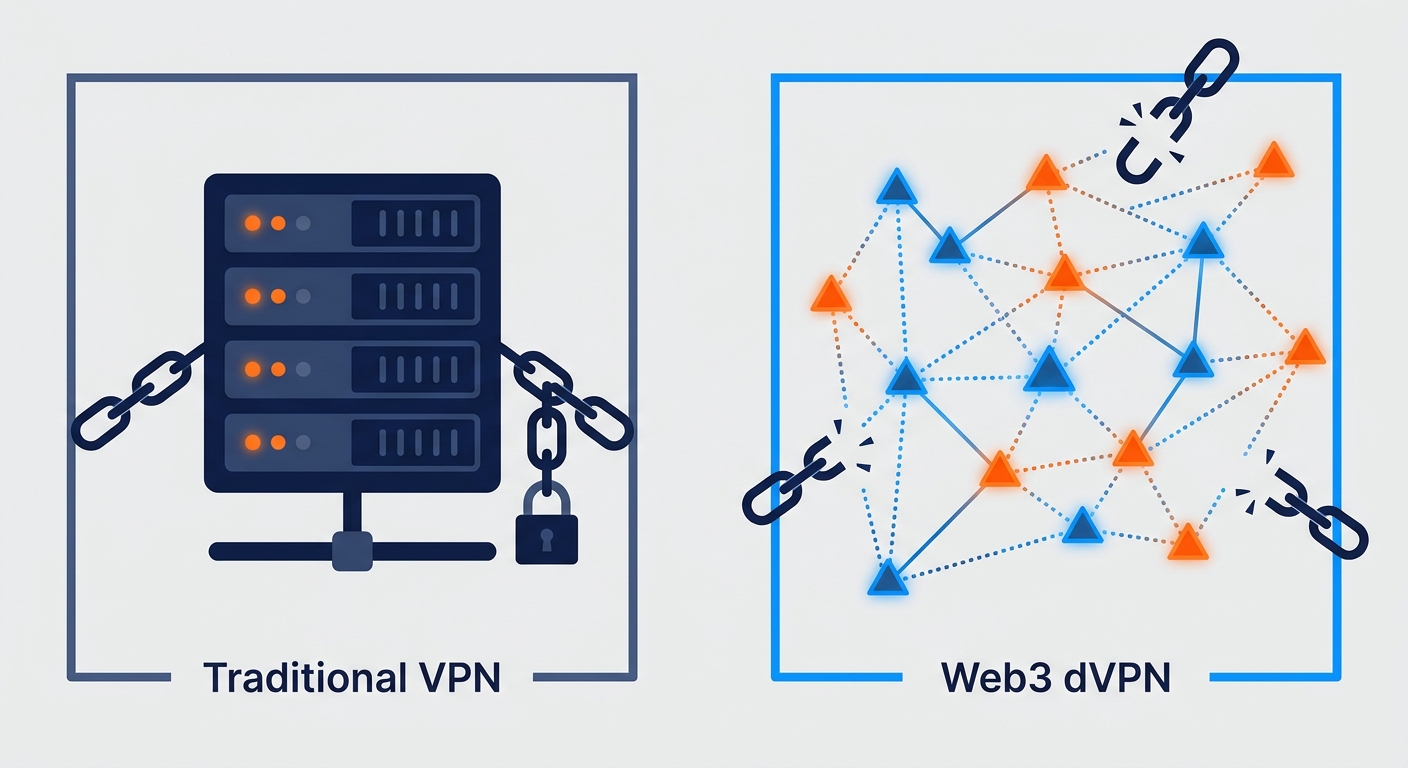
In a web3 vpn, this means you can prove you've paid for bandwidth mining credits without the node ever seeing your wallet history or your real ip.
When we talk about actual implementation in tools like zcash or decentralized proxy networks, two acronyms usually pop up: snarks and starks.
- zk-SNARKs: These are "Succinct" (small and fast). They’ve been around longer, so the documentation is better. The catch? They need a "trusted setup"—a bit of initial data that, if not destroyed properly, is basically "toxic waste" that could be used to forge proofs.
- zk-STARKs: These are the newer, beefier cousins. They don't need a trusted setup (transparent) and they're resistant to quantum computers. The downside is the proof sizes are much larger, which can lead to higher fees or slower speeds on certain chains.
According to StarkWare, using starks allows for massive scalability because you can bundle thousands of transactions into one proof. This is perfect for a p2p bandwidth exchange where you're making tiny payments for every megabyte used.
Next, let's get into the weeds of how we actually implement this to hide your traffic patterns.
ZKP Applications in DePIN and Bandwidth Mining
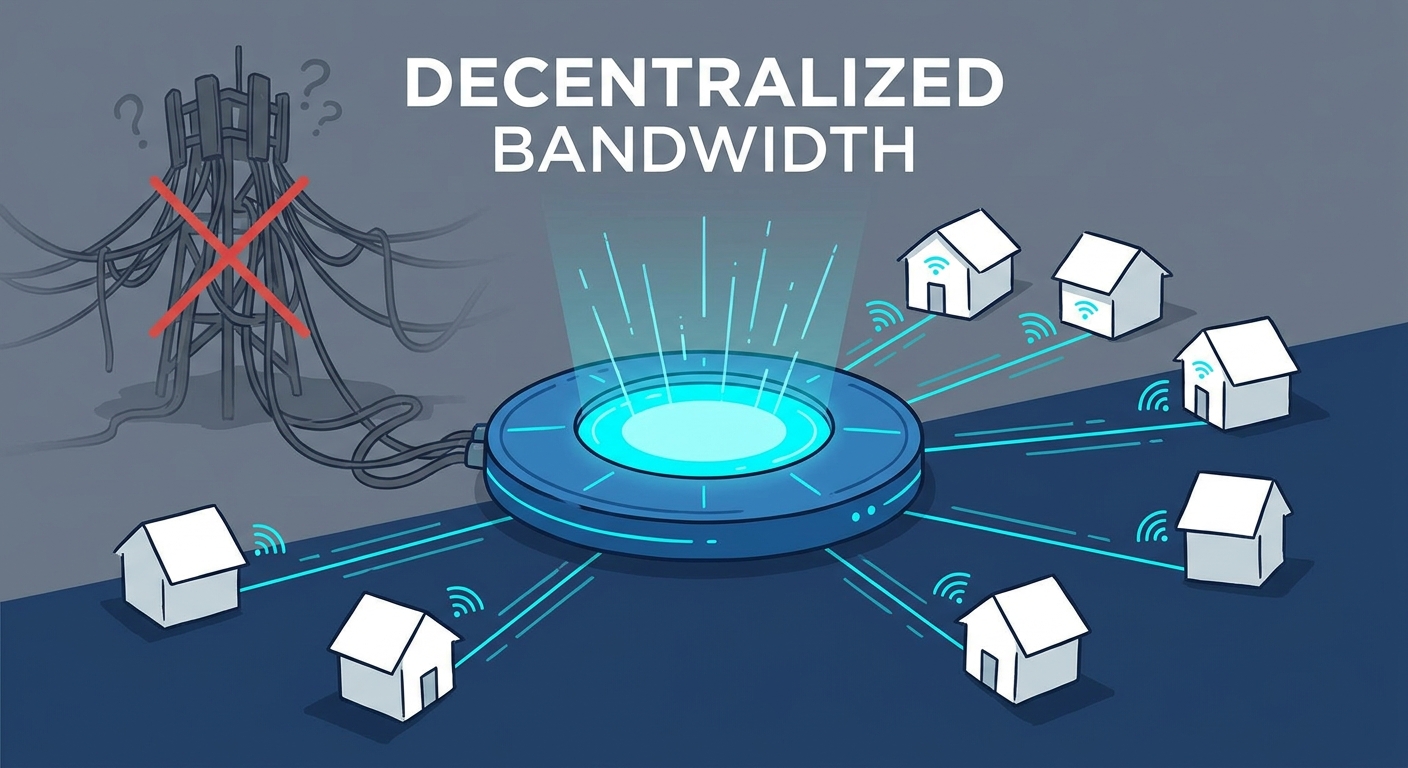
Ever wonder how you can get paid for sharing your internet without some creepy node operator sniffing your traffic? It’s a weird trust gap where we want to earn tokens but don't want to sell our soul (or data) to do it. This is where DePIN (Decentralized Physical Infrastructure Networks) comes in—it's basically a way to build real-world stuff like wifi networks or sensor grids using crypto incentives.
The tech behind these tunneling protocols are evolving fast. We're moving away from old-school protocols that were easy to fingerprint and toward modular setups where the transport layer is totally separated from the identity layer. Instead of a static tunnel that an isp can easily spot, newer DePIN projects use rotating nodes and zkp-based auth to make the connection look like generic encrypted noise. It's less about "vpn tips" and more about how the math handles the handshake without leaking your metadata.
The real magic happens when we use zkps to prove we actually routed data. In a standard setup, the network needs to see your traffic to verify you're working. That's a privacy nightmare. With a bandwidth proof protocol, you generate a proof that says "I moved 500mb of data" without showing what that data was.
- Securing rewards: You get your crypto network rewards by submitting a proof to a smart contract. The contract verifies the math, not the content.
- Node Validation: It allows for privacy-preserving vpn node validation so the network knows you're a "good" node without needing your home ip or logs.
- Tokenized Bandwidth: This turns your spare upload speed into a liquid asset in a decentralized bandwidth exchange.
According to Zcash, this kind of tech lets you maintain a secure ledger of balances without disclosing the parties involved. It's the same logic for depin—proving you provided a service (like storage or bandwidth) while keeping the actual bits hidden.
Next, we're gonna look at how this actually gets implemented in the real world to stop traffic analysis.
The Future of Tokenized Internet Infrastructure
Imagine if you could rent out your home wifi like an airbnb but without ever knowing who's sleeping in the guest room or what they're doing on your network. That’s the dream for a lot of us building out this p2p network economy, and honestly, it’s the only way we get to a truly decentralized internet without getting sued into oblivion.
The goal here is a decentralized bandwidth exchange where you monetize your idle connection. But if i share my bandwidth, i don't want to be liable for what some random person across the globe is downloading. Using zkps, we can build a censorship-resistant vpn where the provider (you) proves you provided the service, and the user proves they paid, but neither of you sees the actual traffic contents or real ips.
To solve the "ISP Factor" where your provider sees you hitting a known node, the future is in stealth addresses and obfuscated bridges. Even if the transaction is hidden by a zkp, these bridges act as a "secret door" that makes your entry point look like a regular zoom call or a netflix stream to your isp.
- Healthcare privacy: A clinic could use a tokenized network to send patient records between nodes. By using zkps, they prove the data was sent and received without the relay nodes ever having a chance to sniff the sensitive medical metadata.
- Retail & Finance: Think about a p2p bandwidth marketplace where a store processes payments. They can use tokenized connectivity to mask the transaction origin, preventing competitors from scraping their sales volume via traffic analysis.
- Global Access: In regions with heavy firewalls, a web3 vpn powered by zkps lets users bypass blocks because the traffic doesn't look like a vpn—it just looks like random, verified noise on the chain.
Look, the math is beautiful, but the computational overhead is a real pain for mobile p2p nodes. Generating a zkp on a high-end server is one thing; doing it on an old android phone acting as a node is another. We need decentralized isp alternatives that don't kill your battery just to stay private.
As we move toward tokenized internet infrastructure, the focus has to shift toward making these proofs "light" enough for everyday hardware. We're getting there, but it's a constant battle between security and performance.
Next up, we're finishing this off by looking at how you can actually start deploying these tools yourself.
Getting Started with Metadata Protection
If you're ready to stop just talking about privacy and actually start using it, there's a few ways to jump in. You don't need to be a math genius to use these tools, but you do need to know which ones actually use zkps under the hood.
- Pick a ZKP-Enabled Provider: Look for depin projects that specifically mention zk-snarks for their "Proof of Connectivity." When you set up a node, check if the dashboard shows "blinded" stats—this means the network is verifying your work without seeing your ip.
- Use Obfuscated Bridges: Since zkps don't hide your connection to the entry node from your isp, always enable "obfuscation" or "stealth mode" in your client settings. This adds the packet padding needed to mess with traffic analysis.
- Wallet Hygiene: Use a privacy-focused wallet that supports shielded addresses (like zcash or iron fish) to pay for your bandwidth. If you pay for a private vpn with a public eth address, you've already leaked your identity before you even hit "connect."
- Run a Light Node: If you have a spare raspberry pi or an old laptop, try running a relay node for a decentralized network. It's the best way to see how the metadata is handled in real-time.
Deploying these tools is about layers. The zkp hides the transaction, the obfuscation hides the traffic pattern, and the decentralized network hides the destination.
Conclusion: A Private Web3 is Possible
So, can we actually have a private web3, or is it just a pipe dream for us nerds? After digging through the math, it's clear that zkps are the only way we stop being "traceable" and start being actually anonymous.
We've spent years just encrypting the "letter" inside the envelope, but as mentioned earlier, the metadata on the outside is what gets you caught. By moving toward metadata obfuscation and zkp-based verification, we're finally building a system where privacy isn't just an optional feature—it's the default state of the network.
The synergy between depin and zkps is the real game changer here. It creates a world where nodes get paid for work they prove they did, but the user's identity stays off the ledger entirely. As discussed previously by Hiro, this balances the openness of blockchain with the confidentiality we actually need to feel safe online. It's the next stage of the revolution—where the internet is finally ours again.