Zero-Knowledge Proofs for Bandwidth Allocation Verification

TL;DR
The problem with proving you sent data
Ever wonder why you're paying for "high-speed" data but your stream still buffers like it’s 2005? It’s usually because we're stuck in a "just trust me" relationship with our internet providers and vpn services.
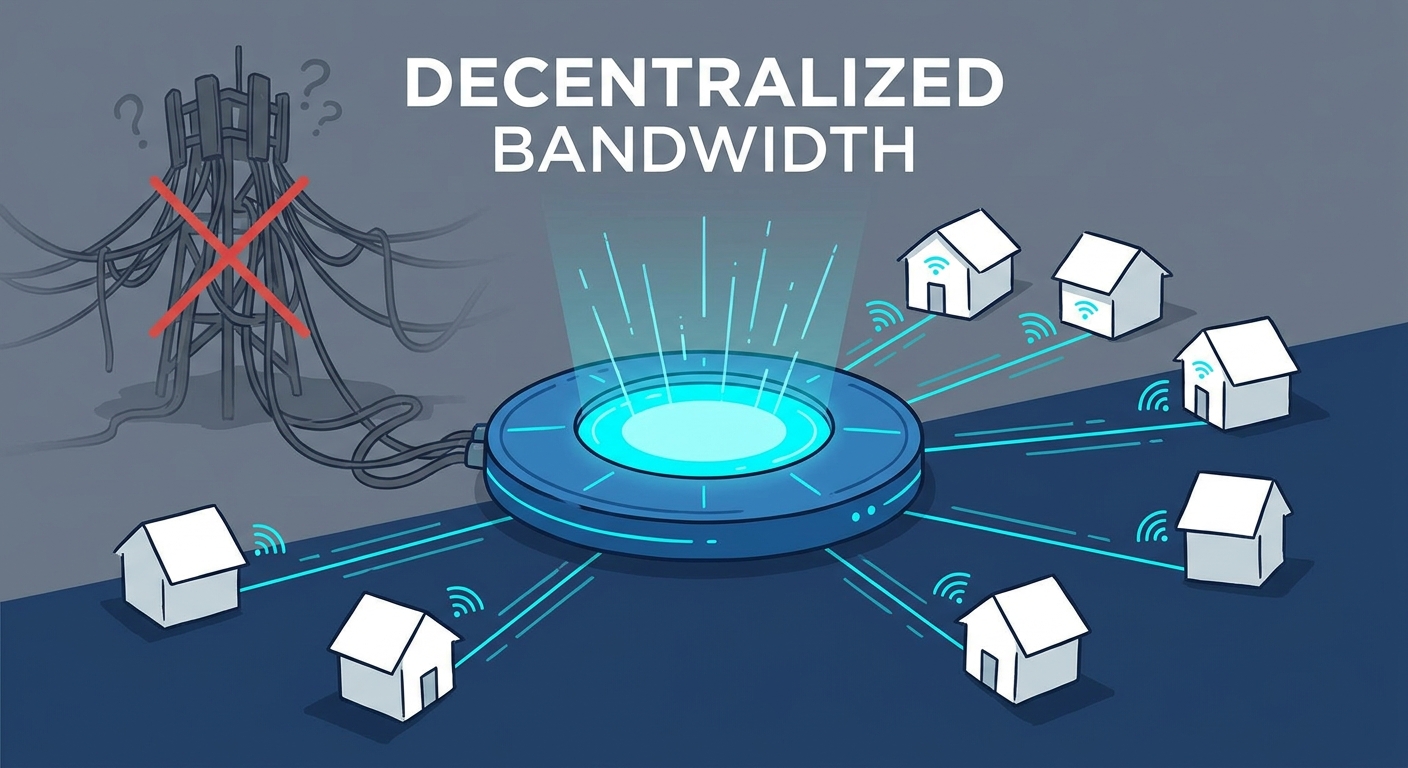
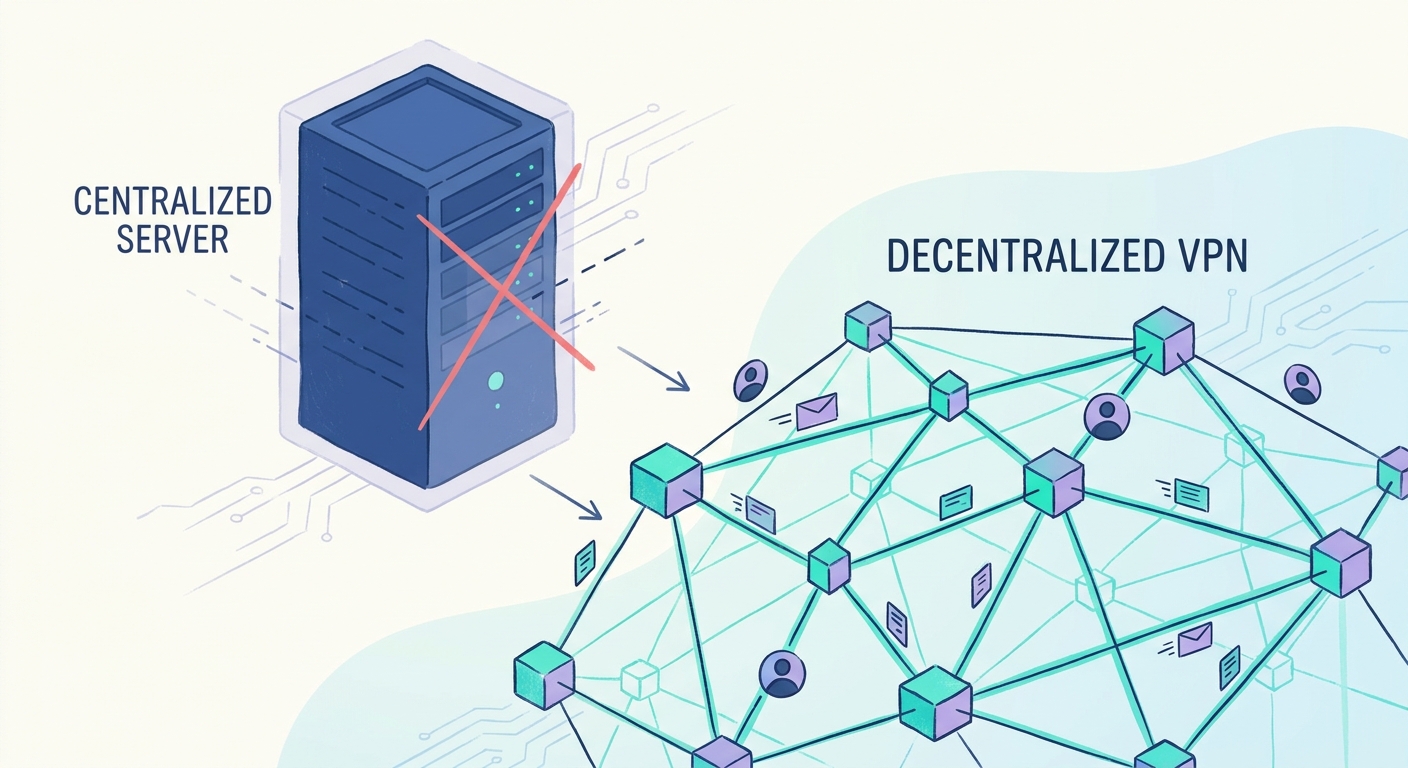
In the old world—what we call the centralized web—you connect to a server owned by a single company. They tell you how much bandwidth you used, and you pay the bill. But in a decentralized physical infrastructure network (DePIN), you’re often getting your internet from a random person’s home node.
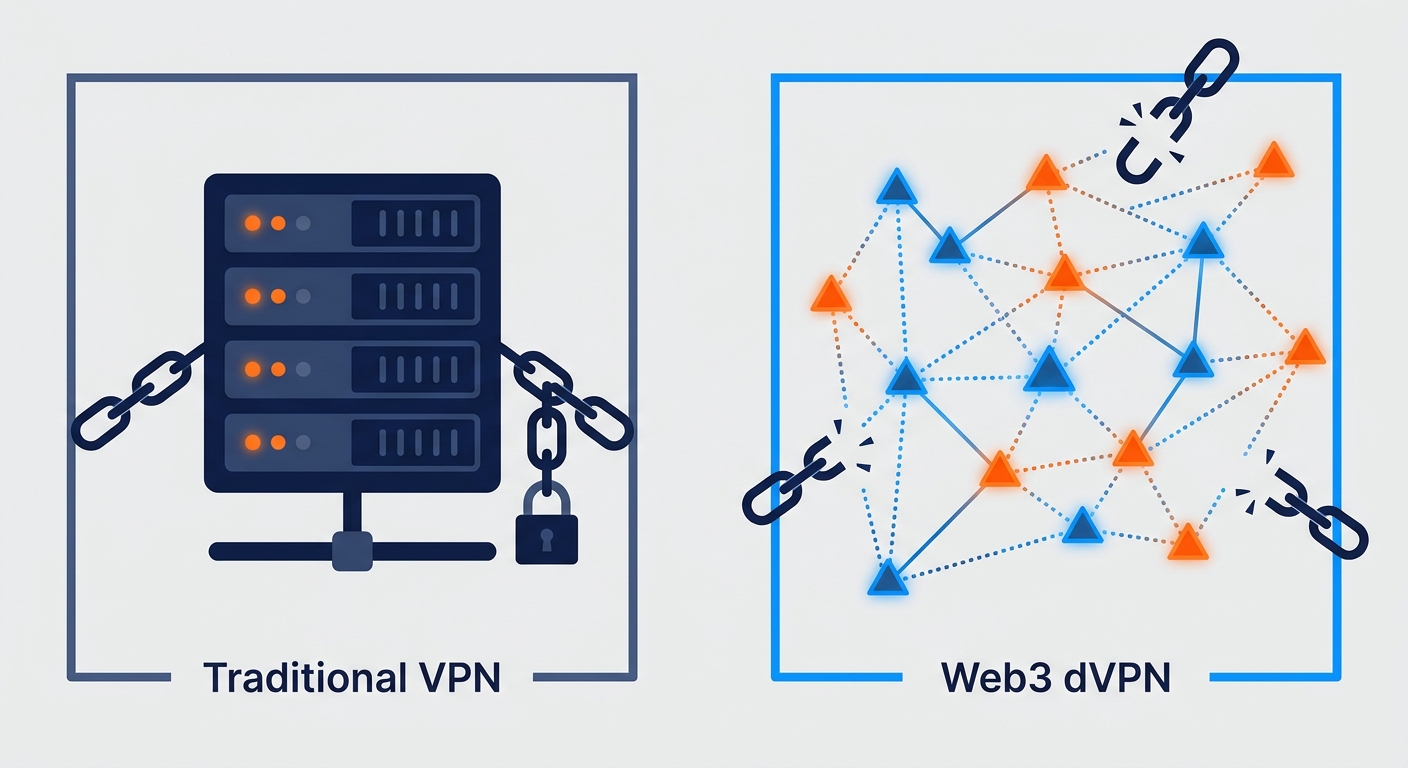
- Centralized logs are a huge privacy hole: Most traditional vpns claim "no-logs," but you’re just taking their word for it. If a government subpoenas them, those logs usually exist.
- The honesty gap: If I'm sharing my home fiber connection with you to earn crypto tokens, what's stopping me from lying to the network and saying I sent you 10GB when I actually sent 1GB?
- The need for "trustless" verification: We need a way to prove data actually moved from point A to point B without a middleman watching the whole conversation.
According to a survey on Zero-Knowledge Proof Frameworks, zkp tech allows a "prover" to convince a "verifier" that a statement is true without revealing the actual secret data. In our world, that means proving I sent you the data without the network having to "sniff" your private packets.
When we talk about "Bandwidth Mining" or "Airbnb for Bandwidth," we’re basically incentivizing people to turn their routers into mini-isps. But crypto incentives bring out the "gamers"—people who want the rewards without doing the work.
As shown in the following diagram of the bandwidth verification workflow, we need a system that checks the data flow without exposing the user.
If we just let nodes report their own stats, the system collapses from fraud. On the flip side, if we let the network see everything to verify the traffic, we’ve just built a giant surveillance machine.
Measuring peer-to-peer (p2p) traffic is notoriously messy. Unlike a retail checkout where a barcode gets scanned, data packets are fluid. In industries like healthcare or finance, this is even more sensitive. You can't just have a third party inspecting packets to see if the node is being honest.
A 2023 report from the arkworks zksnark ecosystem suggests that modular libraries are becoming the standard for building these types of "succinct" proofs that can run on low-power hardware.
We need math—specifically cryptographic commitments—to bridge this gap. Without it, bandwidth remains a "best effort" service rather than a guaranteed resource. Since these use cases require high reliability, the cost of running these checks on a blockchain becomes a major hurdle we have to clear.
What are zero-knowledge proofs anyway
Imagine you want to prove to a club bouncer that you're over 21, but you don't want him seeing your home address, your height, or exactly how bad your DMV photo looks. Instead of handing over the physical ID, you show him a black box that flashes a green light only if you meet the age requirement.
That is essentially what a zero-knowledge proof (zkp) does for the digital world. It’s a way to say, "I have the answer," without actually showing the work or the data behind it.
In the context of our bandwidth marketplace, it’s how a provider proves they sent you exactly 500MB of encrypted traffic without the network ever seeing what’s inside those packets. It bridges the gap between "trust me" and "here is the math that says I'm not lying."
At its core, a zkp involves two characters: the Prover (the person sharing their bandwidth) and the Verifier (the blockchain or the user receiving the data). The goal is for the Prover to convince the Verifier that a statement is true while revealing absolutely zero extra info.
To make this work, every zkp system has to nail three specific things:
- Completeness: If the node actually sent the data, the math should work out every time so they get paid.
- Soundness: If the node is a liar, the math should fail almost 100% of the time. No cheating allowed.
- Zero-knowledge: The Verifier learns nothing about the actual files being transferred—just that the volume and destination were correct.
This is how we keep the "zero" in zero-trust networks. In a dvpn, you don't want the network nodes snooping on your Netflix habits or your banking login. By using zkps, the node can prove it fulfilled its contract to the network—earning those crypto rewards—without ever "peeking" at your private stream.
When you start digging into the technical weeds of depin projects, you’ll run into two main "flavors" of these proofs: snarks and starks. They sound like characters from a Lewis Carroll poem, but they have very different vibes in practice.
zk-snarks (Succinct Non-Interactive Arguments of Knowledge) are the older, more established sibling. They are "succinct," meaning the proofs are tiny—sometimes just a few hundred bytes. This is great for mobile vpn users because it doesn't eat up your data just to verify the connection.
However, most snarks (like the famous Groth16 protocol) require a "trusted setup." This is a one-time event where some random numbers are generated to start the system. If the people running that setup are corrupt, they could theoretically forge proofs. As mentioned earlier in the survey on Zero-Knowledge Proof Frameworks, this is why many newer projects are looking for alternatives.
zk-starks (Scalable Transparent Arguments of Knowledge) are the newer, beefier version. They don't need a trusted setup—they are "transparent." They also have a massive advantage: they're resistant to quantum computers.
The following architecture diagram illustrates the trade-offs between snark and stark workflows in a p2p environment.
In a p2p bandwidth exchange, we’re trying to build a decentralized isp. In retail, you'd never pay a cashier who just "promised" they put the milk in the bag without looking. In finance, you don't just trust a bank's spreadsheet; you want an audit.
zkps provide that audit for data. Whether it's a healthcare provider sending sensitive patient records over a vpn or a retail chain syncing inventory across thousands of stores, they need to know the data arrived without the middleman (the node) seeing the contents.
Verifying bandwidth without spying
So, you’re running a node and sharing your bandwidth to earn some crypto. Great. But how does the network actually know you’re sending real data to a user in, say, Berlin, without someone literally "sniffing" the packets to check?
It’s a massive technical headache. If the network can see the data to verify it, your privacy is toast. If it can't see anything, you could just "mine" tokens by sending junk data to yourself. This is where we get into the nitty-gritty of bandwidth proof protocols.
To solve this, we use a specific flavor of math called vOLE-based Zero-Knowledge (Vector Oblivious Linear Evaluation). I know, it sounds like something out of a sci-fi novel, but it’s actually incredibly elegant for high-speed data.
Unlike snarks or starks that often use heavy elliptic curves, vOLE is a form of "Interactive Oracle Proof" that prioritizes prover speed over proof size. It’s basically built for speed, making it perfect for verifying massive streams of data in real-time without lagging your connection.
- High-speed verification: vOLE-based protocols are great because they don't rely on heavy math for every step. This makes them much faster for real-time bandwidth mining.
- Consistency checks: The network uses these proofs to ensure the node actually has the upload speed it claims. If you claim to be a "Supernode" but the math doesn't add up, the smart contract simply won't trigger the payout.
- Stay in the loop: If you're deep in the weeds on this, staying updated with communities like squirrelvpn—a news resource and community for decentralized vpn tech—is a good move to see which protocols are actually hitting the mainnet.
The diagram below shows how vOLE creates a secure handshake between the node and the verifier.
Now, the cool part is how this links to your wallet. In a decentralized vpn (dvpn), we want the rewards to be automatic. You shouldn't have to wait for a human "manager" to approve your earnings.
We use Smart Contracts that act as the ultimate escrow. These contracts are programmed to be "blind" but fair. They hold the tokens and only release them when a valid zkp is submitted. No proof, no pay. It’s a brutal but necessary way to keep the p2p network honest.
Solving the Gas Problem
One big issue in the past was "gas costs"—the fee you pay to put data on a blockchain. If the proof is too big, you’d spend more on fees than you earned in rewards. This is the "economics of on-chain verification" that kills many projects.
To fix this, we use Recursive Proofs. This is basically a way to verify multiple small proofs inside one big one. Instead of sending 1,000 transactions to the blockchain for 1,000 small data transfers, the system batches them into a single proof. This spreads the gas cost across thousands of claims, making it pennies per user.
Layer 2 solutions also help by moving the heavy lifting off the main chain. By verifying the zkp on a faster, cheaper network and only settling the final balance on the main blockchain, we keep the system profitable for node owners.
- Automated Payouts: The moment the zkp is verified on-chain, the tokens are moved to the node's wallet. There’s no "trust" involved, just code.
- Reducing Overhead: Libraries like arkworks are helping shrink these proofs down so they're "succinct" and cheap to verify.
- Fraud Prevention: Because the math is "sound," it’s statistically impossible for a node to fake a 1GB transfer without actually having the data.
Real world use cases for zkp in depin
Ever wonder how you can sell your extra home internet to a guy in Tokyo without either of you getting scammed? It sounds like a tech thriller plot, but it's actually the bread and butter of the depin movement.
The dream is simple: you have a 1Gbps fiber connection at home, but you only use it to watch Netflix and doomscroll on reddit. Why not sell the excess? In a decentralized vpn (dvpn) model, your router becomes a node.
- Quality of Service (QoS) Guarantees: We use zkps to prove that a node actually provided the 100Mbps speed promised. The node generates a proof of "work" that the chain verifies before releasing your crypto.
- Privacy for the Provider: You don't want to know what the buyer is doing. zkps allow the network to verify the traffic volume without you ever seeing the unencrypted packets.
This flowchart illustrates how a user requests bandwidth and the node provides a proof to get paid.
One interesting approach is seen in how projects handle "Proof of Connectivity." They need to know your node is actually online. Instead of pinging you every second, they can use a zkp to prove your node was active over a specific window of time.
Now, let’s talk about the high-stakes stuff. If you’re in a country with a "Great Firewall," just the act of using a vpn can be a red flag. Traditional vpn protocols have "signatures" that deep packet inspection (dpi) can spot.
This is where Censorship-Resistant Access comes in. By using zkps, we can create "obfuscated" connections. The goal isn't just to encrypt the data, but to prove to the network that the connection is valid without revealing that it’s a vpn tunnel at all.
The following diagram shows how metadata is hidden during a connection to bypass censorship.
Challenges and the road ahead
So, we’ve got the math down, but can your old router actually handle it without catching fire? That is the million-dollar question because nobody wants a private internet connection that feels like they're back on a 56k dial-up modem.
The reality is that generating a zkp is "expensive"—not necessarily in dollars, but in CPU cycles. If you’re trying to run a high-speed dVPN node on a cheap home router, the math starts to get heavy.
- Latency vs. Privacy: There’s a classic trade-off here. If we want 100% absolute cryptographic certainty for every single packet, your ping is going to skyrocket.
- Hardware Acceleration: We’re starting to see a shift toward using GPUs or specialized chips to handle these proofs.
This final diagram shows the future roadmap for hardware-accelerated zkp verification.
Honestly, the "usability gap" is the biggest wall we're hitting. A 2024 study by researchers at UC San Diego and Arizona State University found that while many frameworks exist, this gap is still the biggest hurdle for developers trying to implement these tools in the real world. Most dvpn users don't want to know about elliptic curves; they just want their privacy.
Looking ahead, we’re moving toward a world where the "isp" isn't a giant company with a skyscraper, but a global web of people like you and me. ZKP is basically the final piece of the puzzle for this web3 infrastructure. It’s what makes the system "trustless"—you don't need to know the person providing your bandwidth, because the math proves they aren't cheating you.