Zero-Knowledge Proofs for Anonymous Node Validation

TL;DR
The Problem with Traditional Node Verification
Ever wondered why your vpn provider asks for a photo of your ID just so you can help "privatize" the web? It's a total paradox, right?
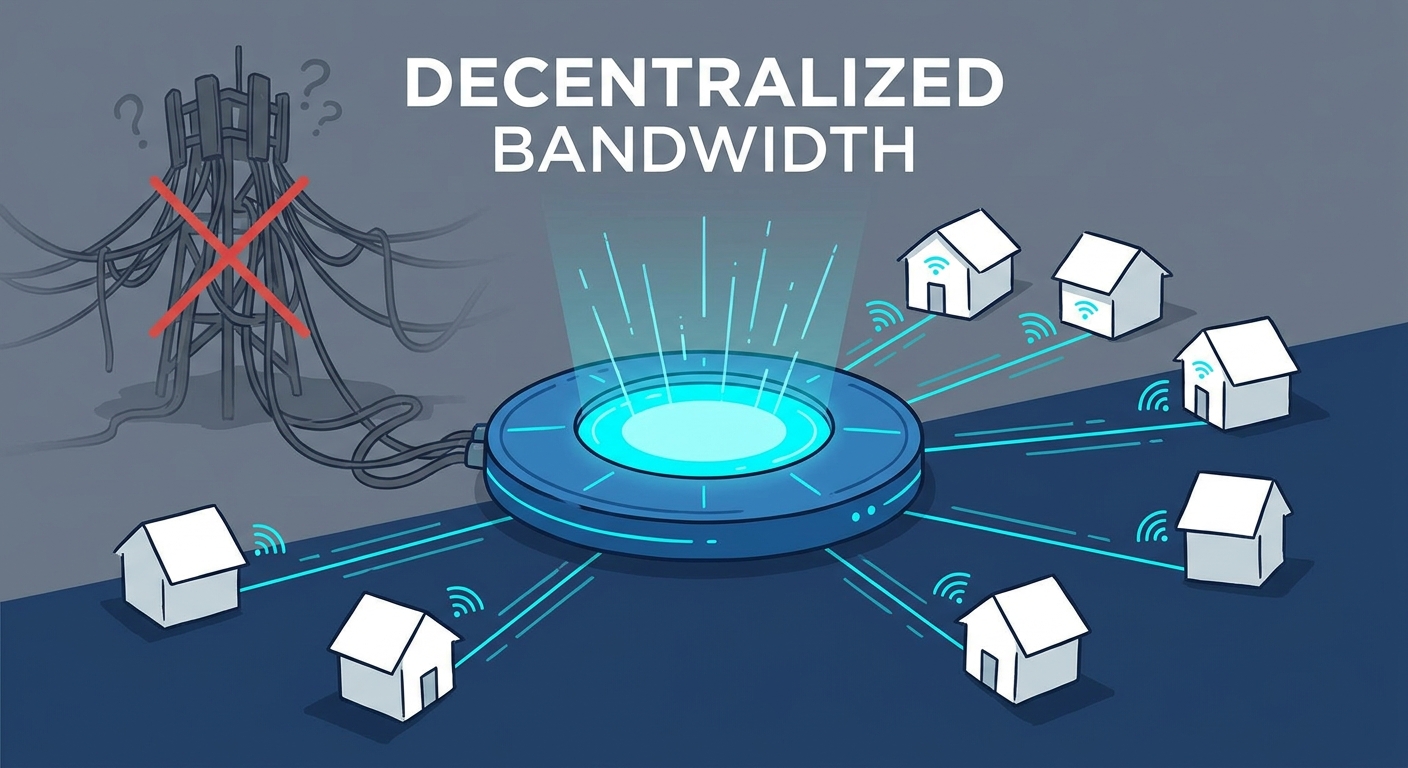
Traditional node verification is kind of a mess for anyone trying to run a decentralized network. Usually, if you want to be a node provider—basically an "Airbnb for bandwidth"—you end up stuck in a trap. Centralized systems often force you to hand over kyc data or they log your home IP address permanently. (Nearly ALL wallet providers are tracking your IP address) This creates a massive paper trail that ruins the whole point of p2p.
- Identity Exposure: In many dvpn setups, the person hosting the node is at risk if their real identity leaks to a malicious user.
- Metadata Leaks: Even without a name, constant ip logging allows for targeted attacks on bandwidth miners by pinpointing their physical location.
- Verification Bottlenecks: Many networks rely on semi-centralized "watchers" to check if a node is "legit," which creates a single point of failure and a juicy target for hackers.
According to Dock.io, traditional physical documents or digital logs often reveal way more info than needed, and storing this on centralized databases makes them sitting ducks for breaches.
Take a look at retail or healthcare; if a doctor had to show their entire medical history just to prove they have a license, nobody would do it. It's the same for bandwidth sharing. We need a way to prove a node is "good" without saying who owns it. Next, we'll look at how math actually fixes this.
What are Zero-Knowledge Proofs Anyway?
Imagine you're trying to get into a club, but instead of showing your ID, you just prove you're over 21 without the bouncer seeing your name or address. Sounds like magic, right? Well, in the crypto world, we call this a zero-knowledge proof (zkp).
Basically, it's a way for a "prover" to convince a "verifier" that a statement is true without sharing the actual data. Think of the "Where’s Wally?" (or Waldo) analogy. To prove you found him without showing his spot on the map, you could place a giant sheet of cardboard with a tiny hole over the picture, showing only Wally's face. You've proven you know where he is, but your friend still has no clue about his coordinates.
In a dvpn context, "Wally" represents the node's compliance with network rules—like having a valid license or meeting speed requirements—without revealing the node's specific identity or location.
In a p2p network, we need to know a node is legit before we route traffic through it. But we don't want to know who owns it. zkp makes this possible by satisfying three big rules:
- Completeness: If the node is honest, the network will definitely accept it.
- Soundness: If a node tries to fake its credentials, the math will catch them.
- Zero-knowledgeness: The network learns absolutely nothing about the node's private keys or owner.
You'll mostly hear about two flavors here. zk-snarks are super small and fast to verify, which is great for mobile vpn apps. These often use Universal Setups (like the ones discussed by teams at circularise and dock.io), which means the initial "trust" phase only has to happen once for many different types of proofs.
On the other hand, zk-starks are "transparent" (no trusted setup) and even quantum-resistant. They're a bit bulkier, but as Chainalysis points out, they're designed to scale for huge computations. Honestly, for most bandwidth sharing, the speed of snarks usually wins out.
Implementing ZKPs in Decentralized VPNs
So, we’ve figured out that math can prove you're "good" without snitching on your identity. But how do we actually drop this into a dvpn without making the whole thing crawl like a 56k modem?
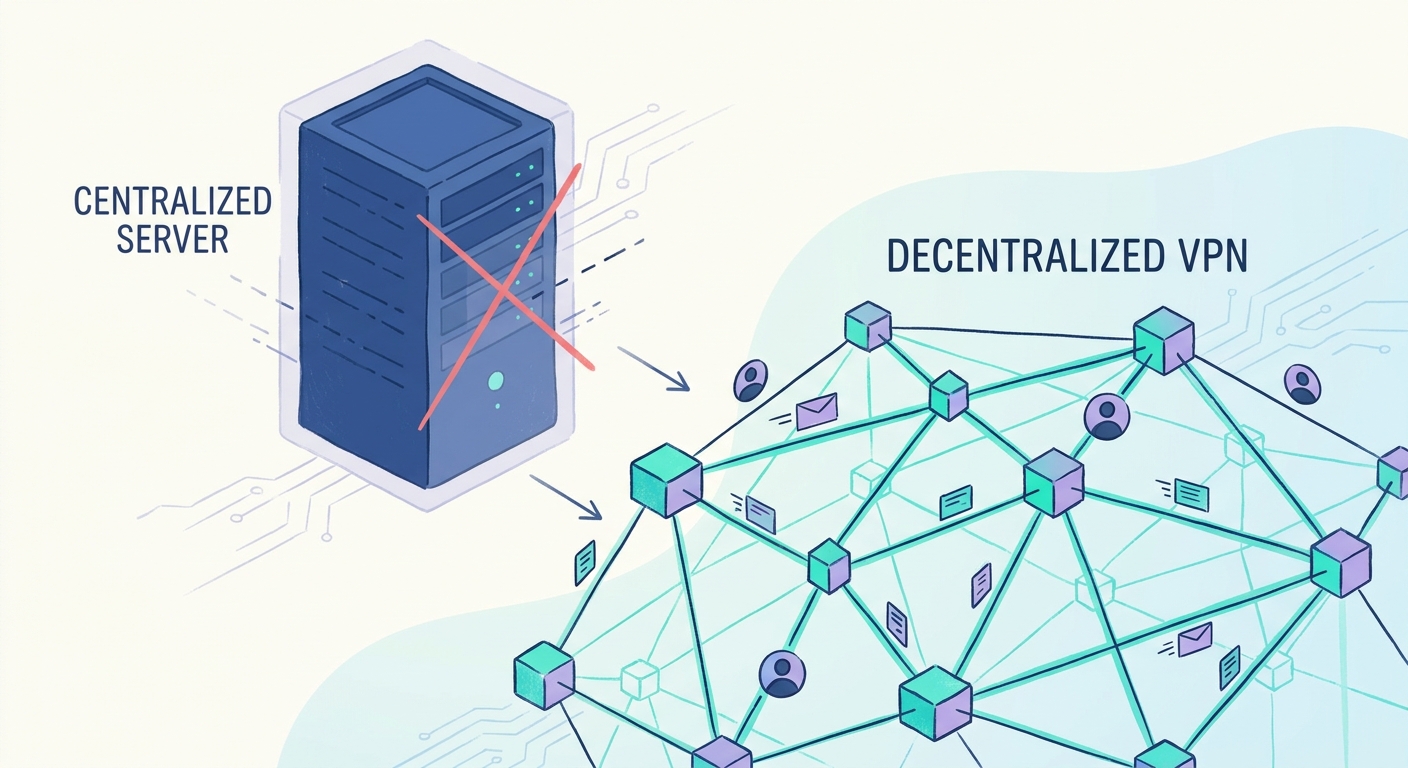
In a decentralized setup, we use these proofs to handle the "trust but verify" part of the job. Usually, a vpn needs to know if a node is actually fast or just pretending. Instead of the network pinging your home address constantly—which is a privacy nightmare—the node generates a proof.
- Bandwidth and Uptime: A node can prove it handled a certain amount of traffic or stayed online for 24 hours. It uses a "range proof" to show the speed is, say, between 50mbps and 100mbps without revealing the exact telemetry that could fingerprint the ISP.
- Reward Triggers: This is where it gets spicy for bandwidth miners. Smart contracts can be set up to release tokens only when a valid zkp is submitted. No proof, no pay. it keeps the network honest without a central boss watching over your shoulder.
- Proof of Software Integrity: When the vpn protocol updates, nodes can prove they’ve switched to the latest version (like aes-256-gcm). This is done through "Remote Attestation," where the node provides a zkp of a hash of the running code. This proves the node is running the right software without needing a central auditor to log in and check.
We're seeing this move beyond just crypto. For example, industries like healthcare use similar logic to verify medical licenses without sharing a doctor's entire history. In our world, Ancilar explains how developers use tools like Circom to build "circuits." Think of a circuit as a mathematical representation of the rules the node needs to prove—like a digital checklist that the math verifies.
The P2P Bandwidth Marketplace and Token Incentives
Imagine if you could turn your spare home internet into a revenue stream without ever worrying about some stranger using your ip for something shady. That’s the dream of a Decentralized Physical Infrastructure (DePIN), but it only works if the incentives are actually worth the risk.
In a distributed relay network, we use tokenized rewards to coax people into sharing their connection. But how do we stop one guy with a powerful server from pretending to be 5,000 different residential nodes just to drain the reward pool? This is the classic "sybil attack," and it's a total buzzkill for p2p economies.
To keep things fair, the network needs to verify that you're actually providing the speed you claim.
- Proof of Contribution: Instead of a central boss checking your speed, you submit a zkp. This proves you hit your 100mbps target without leaking your exact gps coordinates.
- Sybil Resistance: By requiring a "proof of unique hardware" via cryptography, the system ensures rewards go to real humans, not just bot farms.
- Automated Payouts: Smart contracts act as the escrow. If the math in your zkp checks out, the tokens hit your wallet instantly.
As previously discussed, this "trust but verify" model is already being used in finance. For instance, Circularise explains how companies use these proofs to confirm they're paying fair market prices without actually revealing the private dollar amounts to competitors.
Security and Bad Actors
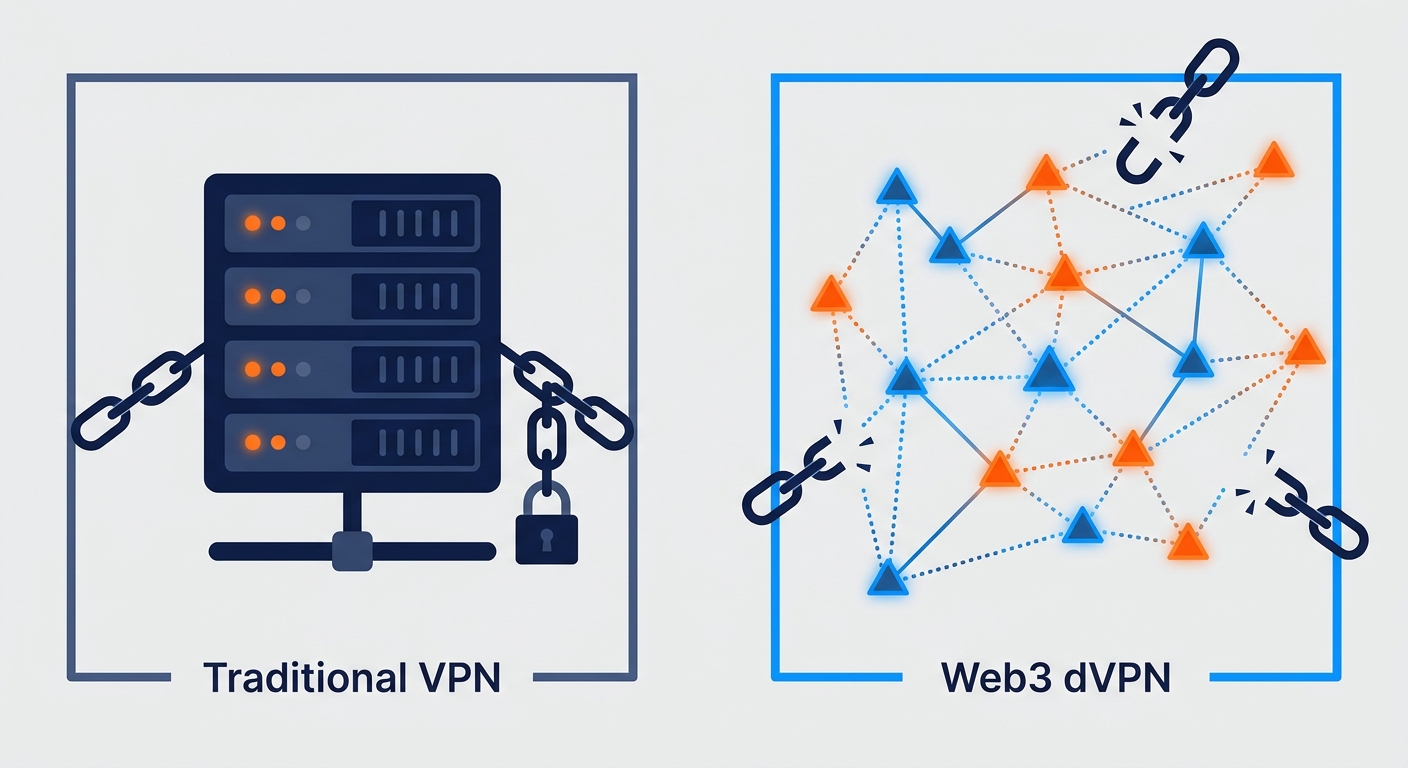
So, how does this actually stop the "bad guys" from ruining the party? In a regular vpn, you just hope the provider is blocking malicious stuff. In a dvpn, we use math to build a wall.
First off, Sybil Attacks are the biggest threat. If someone can create a million fake nodes, they can control the network. ZKPs stop this by requiring a proof of unique hardware or a "proof of stake" that doesn't reveal the owner's wallet balance. You prove you have the "skin in the game" without showing the game board.
Then there is Malicious Traffic Injection. If a node tries to mess with your data or inject ads, the zkp-based integrity checks will fail. Because the node has to prove it's running the exact, untampered code (that "Software Integrity" we mentioned), it can't easily swap in a "bad" version of the vpn software to spy on you.
Finally, Data Spoofing is a huge issue where nodes lie about how much bandwidth they actually provided to get more rewards. By using cryptographic "receipts" from the users they served, nodes generate a zkp that proves the traffic actually happened. If the math doesn't add up, the node gets slashed (loses money) and kicked off the network. It's like a bouncer that can see through every lie.
Future Trends in Anonymous Internet Access
So, what’s next for the distributed relay network once we’ve nailed the math? Honestly, we’re looking at a world where your isp doesn't even know you’re online, let alone what you’re doing.
The shift is moving from simple apps to raw hardware. Imagine a router that has zkp and post-quantum cryptographic algorithms baked into the silicon. You wouldn’t just "run" a vpn; your entire home network would be a stealth node by default.
Here is what’s actually coming down the pipe:
- Hardware-Level Privacy: Next-gen routers will use secure enclaves to generate proofs of uptime without ever touching your personal traffic data.
- Universal Setups: As mentioned before, we’re moving toward systems that don't need a "trusted setup" for every new app, making it way easier for devs to build anonymous tools.
- Quantum Resistance: New protocols are already eyeing algorithms that even a quantum computer couldn’t crack, keeping your bandwidth mining rewards safe for decades.
It’s a bit messy right now, but the tech is catching up to the dream of a truly decentralized internet. Stay curious, because the gatekeepers are losing their keys.