Tokenomics of Resource-Weighted Bandwidth Mining

TL;DR
The Evolution of Bandwidth Mining in depin
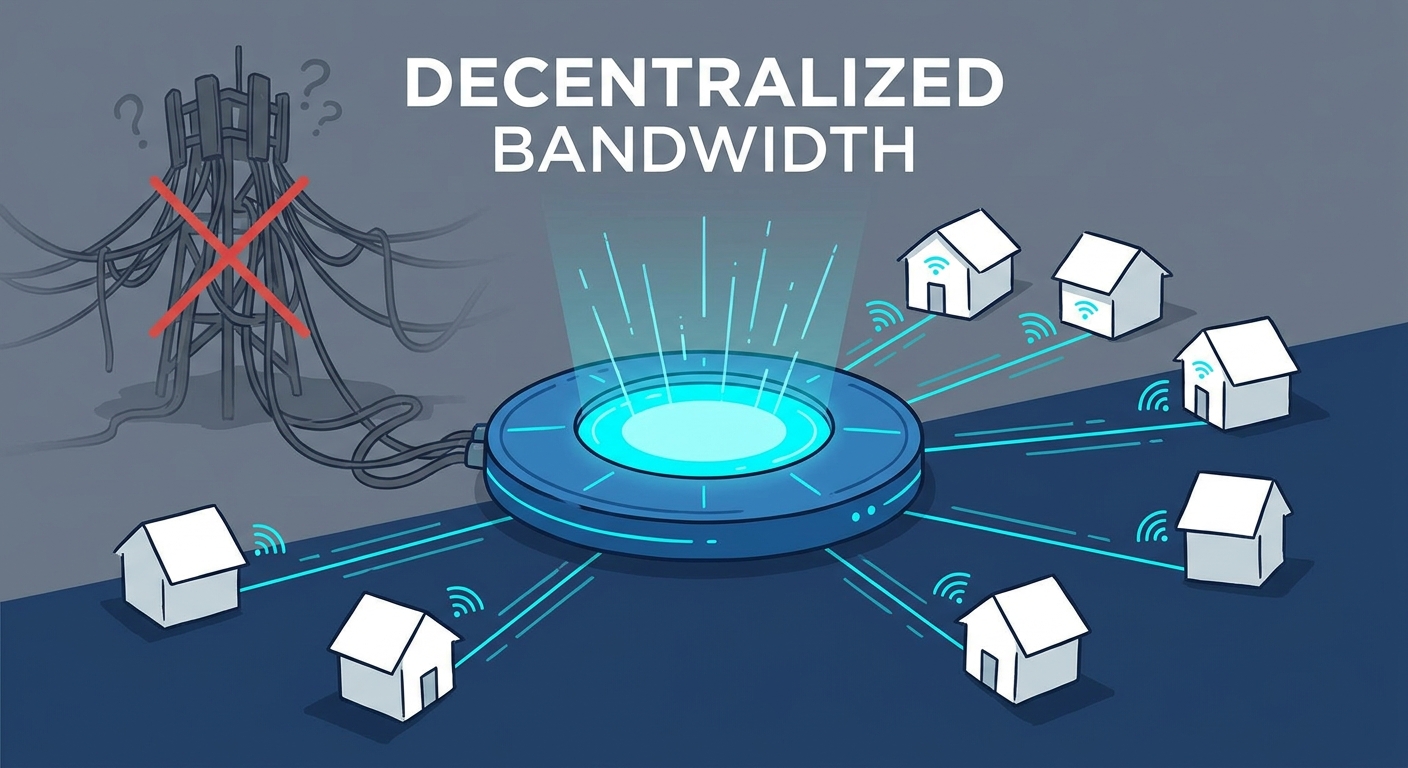
Ever wondered why your home internet sits idle most of the day while big companies pay a fortune for bandwidth? It’s a bit of a waste, right? That’s where depin (Decentralized Physical Infrastructure Networks) comes in, turning your router into a mini-revenue stream.
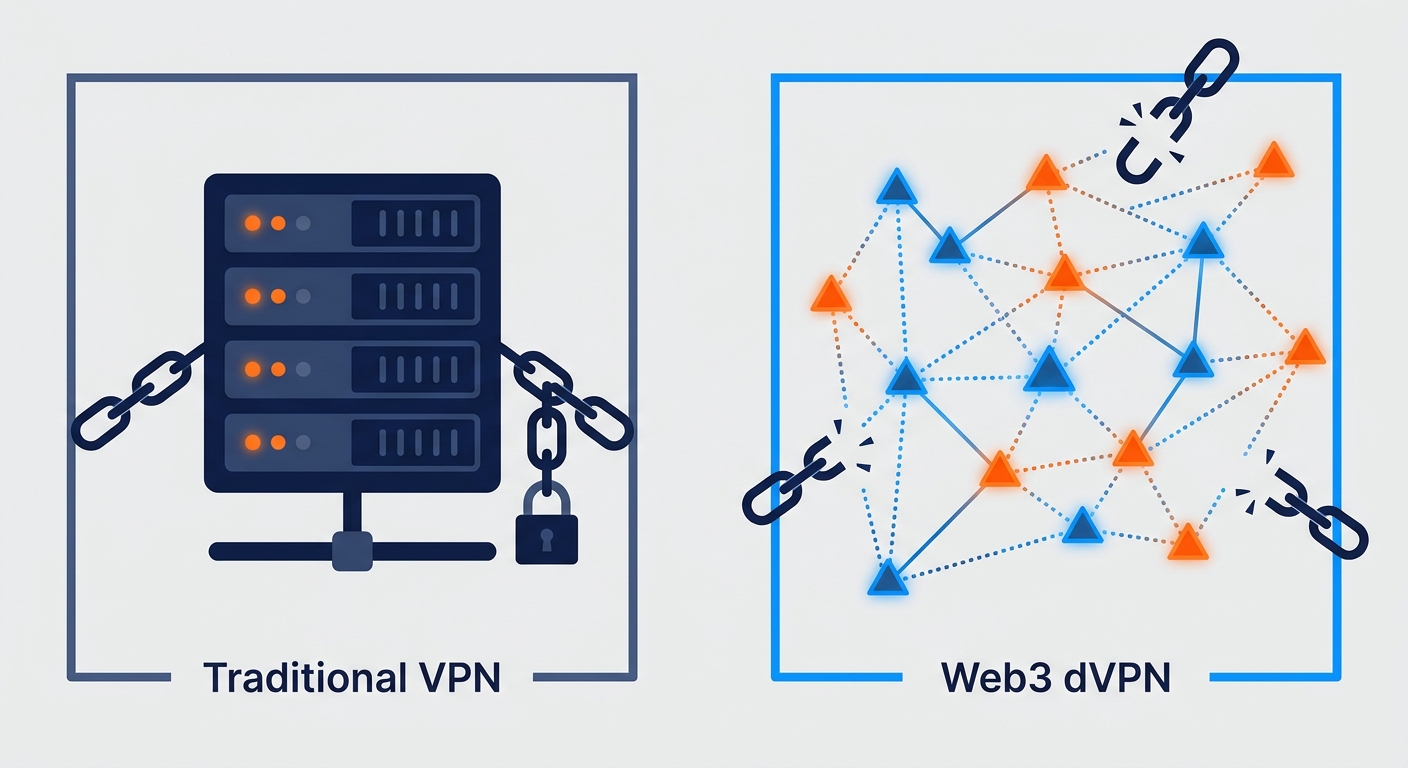
In the early days of p2p networks, things were pretty simple—maybe too simple. You’d share a bit of data and get a token. But that led to "quantity over quality" problems where people would game the system with low-quality connections.
- Early failures: Just rewarding "uptime" meant people ran nodes on terrible connections that didn't actually help the network. This made services like decentralized vpns laggy and unreliable for real users.
- Rewarding Quality: Now, we’re seeing a shift toward resource-weighting. This means the network checks your speed, latency, and geographic location before deciding your payout.
- Stopping Sybil Attacks: By requiring "proof of contribution," it’s much harder for someone to fake a thousand fake nodes on a single server. This works by having the network actively verify data packets or actual bandwidth throughput to make sure the node is physically active and not just a script. According to 2024 market data from Messari, the depin sector has reached a market cap of around $20 billion, with a total addressable market (TAM) projected to hit trillions as these incentive models get smarter.
Think of it like renting out a spare room, but for your data. You aren't using all your gigabits while you're at work, so why not let the mesh network use it?
This works across industries too. A retail chain might use decentralized bandwidth to securely sync inventory without paying an isp for a dedicated line. Or a healthcare clinic could use it to move large imaging files privately. It’s all about making the internet more of a commodity exchange and less of a closed monopoly.
Next, we'll look at how these tokens actually get their value in a crowded market.
Core Components of Resource-Weighted Tokenomics
Ever think about why a 5G node in downtown Tokyo might be worth more to a network than a DSL connection in rural Wyoming? It isn't just about snobbery; it’s about where the data actually needs to go to keep the gears of the internet turning.
In a resource-weighted setup, not all megabits are created equal. The system uses a few "multipliers" to figure out who gets the biggest slice of the token pie.
- Latency and Ping: If you’re providing bandwidth for a high-frequency trading firm or a telehealth surgery suite, every millisecond matters. Nodes with lower latency get a higher "weight," meaning they earn more tokens for the same amount of data moved compared to a laggy connection.
- Uptime and Reputation: Consistency is king. A node that flickers on and off is useless for a retail chain trying to sync global inventory. Networks track your "reputation score" over time; the longer you stay stable, the better your payout multiplier becomes.
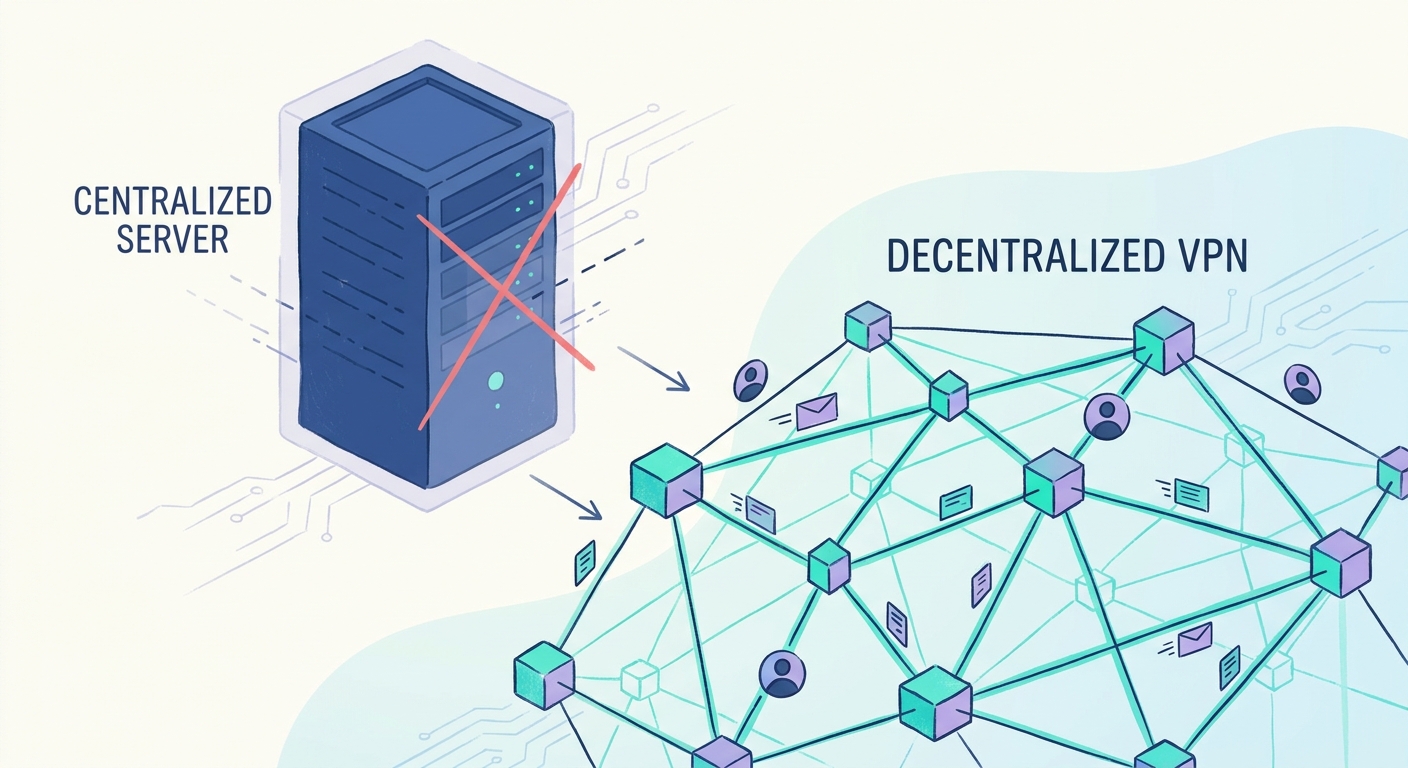
- Geographic Scarcity: This is basically supply and demand. If a decentralized vpn has a thousand nodes in London but only two in Lagos, those Lagos nodes are going to earn a premium because they’re providing a rare resource.
According to DePIN Hub, geographic distribution is becoming a critical metric for network health, as it ensures censorship resistance and better edge computing performance for global users.
So, how does the network know you aren't lying about your speed? This is where the "proof" part comes in. It’s a bit like a digital audit that happens in the background without snooping on what’s actually inside the data packets.
These protocols use cryptographic "heartbeats" to verify that a node is actually capable of the speeds it claims. It’s a way to ensure corporate data compliance—like making sure a healthcare provider's records are moving through a pipe that’s actually secure and fast enough—without a centralized ceo having to oversee every single transaction.
Next, we’ll dive into how these rewards actually hit your wallet and what keeps the token price from crashing.
Economic Sustainability of dVPN Ecosystems
So, you’ve got a network where anyone can join, but how do you stop it from collapsing under its own weight? It's one thing to launch a token, but quite another to make sure it actually has value six months later when the initial hype dies down.
Most dVPN projects fail because they just print tokens to reward nodes without any real "buy-side" pressure. A sustainable system needs a burn and mint equilibrium. This means when a user pays for a private connection to bypass local censorship, a portion of those tokens are "burned" or removed from circulation.
- Dynamic Pricing: If a network like SquirrelVPN sees a spike in demand because of new privacy trends or a sudden regional blackout, the cost to use the network should adjust. This keeps the rewards high enough to attract new nodes exactly where they're needed most.
- Incentivizing the Gaps: We need more than just nodes in New Jersey. By offering higher "multipliers" in under-served regions, the network grows its global footprint. This makes the service more valuable to corporate clients who need diverse ip addresses for market research or data compliance.
- Enterprise Buy-in: When a retail chain uses the network to sync inventory across a thousand stores, they provide the "real" capital that backs the token value. It moves the ecosystem from a speculative circular economy to a legitimate utility.
You can't just let anyone route sensitive data without some skin in the game. That’s where staking comes in. To become a verified provider, you usually have to lock up a certain amount of the network's native tokens.
- Security Deposit: Think of staking as a security deposit for your apartment. It proves you’re serious about providing a quality service and aren't just there to sybil attack the system.
- The Slashing Penalty: If your node goes offline during a critical transfer or fails a "heartbeat" check, the network "slashes" your stake. You lose your money. This automated policing is what keeps the network honest. Note that slashing usually targets uptime issues, since inspecting encrypted traffic for "malicious code" is technically impossible without breaking the privacy of the dvpn.
According to research by Messari, the depin sector is shifting toward these "hardware-backed" staking models because they provide a much higher floor for token value compared to purely digital assets. It’s about building a physical moat that’s hard to fake.
Next, we’ll look at the future landscape of this tech and how it might integrate into our daily lives.
Future Outlook for Tokenized Internet Infrastructure
So, where is all this actually heading? We’re moving toward an internet where the infrastructure isn't just something you buy from a giant isp, but something we all essentially "own" and maintain through our own hardware.
The real shift happens when this tech gets baked into stuff we already use. Imagine your smart fridge or a mesh router coming out of the box with a "earn while you sleep" toggle. It sounds futuristic, but as 5G rollouts continue, the demand for local "edge" nodes is exploding. According to a 2024 analysis by CoinGecko, the depin sector is one of the fastest-growing niches because it bridges the gap between digital tokens and physical utility.
- IoT Integration: Future routers won't just provide wifi; they'll act as encrypted gateways for nearby devices, earning tokens by securing traffic for everything from a neighbor's smart lock to a local delivery drone.
- Regulatory Hurdles: We can't ignore the legal side. Some jurisdictions are still fuzzy on whether sharing your bandwidth makes you an "internet service provider" in the eyes of the law. This is where privacy-preserving protocols like zero-knowledge proofs or traffic obfuscation act as a shield—since the node owner can't see the traffic, they can't be held responsible for the content.
- 5G and Beyond: High-speed mobile networks need way more "cells" than 4G did. Instead of telcos building a tower on every corner, they might just pay you to host a small 5G node in your window.
In the finance world, a hedge fund might use a decentralized network to scrape global pricing data without getting blocked by regional firewalls. Meanwhile, a hospital could use a p2p tunnel to send encrypted patient records between branches, ensuring they meet strict data compliance rules without relying on a single point of failure.
Honestly, the "airbnb for bandwidth" model is just the start. As ai and edge computing demand more juice, your idle home connection might just become your most valuable digital asset. It’s a messy, exciting transition, but the days of "wasteful" bandwidth are definitely numbered.