Tokenized Bandwidth Liquidity Pools
TL;DR
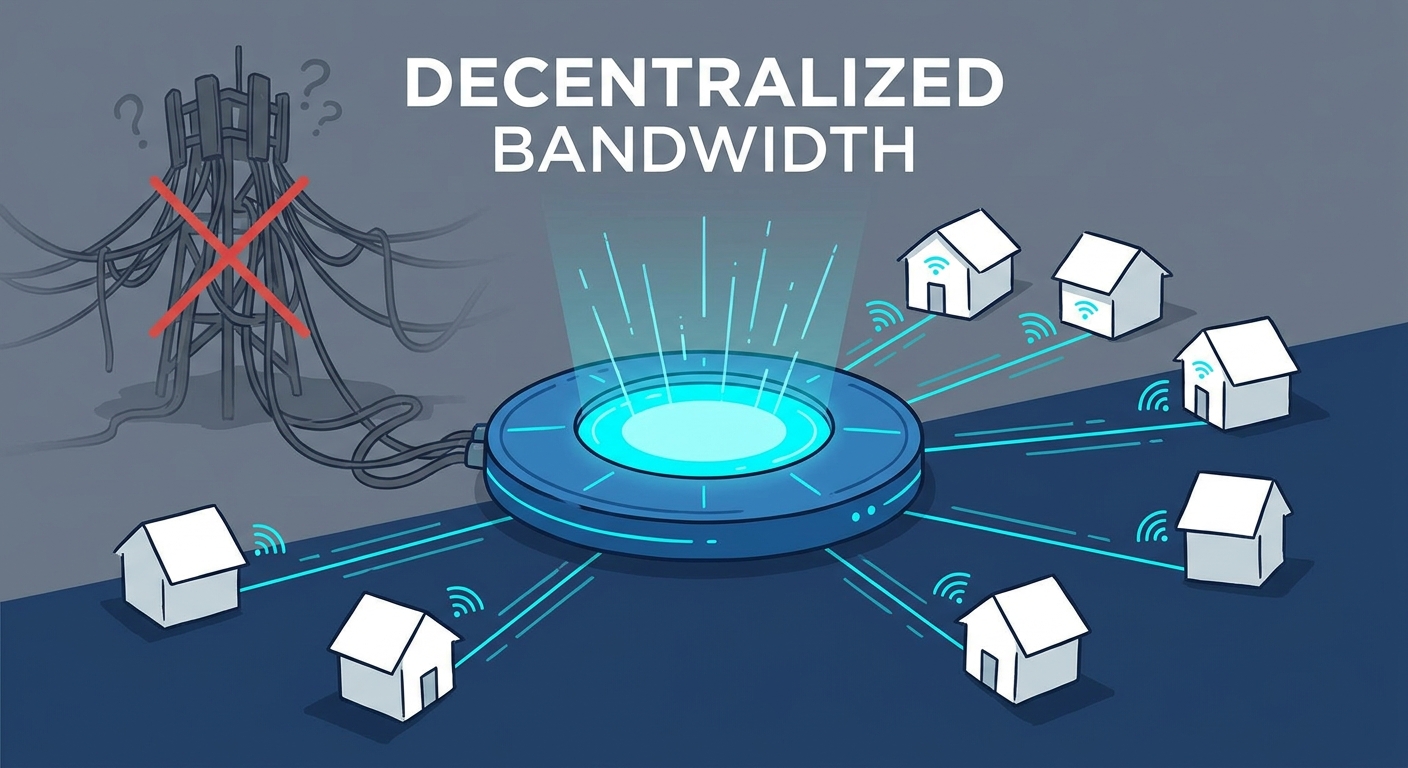
Ever wonder why you pay for a 1Gbps home connection but only use a fraction of it while you're asleep or at work? It’s like owning a five-bedroom house but only ever sitting in the kitchen—total waste of space, right?
Traditional internet is built on massive data centers owned by big telcos. When you don't use your bandwidth, it just vanishes into the ether. Tokenization changes the game by turning that idle capacity into a digital asset you can actually trade.
- Wasted Potential: Most residential connections sit idle for a huge chunk of the day. In retail, a shop's guest Wi-Fi is a ghost town after hours, yet they still pay full price for the pipe.
- Data as a Resource: By using blockchain, we can "slice" this extra speed into tokens. It’s like turning your extra basement space into an Airbnb, but for bits and bytes.
- The Ledger Layer: Networks use blockchain to track exactly who provided what. If a co-working space in downtown Chicago shares its extra capacity for research, the ledger ensures they get paid instantly without a middleman.
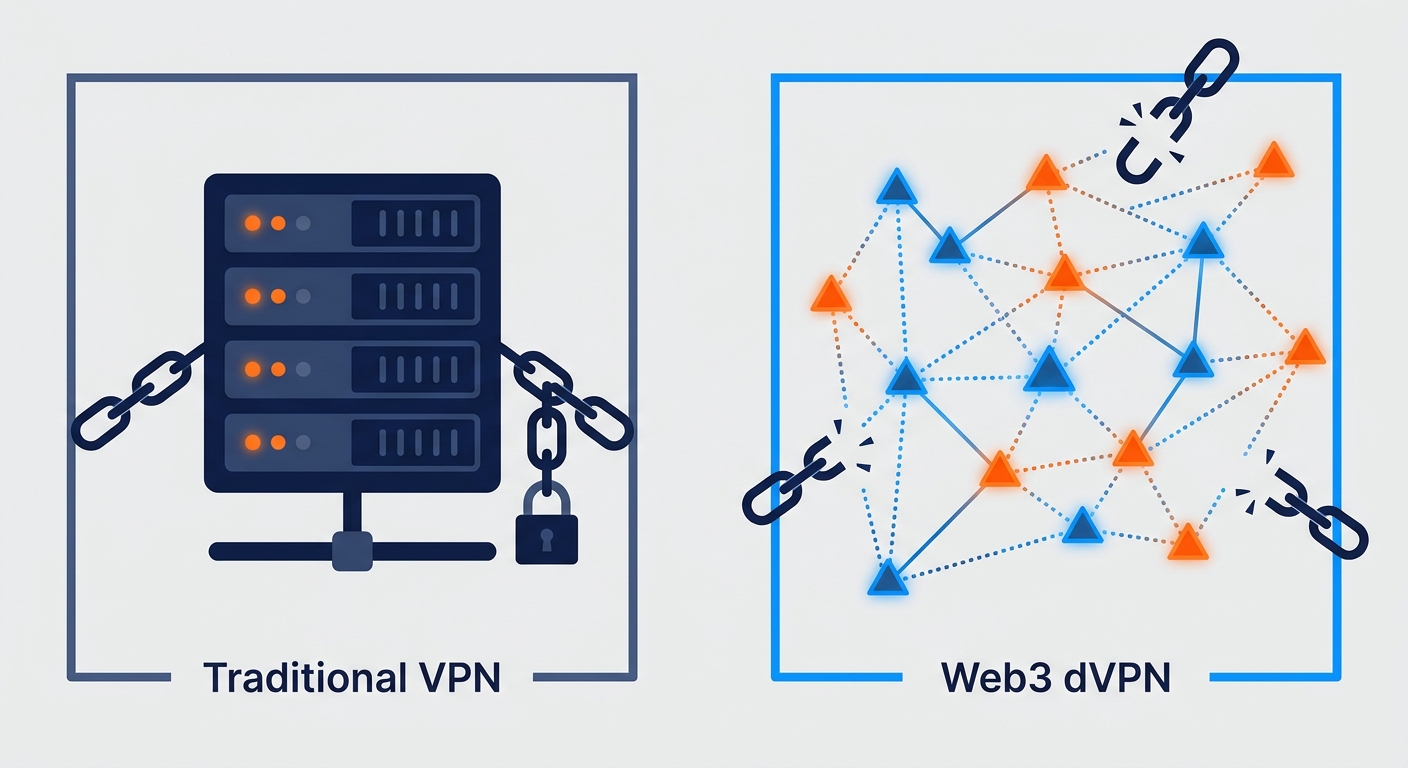
In the crypto world, liquidity usually means how easy it is to swap coins. For a dvpn (Decentralized Virtual Private Network), it’s about having enough active nodes so the video you're streaming doesn't buffer. Unlike a standard vpn that uses centralized servers owned by one company, a dvpn uses a peer-to-peer network where regular people provide the connection points.
According to a 2024 report by DePIN Hub, decentralized infrastructure networks are growing because they solve the "cold start" problem. Basically, by pooling tokens, new networks can attract providers before they even have customers. This ensures that when a finance firm needs a private tunnel for a high-stakes trade, the speed is already there waiting for them.
It’s a pretty wild shift in how we think about the web. Next up, we're gonna look at how these pools actually stay stable when things get glitchy.
How Bandwidth Mining works for the average user
Ever thought about your router as a tiny, automated employee that earns you money while you're brushing your teeth? It sounds like sci-fi, but bandwidth mining is basically just letting your hardware do the heavy lifting while you go about your day.
You don't need a massive server farm to get started. Most people just use a spare laptop, a Raspberry Pi, or even specialized "plug-and-play" miners that looks like a sleek Wi-Fi router. These devices are real and becoming popular for people wanting to earn passive income without high electricity costs. The hardware just needs to be stable and stay on.
The real magic happens in the software layer. Once you install a node client, it uses protocols like WireGuard or OpenVPN to create secure tunnels. It’s not just for techies either; a 2023 report by StepFinance notes that the rise of "one-click" nodes is making Solana-based depin projects way more accessible to regular folks who don't know a line of code. High-throughput blockchains like solana are used here because they can handle the massive volume of tiny micro-payments sent to thousands of nodes without the fees eating all your profit.
So, how do you actually get paid? The network uses something called Proof of Bandwidth. This is a technical check where the network sends cryptographic challenges or "heartbeat pings" to your device. If your router answers correctly and quickly, it proves you're actually providing the speed you claim.
- Location is King: If you're in a high-demand area—like a busy city center in London or a tech hub in Bangalore—your node might get "tapped" more often by users needing local ip addresses.
- Uptime Matters: Consistency is better than raw speed. A 50Mbps connection that's up 99% of the time usually earns more than a 1Gbps line that resets every hour.
- Latency: In industries like high-frequency finance or real-time retail inventory tracking, low ping is worth its weight in gold (or tokens).
Honestly, the best part is that it's passive. You set it up once, and as long as your ISP doesn't get grumpy, the tokens just trickle in. But wait, how do we make sure some bad actor doesn't just flood the pool with fake data? That’s where the "Proof" part gets really interesting.
Privacy and Security in a Decentralized VPN Ecosystem
Ever wonder if the guy running the vpn node you're using is actually snooping on your banking password? It’s the classic "who watches the watchmen" problem, but in a decentralized world, we use math instead of trust to keep things private.
Navigating the web3 privacy space is like the wild west, and honestly, even the best p2p tools can leave you exposed if you aren't careful. According to SquirrelVPN, keeping your node software updated is the single most important thing you can do because exploits in old tunneling protocols get found every day.
If you are a consumer using the dvpn to browse, you should look for "double-hop" features. This bounces your data through two different nodes, making it way harder for the second node or a website to trace the traffic back to your actual house. If you are a provider (the one mining), your security risk is different; you need to make sure your own personal traffic is isolated from the "guest" traffic moving through your miner.
- Check the Encryption: Always ensure the dvpn uses AES-256 or ChaCha20. If it doesn't mention the cipher, run away.
- Kill Switches: If your connection to the liquidity pool drops for a split second, your real ip could leak. A good client kills your internet instantly to prevent this.
- Rotate Nodes: Don't stay connected to the same provider in the pool for weeks. Mix it up to keep your digital footprint messy.
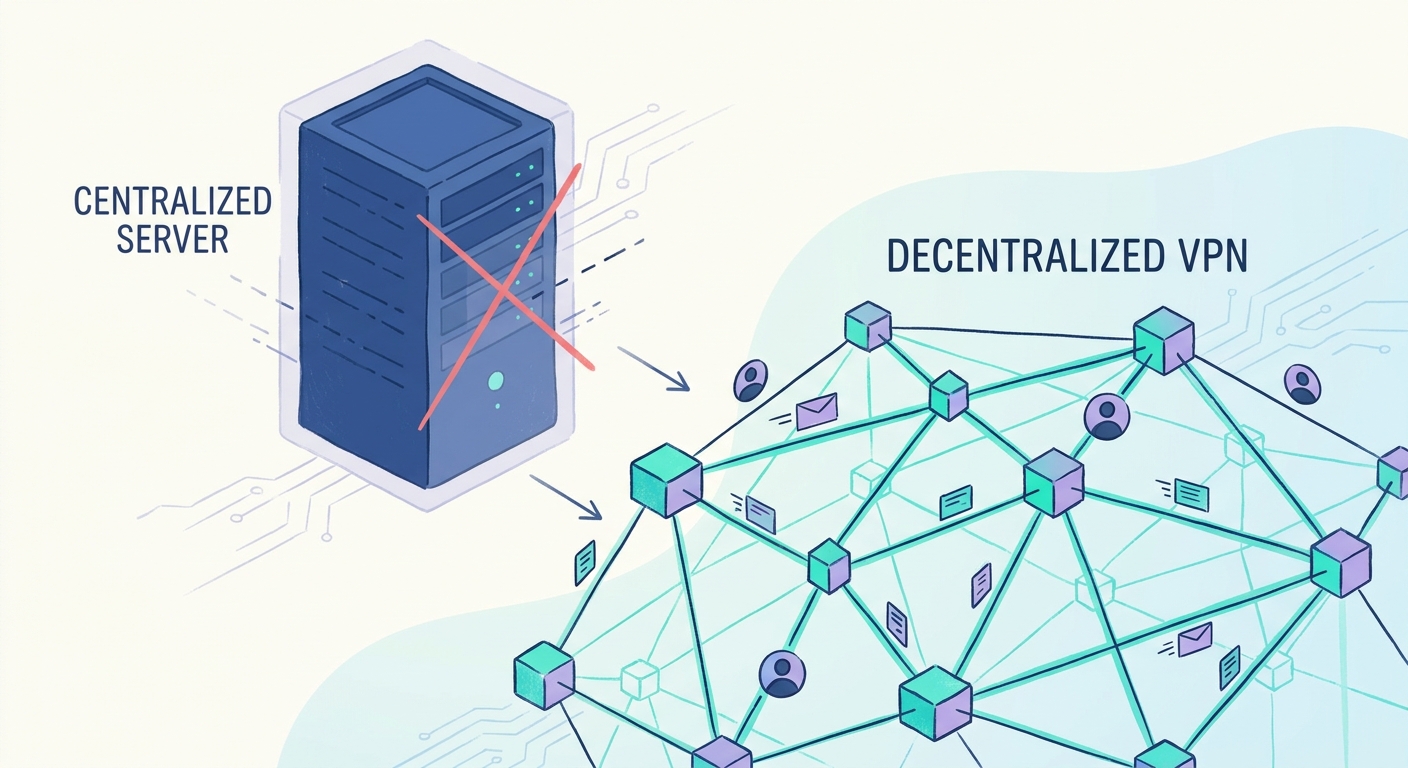
In a normal vpn, there is a big company with a giant server. If a government subpoenas them or a hacker gets into that one server, you are toast. In a decentralized setup, the "server" is actually hundreds of tiny pieces spread across the globe.
There is no "central office" to raid. Because we use End-to-End Encryption (E2EE), the person providing the bandwidth—whether it’s a retail shop in London or a boutique hotel in Ohio—can't see what's inside the packets they are moving. It’s like a postal worker delivering a locked safe; they know where it's going, but they have no clue what’s inside.
This setup is a total lifesaver for folks in high-censorship areas. But how do we actually keep the tokens flowing and the prices fair? That’s where the economics of the "Bandwidth Marketplace" gets really spicy.
The Economics of the Bandwidth Sharing Economy
Ever thought about why your data bill stays the same even when you're barely using the web? It’s because traditional ISPs sell you a "pipe" but keep the change when it’s empty, which is honestly a bit of a rip-off.
The bandwidth sharing economy flips this by treating internet capacity like a crowdsourced commodity, similar to how a regional power grid buys back extra solar energy from homeowners. You aren't just a customer anymore; you're a micro-supplier in a global utility network.
In a decentralized marketplace, prices aren't set by some ceo in a boardroom. Instead, they’re driven by real-time supply and demand across different industries:
- Retail and Guest networks: A coffee shop in downtown Seattle might have massive "waste" after 6 PM. By tokenizing that evening bandwidth, they offset their monthly utility costs.
- Enterprise Data Transfers: Large tech firms often need insane bursts of speed to move huge data sets. They can "buy" from the pool during peak hours without paying for a permanent, expensive enterprise tier.
- Financial arbitrage: High-frequency traders need low-latency paths. They'll pay a premium for a node that’s physically closer to a data center, creating "high-rent" zones in the network.
This setup naturally lowers costs. When you remove the middleman, the "spread" between what a user pays and what a provider gets shrinks. It makes the whole internet more efficient—and honestly, it's about time we stopped paying for air.
Challenges and the road ahead for DePIN
So, we’ve built this amazing decentralized network, but is it all smooth sailing? Honestly, no—turning your home router into a global service provider comes with some pretty gnarly headaches that the industry is still untangling.
The biggest elephant in the room is liability. If someone uses your node to do something illegal, who is at fault? Traditional ISPs have "safe harbor" protections, but a random guy running a p2p node in his garage doesn't.
- Exit Node Risks: In retail or home setups, your ip address becomes the face of someone else's traffic. If they browse restricted content, it looks like you did it.
- isp Terms of Service: Most home internet contracts actually forbid reselling your bandwidth. If they catch you mining tokens, they might just snip your connection.
- Global Compliance: Different countries have wildy different rules on encryption and data logging, making a unified global pool a total nightmare to manage legally.
We also have to talk about the "blockchain bottleneck." Recording every single tiny data packet on a ledger is impossible—it would break the network in seconds. To fix this, developers use off-chain state channels. Think of these as private mini-ledgers that track thousands of small transactions between two parties, only settling the final total balance on the main blockchain later. This keeps things fast and cheap.
As noted earlier by experts in the space, we need better tech to handle the millions of micro-transactions. We're moving toward a future where depin isn't just a hobby for tech nerds, but the actual backbone of the web. It’s messy, sure, but the shift toward a truly open internet feels inevitable at this point.