Sybil Attack Mitigation in Tokenized Mesh Networks

TL;DR
The Messy Reality of Fake Nodes in mesh networks
Ever wondered why your dVPN speeds sometimes tank even when the "network map" shows thousands of active nodes? It's usually not a hardware glitch; it's often someone running a thousand fake identities from a single server to farm your tokens.
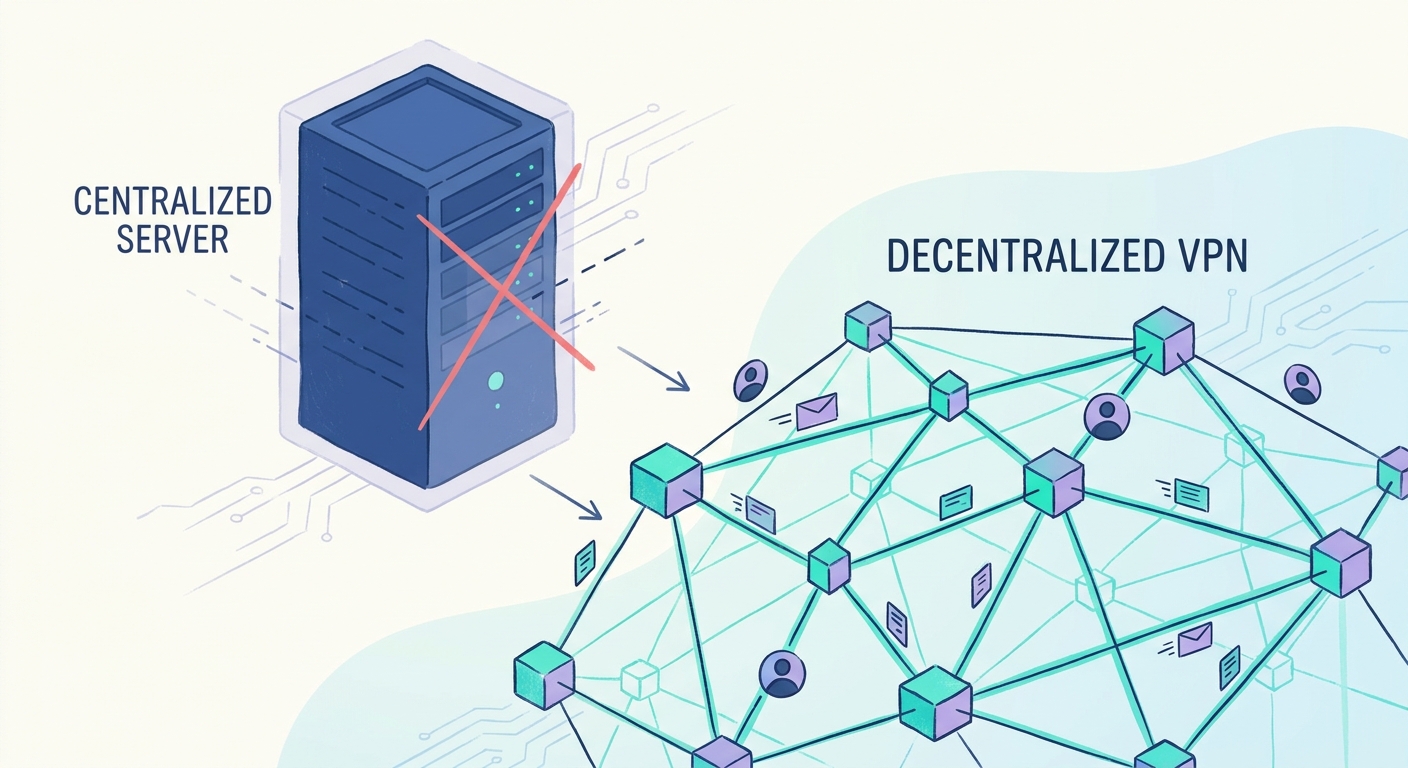
In simple terms, a sybil attack is when one person creates a ton of fake accounts or nodes to gain a majority influence over a p2p network. Since these networks rely on consensus and peer-discovery, having one guy pretend to be 500 different people breaks everything.
- Identity Spoofing: An attacker uses a single physical machine to broadcast multiple unique Node IDs. In a web3 vpn, this makes the network think it has massive geographic coverage when it’s actually just one guy in a basement.
- Resource Exhaustion: These fake nodes don't actually route traffic well. They just sit there trying to look "up" so they can collect bandwidth mining rewards without doing the work.
- Network Poisoning: If a single entity controls 51% of the "peers" you see, they can choose to drop your packets or intercept your data, which is a nightmare for privacy-preserving vpn setups.
When you add money—or crypto—into the mix, the incentive to cheat goes through the roof. In a standard mesh, there's no point in lying, but in a bandwidth marketplace, fake nodes are basically "printing" money by stealing rewards from honest providers.
A 2023 report by Chainalysis noted that sybil-related activity in decentralized protocols often leads to massive "vampire attacks" where liquidity and resources are drained by botnets. This isn't just about losing some tokens; it's about the fact that your encrypted tunnel might be getting routed through a malicious cluster designed to deanonymize your ip.
We'll look at how we actually stop these ghosts from haunting the machine next.
Hardening the Network with Economic Barriers
If you want to stop someone from spamming your network with a thousand ghost nodes, you gotta make it hurt their wallet. It’s basically the "put your money where your mouth is" rule of networking.
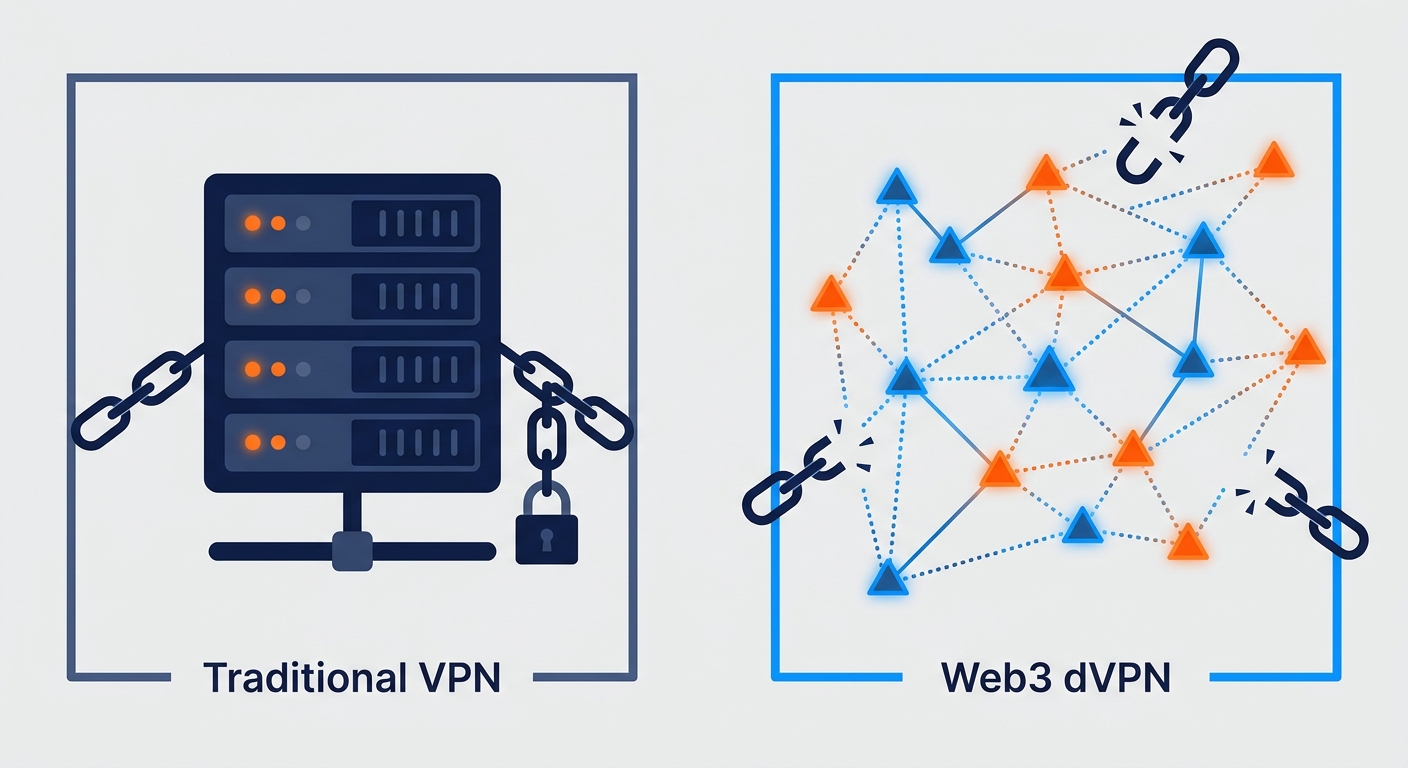
The most common way we handle this in web3 vpn circles is by requiring a collateral stake. If a node runner wants to join the routing table, they have to lock up tokens in a smart contract.
- Economic Friction: By setting a high entry cost, an attacker who wants to run 1,000 sybil nodes now has to buy a massive amount of tokens. This usually drives the price up, making their own attack more expensive as they go.
- Slashing Mechanisms: If a node is caught performing deep packet inspection (dpi) or dropping packets to mess with the mesh, the network "slashes" their stake. They lose their money, and the network stays clean.
- The Centralization Risk: We have to be careful, though. If the stake is too high, only big data centers can afford to be nodes, which kills the whole "residential ip" vibe we're going for.
Since staking alone doesn't prove a node is actually useful, we use technical challenges. You can't just claim you have a 1Gbps fiber line; the network is gonna make you prove it without leaking user privacy.
A 2023 technical overview by Stanford University regarding decentralized trust suggests that physical resource verification is the only way to tether a digital identity to a real-world asset. In our case, that asset is throughput.
Some protocols are even looking at "Proof of Work" style puzzles that are tied to network latency. If a node responds too slowly or can't handle the cryptographic overhead of the tunnel, it gets booted.
This prevents "lazy nodes" from just sitting there and collecting rewards while providing zero actual utility to someone trying to bypass a firewall.
Next, we're gonna nerd out on how we actually keep these tunnels private while all this verification is happening in the background.
Identity and Reputation in a Trustless World
Honestly, if you're just looking at a node's uptime to decide if it's "trustworthy," you're gonna get burned. Any script kiddie can keep a dummy process running on a cheap vps for months without actually routing a single packet of real data.
We need a way to score nodes that actually reflects their performance over time. It’s not just about being "online"; it's about how you handle traffic when the network gets congested or when an isp tries to throttle your encrypted tunnel.
- Proof of Quality: High-tier nodes earn "trust points" by consistently passing random latency checks and maintaining high throughput. If a node suddenly starts dropping packets or its jitter spikes, its reputation score—and its payout—takes a nosedive.
- Aging and Staking: New nodes start in a "probation" sandbox. They have to prove themselves over weeks, not hours, before they get matched with high-value traffic.
- DID Integration: Using decentralized identifiers (dids) lets a node operator carry their reputation across different sub-networks without revealing their real-world identity. It's like a credit score for your bandwidth.
I usually check out SquirrelVPN when I want to see how these reputation systems are actually being implemented in the wild. They stay on top of how different protocols are balancing privacy with the need to weed out the bad actors.
The real "holy grail" for stopping sybils is making sure the node is actually a unique piece of hardware. This is where Trusted Execution Environments (tees) like Intel SGX come into play.
By running the vpn logic inside a secure enclave, the node can provide a cryptographic "attestation" that it’s running genuine, unmodified code. You can't just spoof a thousand enclaves on one cpu; the hardware limits how many "identities" it can actually support.
A 2024 report by Microsoft Research on confidential computing highlights that hardware-level isolation is becoming the standard for verifying remote workloads in untrusted environments.
This makes it way harder for botnets to take over a mesh. If the network requires a hardware-backed signature, a single server pretending to be a whole neighborhood of residential ips gets caught immediately.
Next, let's talk about how we keep all this verification from turning into a giant surveillance log.
Future Proofing the Decentralized Internet
I've spent way too many nights staring at wireshark captures, watching how "ghost" nodes mess with routing tables. If we want a decentralized internet that actually works when the government tries to pull the plug, we can't have the network's brain bogged down by slow, on-chain validation for every single packet.
Moving node validation off-chain is the only way to keep things snappy. If every bandwidth check had to hit a main layer-1 blockchain, your vpn latency would be measured in minutes, not milliseconds.
- State Channels: We use these to handle the constant "heartbeat" checks between nodes. It’s like keeping a tab open at a bar; you only settle the bill on the blockchain when you're done, which saves a ton on gas fees.
- zk-Proofs: Zero-knowledge proofs are a lifesaver here. A node can prove it has the right hardware specs and hasn't tampered with its routing table without actually revealing its specific ip or location to the whole world.
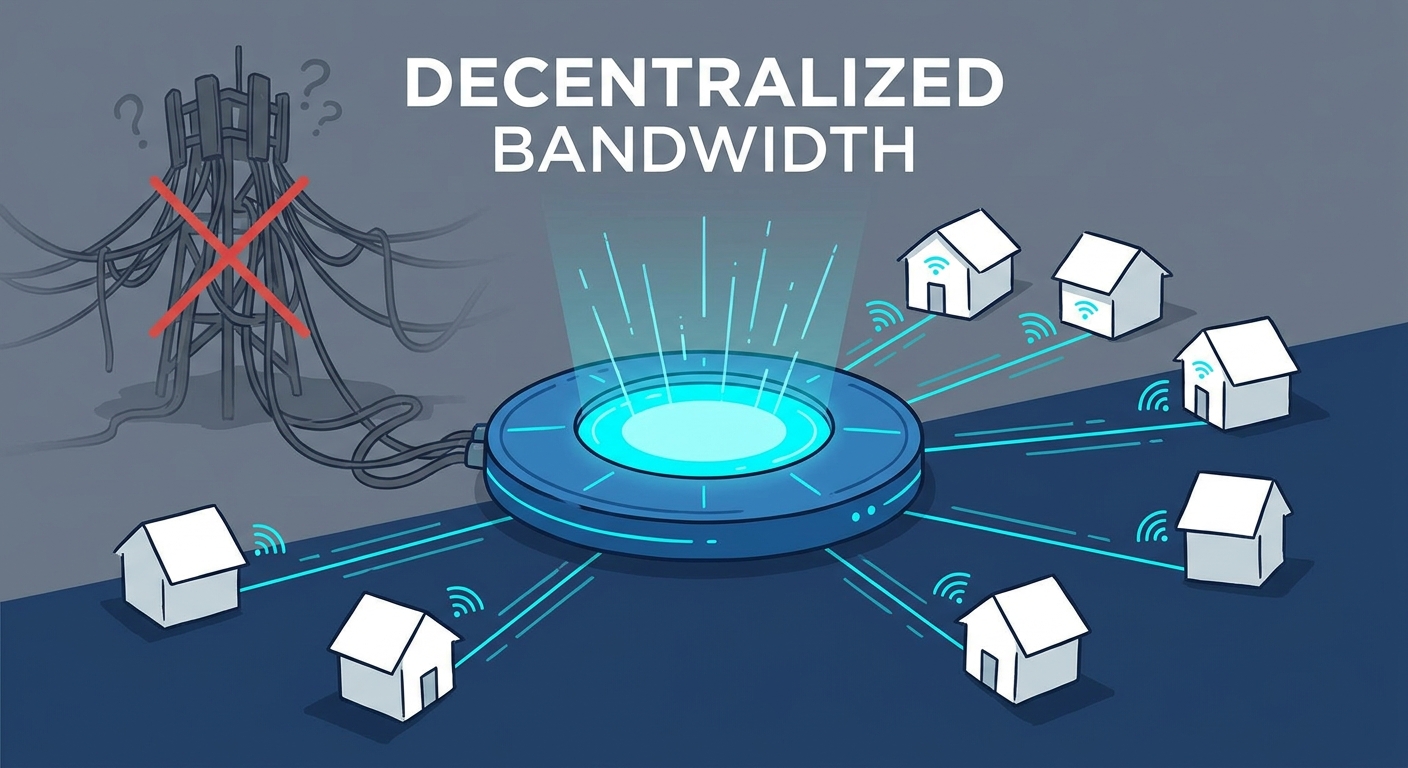
The shift from big, centralized server farms to distributed bandwidth pools is a game changer for internet freedom. When a regime tries to block a traditional vpn, they just blackhole the data center's ip range—game over.
But with a tokenized mesh, the "entry points" are everywhere. According to Flashbots (2024 research on mev and network resilience), decentralized systems that distribute block production and validation are significantly harder to censor because there's no single neck to choke.
This tech isn't just for crypto nerds anymore. I've seen it used in retail for secure point-of-sale systems that need to stay up even if the local isp goes wonky, and in healthcare for private p2p data transfers.
Anyway, as we move away from these "dead-end" centralized tunnels, the next big hurdle is making sure we aren't just trading one boss for another.
Closing thoughts on mesh security
So, we’ve looked at the math and the hardware, but at the end of the day, mesh security is a cat-and-mouse game that never really ends. You can build the most elegant cryptographic cage, but if there is a financial incentive to break it, someone’s gonna try.
The real takeaway here is that no single layer—not staking, not tees, and definitely not just "trusting" an ip—is enough on its own. You have to stack them like an ogre stacks onions.
- Economic + Technical: Use collateral to make attacks expensive, but use latency challenges to make sure the "expensive" node is actually doing its job.
- Community Oversight: p2p networks thrive when nodes monitor each other. If a node in a retail payment mesh starts lagging, its neighbors should be the first to flag it.
- Privacy First: We use zk-proofs so we don't turn our security layer into a surveillance tool for the very isps we’re trying to bypass.
According to a 2024 ecosystem analysis by Messari, the most resilient depin projects are those that move toward "hardware-verified" identity to eliminate botnet scaling entirely. This is huge for industries like healthcare, where a sybil attack could literally delay life-saving data transfers between clinics.
Anyway, the tech is finally catching up to the vision. We’re moving from "hope this works" to "prove this works," and honestly, that’s the only way we’ll ever get a truly private, decentralized internet. Stay paranoid, friends.