Sybil Attack Mitigation in Distributed Node Networks
TL;DR
Understanding the Sybil Threat in Decentralized Ecosystems
Ever wonder how a single person can look like a thousand different people online? It’s not just a plot for a sci-fi movie; in the world of decentralized networks, it is a huge security headache known as a Sybil attack.
Named after a famous case of dissociative identity disorder, this threat is all about one bad actor spinning up a bunch of fake nodes to drown out the honest ones. Imagine trying to run a fair vote in a small town, but one guy shows up wearing 50 different hats and fake mustaches, claiming he’s 50 different citizens. That's basically what happens to a p2p network during a sybil event.
In a standard decentralized setup, we usually trust that "one node equals one vote" or one unit of influence. But since there isn't a central dmv or passport office to check id, an attacker can use a single computer to create thousands of digital aliases. According to Imperva, this lets them out-vote honest users and even refuse to transmit data blocks.
- Fake Identities: The attacker creates "sybil nodes" that look legit to the rest of the network.
- Network Influence: By controlling a majority of nodes, they can trigger a 51% attack—this is where the attacker owns more than half the network power, letting them reverse transactions or block others from doing anything.
- Resource Exhaustion: These fake nodes can clog up the bandwidth, making the decentralized internet slow and buggy for everyone else.
John R. Douceur, who first really dug into this at microsoft research, split these into two flavors. A direct attack is when the fake nodes talk straight to the honest ones. It's bold and fast. An indirect attack is sneakier; the attacker uses "proxy" nodes as a middleman to hide their influence.
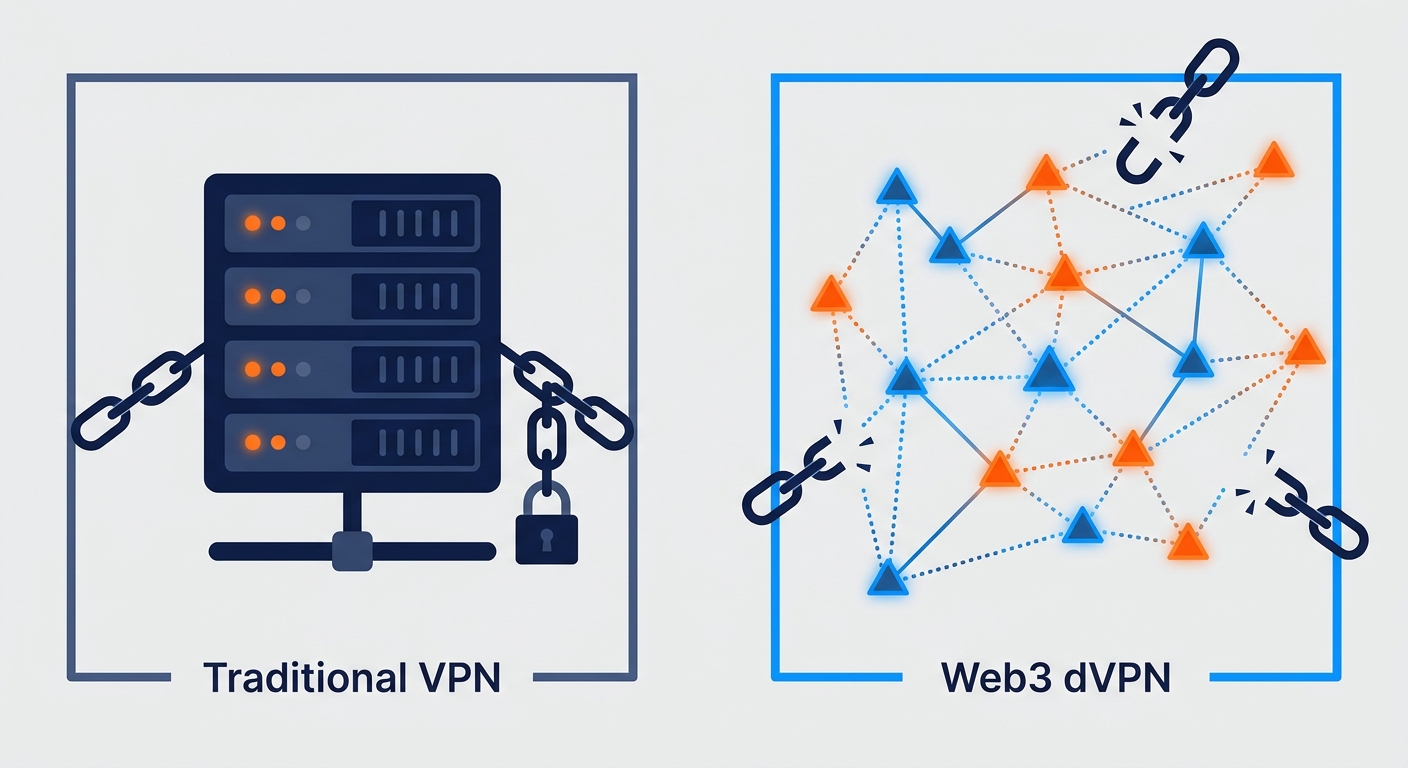
This is super dangerous for things like decentralized vpn services or p2p file sharing. If a hacker controls both the entry and exit points of your connection by using multiple fake identities, your privacy is basically toast.
Honestly, if we don't fix how we validate who is "real" without ruining anonymity, these networks won't ever be truly safe. Next, we're gonna look at how we actually start fighting back against these fake crowds.
Why dVPN and DePIN Networks Are Vulnerable
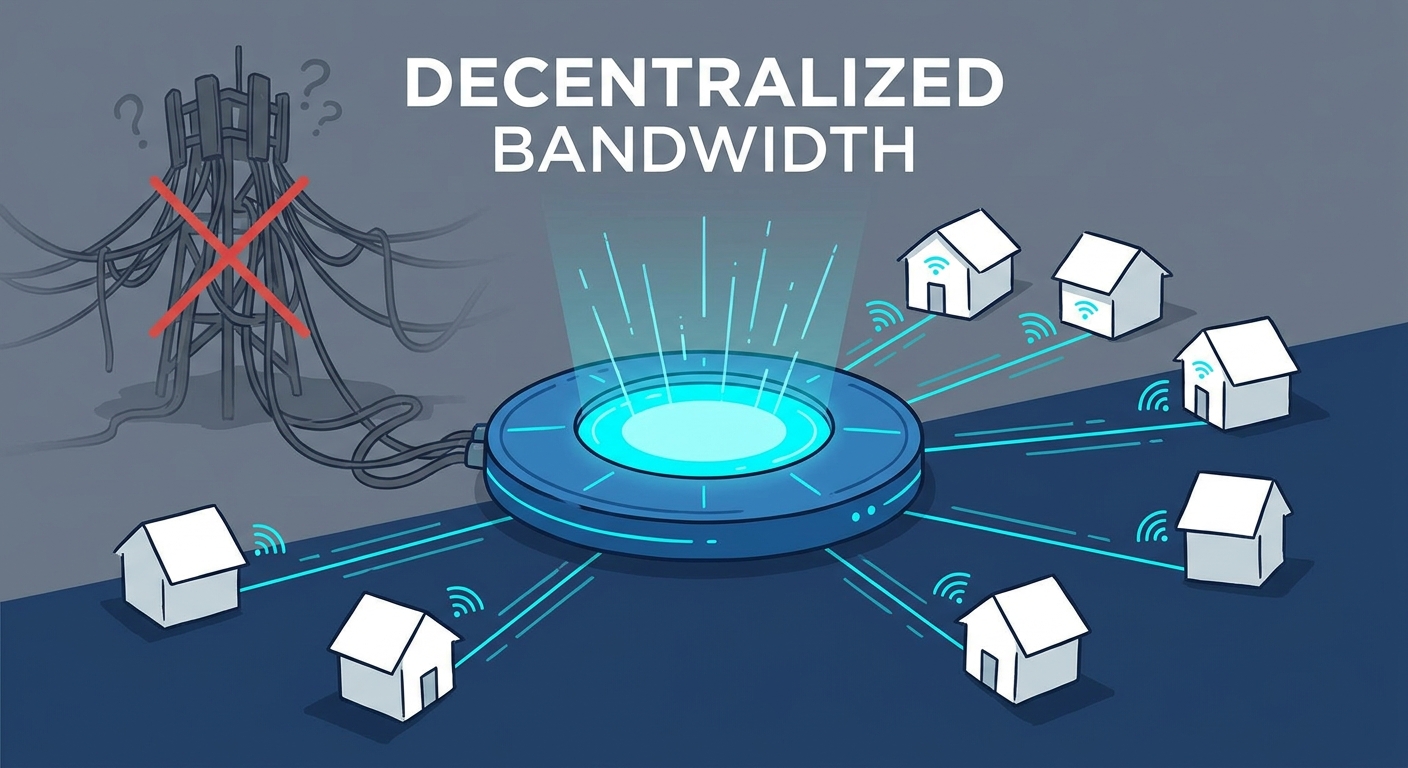
Actually, it is kind of wild when you think about it. We’re building these massive, global networks like dvpn and depin to take power away from big corporations, but that same "open door" policy is exactly what hackers love. If anyone can join, then anyone—including a botnet with ten thousand fake faces—can join too.
Building on the identity problem mentioned earlier, dVPNs face specific financial incentives that make them a prime target. Why would someone go through the trouble? Simple: rewards. Most depin networks use bandwidth mining to incentivize people to share their extra internet.
- Draining the Pool: In a bandwidth marketplace, sybil nodes can "fake" being active to suck up token rewards meant for real users.
- Bogus Data: Attackers can flood the network with fake traffic reports, making the p2p economy look way healthier (or busier) than it actually is just to spike their own earnings.
- Market Manipulation: By controlling a huge chunk of the "supply," a single bad actor can mess with the pricing of the entire marketplace.
It gets scarier when we talk about actual privacy. If you’re using a privacy-preserving vpn, you’re trusting that your data is bouncing through independent nodes. But what if those "independent" nodes are all owned by the same guy?
According to Hacken, if an attacker gains enough dominance, they can actually start censoring specific traffic or, even worse, unmasking users. If a hacker controls both where your data enters and where it exits the network, your "anonymous" session is basically an open book to them.
This isn't just theory, either. Back in 2014, the tor network—which is basically the grandfather of all p2p privacy tools—got hit by a massive sybil event where someone ran over 110 relays just to try and "de-cloak" users. Anyway, it's a constant cat-and-mouse game.
Mitigation Strategies for Distributed Networks
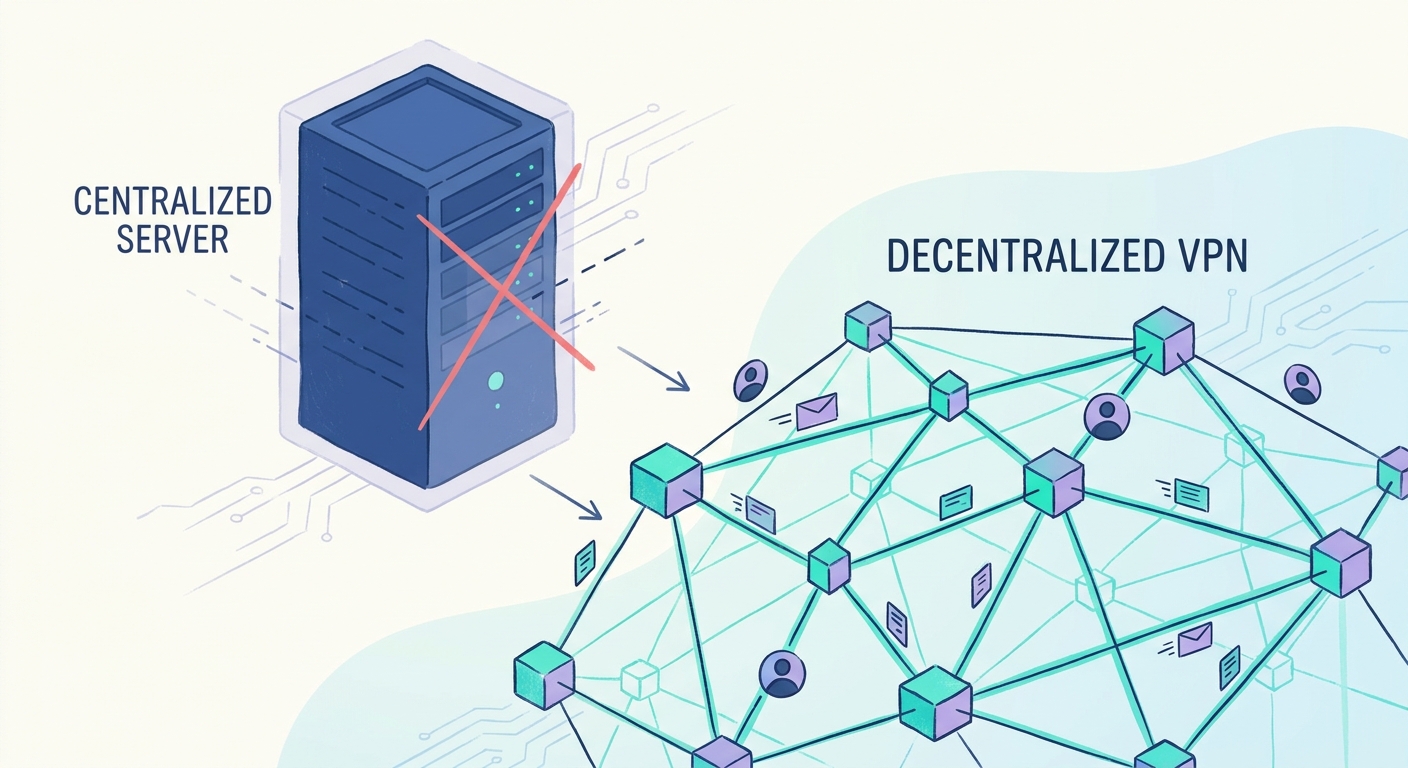
So, how do we actually stop these digital ghosts from taking over? It’s one thing to know a sybil attack is happening, but it's a whole other ballgame to build a "bouncer" for your network that doesn't ruin the whole point of being decentralized.
One of the oldest tricks in the book is just asking for an id. But in web3, that’s a bit of a dirty word. According to Nitish Balachandran and Sugata Sanyal (2012), identity validation usually falls into two buckets: direct and indirect. Direct is when a central authority checks you out, while indirect is more about "vouching." Basically, if three trusted nodes say you’re cool, the network lets you in.
If we can't check ids, we can at least check wallets. This is where things like Proof of Stake (PoS) and Staking come in. The idea is simple: make it expensive to be a jerk.
- Slashing: If a node is caught acting weird—like dropping packets or lying about data—the network "slashes" their stake. They lose their money.
- Bandwidth Proof Protocols: Some depin projects require you to prove you actually have the hardware. You can’t just simulate a thousand nodes on one laptop if the network demands a high-speed ping from each one.
Another way to fight back is by looking at the "shape" of how nodes connect. This is where research like SybilDefender comes in. SybilDefender is a defense mechanism that uses "random walks" on the network graph. It assumes that honest nodes are well-connected to each other, but sybil nodes are only connected to the rest of the world through a few "bridge" links created by the attacker.
Instead of just looking at individual IDs, we need to look at the structural and mathematical "shape" of the network to see if it's healthy. This leads us into the more advanced ways we map these connections.
Advanced Topological Defenses
Ever felt like you’re trying to find a needle in a haystack, but the needle keeps changing its shape? That is exactly what it feels like trying to spot sybil clusters using just basic math, which is why we have to look at the "shape" of the network itself.
The cool thing about honest users is that they usually form a "fast-mixing" bunch—meaning they connect to each other in a tight, predictable web. Attackers, however, are stuck behind a narrow bridge because it's actually hard to trick tons of real people into friending a bot.
- Connection Analysis: Algorithms look for parts of the graph that are "bottlenecked." If a huge group of nodes only talks to the rest of the world through one or two accounts, that’s a massive red flag.
- SybilLimit and SybilGuard: These tools use "random routes" to see if a path stays within a trusted circle or wanders off into a dark corner of the web.
- Scale Issues: Unlike the theoretical models where everyone is friends, real-world networks are messy. Online social behavior doesn't always follow a perfect "trust your friends" rule, so we have to get more aggressive with the math.
As mentioned earlier, SybilDefender performs these walks to see where they end up. If 2,000 walks from one node keep circling the same fifty accounts, you’ve probably found a sybil. A 2012 study by Wei Wei and researchers at the College of William and Mary proved this can be way more accurate than older methods, even on networks with millions of users. It basically spots the "dead ends" where an attacker is hiding.
I've seen this in action with node-based vpn setups. If a provider sees 500 new nodes pop up that only talk to each other, they use community detection to snip that "bridge" before the nodes can ruin the consensus.
The Future of Censorship-Resistant VPNs
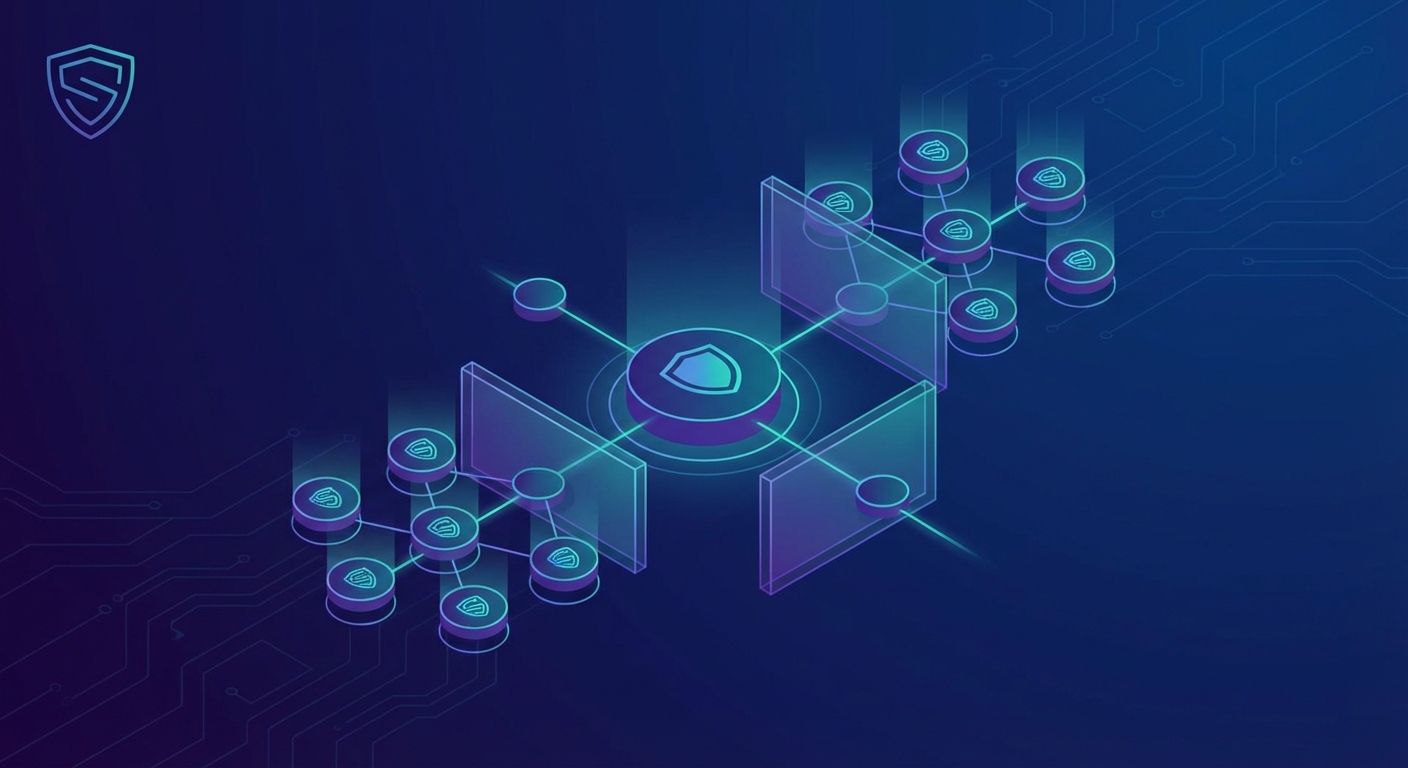
So, we’ve spent a lot of time talking about how fake nodes can wreck a network, but where is all this actually going? The reality is that building a truly censorship-resistant vpn isn’t just about better encryption anymore; it’s about making the network way too "heavy" for a liar to manipulate.
Generic security just doesn't cut it when you're dealing with a blockchain vpn. You need something more tailored. Specific protocols like Kademlia are being used because they make it naturally harder for an attacker to flood the system. Kademlia is a "Distributed Hash Table" (dht) that uses XOR-based routing. Basically, it uses a specific mathematical distance to organize nodes, which makes it really hard for an attacker to "position" their fake nodes strategically in the network without having very specific Node IDs that are hard to generate.
- DHT Resistance: Using Kademlia helps ensure that even if some nodes are sybils, the data stays reachable because the attacker can't easily predict where data will be stored.
- Privacy vs. Integrity: It's a tightrope walk. You want to stay anonymous, but the network needs to know you're a real human.
- Layered approach: I've seen projects try to rely on just one fix, and they always get burned. You need staking and topological checks.
Auditing the Defenses
How do we know if these "bouncers" are actually working? We can't just take the developers word for it.
- Third-Party Audits: Security firms now specialize in "Sybil-resistance audits" where they try to spin up botnets to see if the network catches them.
- Automated Stress-Testing: Many dvpn projects now run "Chaos Monkey" style tests, where they intentionally flood their own testnets with fake nodes to measure how much the performance drops.
- Open Metrics: Real networks should show "Node Age" and "Connection Density" stats so users can see if the network is made of long-term honest players or overnight botnets.
Honestly, the future of internet freedom depends on these depin networks getting their act together regarding sybil resistance. If we can't trust the nodes, we can't trust the privacy. At the end of the day, staying updated on cybersecurity trends in the bandwidth mining space is a full-time job. But if we get this right, we're looking at a decentralized web that nobody can shut down.