Recursive Zero-Knowledge Proofs for Private Tunneling
TL;DR
Wait, What Are Recursive Zero-Knowledge Proofs Anyway?
Ever wonder how you could prove to a friend you have the keys to a locked safe without actually showing them the keys or opening the door? It sounds like a magic trick, but in the world of cryptography, we call this a zero-knowledge proof (zkp).
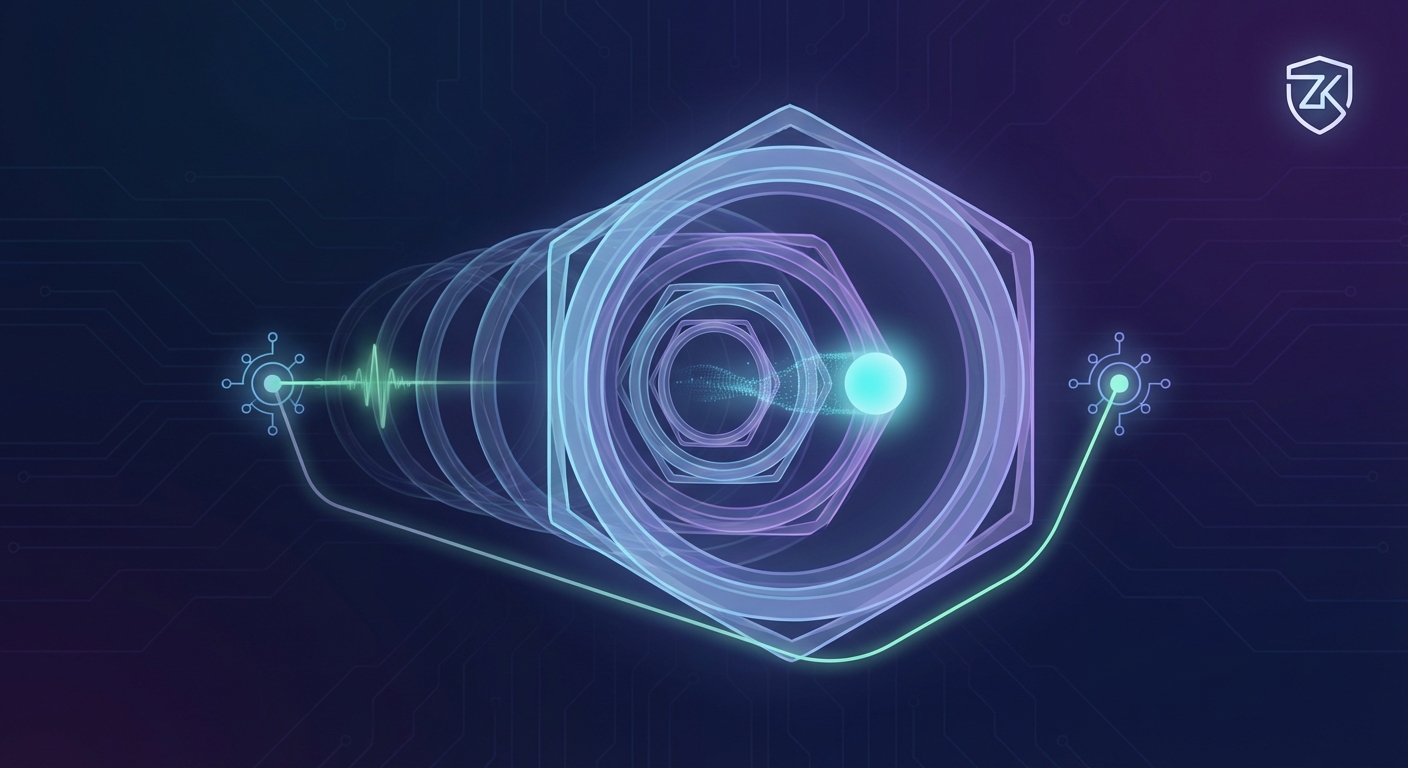
Honestly, the easiest way to wrap your head around recursive proofs is to imagine taking a selfie in a park today while holding a printed photo of yourself in that same park from yesterday. To prove you've been there all week, you just keep taking a new photo every day while holding the previous day's picture.
By day seven, that single final photo proves the whole week's history because it contains a "proof of a proof." According to sCrypt, this logic allows us to aggregate thousands of transactions—including complex "handshakes" between users—into one tiny, verifiable string.
- Knowledge without exposure: You prove you know a secret (like a vpn private key) without leaking a single bit of the actual data.
- Recursive nesting: A proof doesn't just verify data; it verifies that a previous verification was done correctly.
- Scaling the impossible: In finance, this means a bank could prove a million trades are valid without making the auditor check every single one.
Standard proofs are great, but they get "heavy" fast. As noted in research by Anoma, recomputing every state transition from a blockchain's genesis block is a nightmare for a mobile user.
Regular zk-snarks can get too big or slow for real-time private tunneling. (zk-SNARKs: From Scalability Issues to Innovative Solutions) If your dVPN had to generate a massive proof for every single packet, your internet speed would crawl. Recursive proofs fix this by "compressing" the truth.
And that's the kicker—it doesn't matter if you're proving one hour of data or ten years; the proof stays small. We're going to dive into how this actually builds a "private tunnel" next.
Private Tunneling and the dVPN Revolution
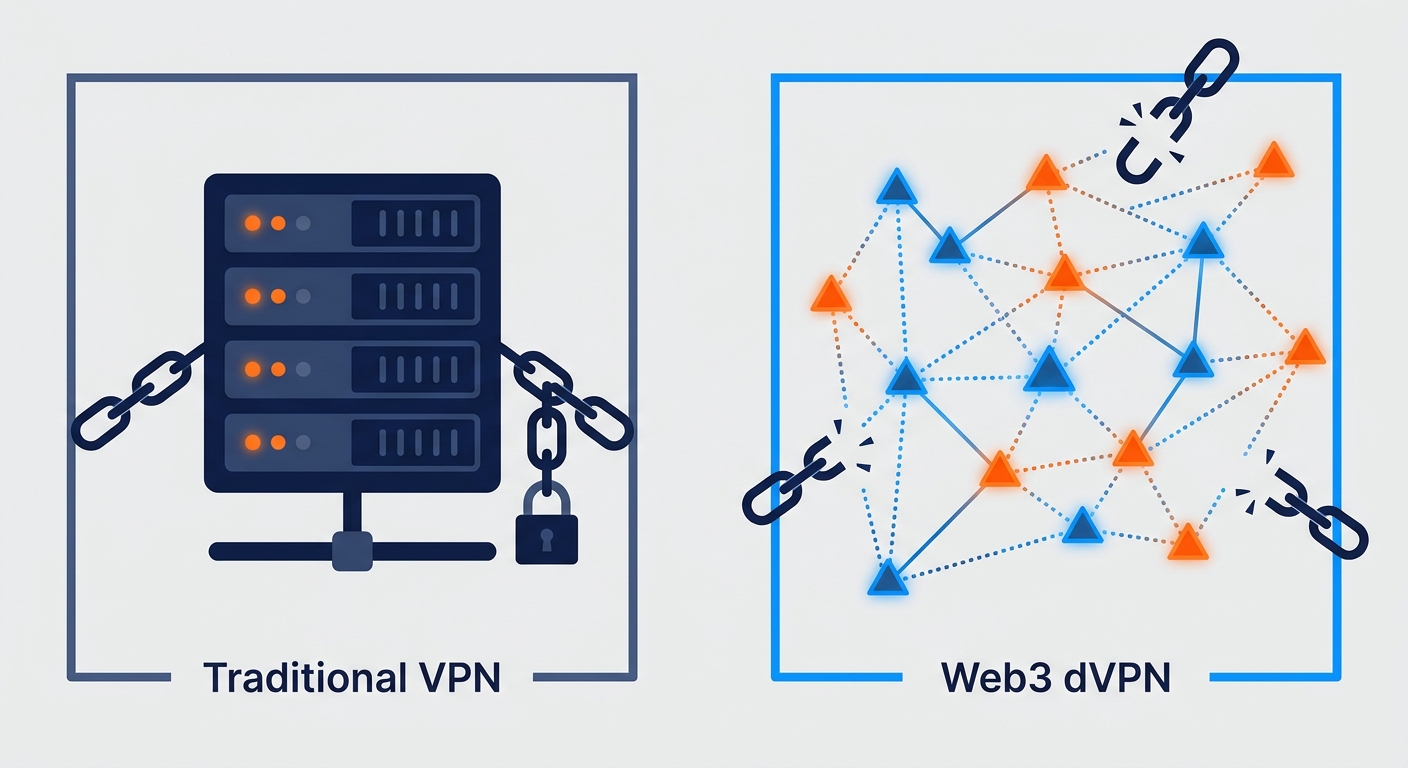
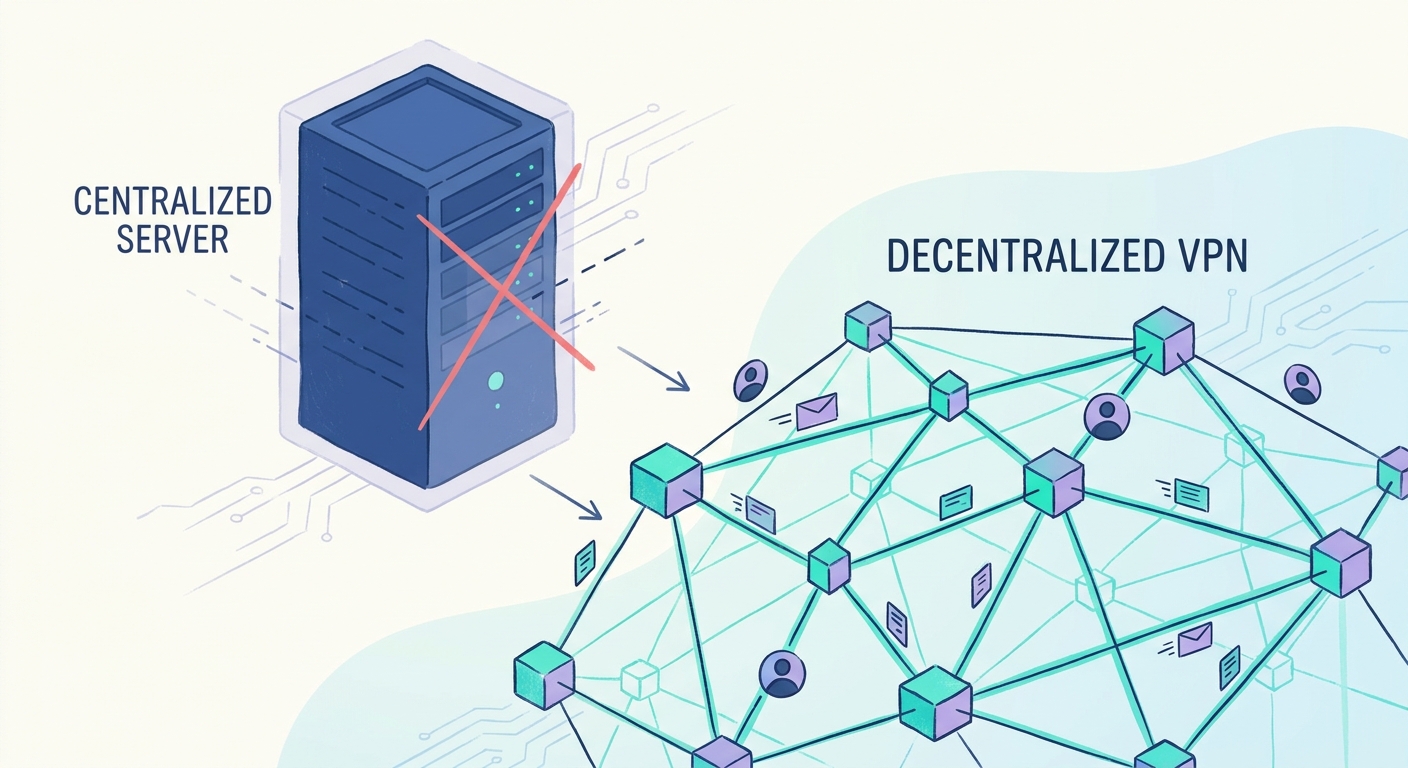
Ever feel like your "private" VPN is actually just a big glass house with a very busy landlord? Traditional VPNs are basically honeypots; they sit there, collecting your data on a single server, just waiting for a hacker or a subpoena to come knocking.
Most people use a VPN to hide, but you're actually just shifting your trust from your ISP to a company like Nord or Express. If their server gets popped, your metadata—who you are, when you logged in, how much data you moved—is right there for the taking.
- Honeypots for Hackers: A centralized server is a giant target. If a bad actor gets into a provider's database, they don't just get one person's info; they get everyone's.
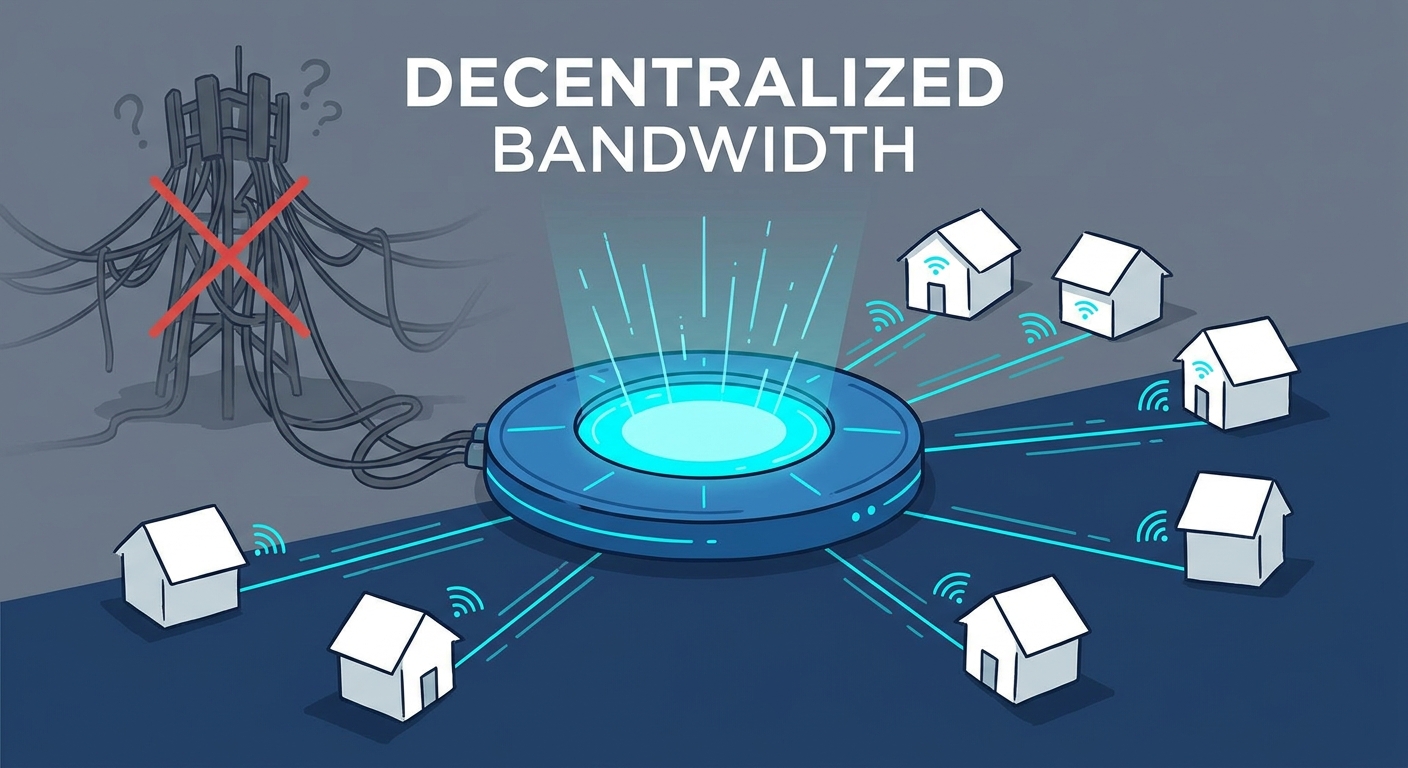
- The dVPN Shift: In a decentralized VPN (dvpn), nodes are run by regular people. It's like an "Airbnb for bandwidth." You aren't trusting one big corporation; you're using a peer-to-peer (p2p) network.
- Trustless Verification: Since you don't know the person running the node, you need a way to prove they aren't sniffing your traffic or lying about the data they sent. This is where those recursive zkp tricks come in handy.
In the web3 world, tunneling isn't just about moving packets; it's about wrapping them in layers of cryptographic proof. You want to move data between nodes without the node owner seeing what's inside or even knowing your real identity.
Encryption hides the content, but it doesn't hide the fact that you're communicating. As noted by sCrypt in the previous section, recursive proofs let us aggregate these handshakes so the network stays fast.
I've seen tech enthusiasts set up these nodes in their basements to earn token rewards. In gaming, this means a player can reduce lag by connecting through a local node without the node owner seeing their account details. In journalism, a reporter could access restricted sites via a p2p tunnel, ensuring no single server holds the "master key" to that sensitive connection.
According to research in Tari Labs University, using these "amicable pairs" of elliptic curves allows the verifier to check the tunnel's integrity without doing the heavy lifting themselves. It makes the whole "trustless" thing actually work on a phone.
Next, we're going to look at how these proofs actually "compress" the data so your speed doesn't tank.
The Math Behind the Magic: SNARKs, Halo, and More
To make these "private tunnels" actually work, we need some pretty heavy-duty math that doesn't act heavy. Here is the breakdown of the tech making this happen:
- SNARKs (Succinct Non-interactive Arguments of Knowledge): These are the rockstars of the zkp world. They're "succinct" because the proof is tiny and "non-interactive" because the prover can just send the proof over without having to do a back-and-forth dance with the verifier.
- The Halo Protocol: This was a massive breakthrough because it ditched the "trusted setup." Earlier snarks required a secret key to be created and then destroyed; if someone kept a copy, they could forge proofs. Halo, as discussed in research by the Electric Coin Company, uses "nested amortization" to verify proofs without that risky initial secret.
- Cycles of Elliptic Curves: This sounds like a prog-rock band name, but it's the secret sauce for mobile dvpns. By using "amicable pairs" of curves (like Tweedledum and Tweedledee), a phone can verify a proof using its native math language, making recursion fast enough to handle real-time traffic.
Most people don't realize that checking a cryptographic proof is actually a pretty "loud" computational task. If a dvpn node had to check every single packet's history from scratch, your Netflix stream would look like a slideshow from 1995.
As previously discussed, recursive proofs solve this by "compressing" the workload. But there's another trick: Parallel Proof Generation. Instead of one guy checking a thousand receipts in a row, you hire a thousand guys to check one receipt each, then combine their results into one tiny "master" receipt.
I've seen this play out in more than just web browsing. In finance, high-frequency traders use these parallel snarks to prove a million trades are valid without making the auditor check every single one, keeping the market moving at light speed.
According to Jiaheng Zhang's research at UC Berkeley, protocols like Virgo and Libra have pushed this even further, achieving "optimal prover time." This means the time it takes to create the proof is now strictly linear to the size of the data—no more exponential slowdowns.
So, we've got the math to keep things fast and private. But how does this actually stop someone from stealing your data? Next, we're looking at how this fits into the bigger picture of physical hardware.
Tokenized Bandwidth and the Airbnb for the Internet
Ever thought about how much of your home internet connection just sits there doing nothing while you're at work or sleeping? It's like having a spare bedroom that stays empty all year—except in this case, the "room" is your unused upload speed.
This is where tokenized bandwidth comes in. It's basically the "Airbnb for the Internet." Instead of letting that extra capacity go to waste, you can rent it out to a peer-to-peer (p2p) network and get paid in crypto.
Bandwidth mining is turning into a massive trend because it flips the old isp model on its head. Usually, you pay a company like Comcast or Verizon for a pipe, and they don't care if you use 1% or 90% of it.
With a decentralized vpn, your router becomes a "node." When someone across the world needs a secure connection, they tunnel through your IP, and you earn tokens for the data moved. It’s a way for users to take back control, and sites like SquirrelVPN are constantly tracking how these features are making the web more open.
But there is a catch: how does the person paying you know you actually provided the bandwidth? You could just lie and say you sent 10 GB when you only sent 1. This is where those recursive zkp tricks we talked about earlier save the day.
The whole system runs on supply and demand for global IP addresses. A researcher in Turkey might need a US-based IP to bypass local censorship, while a small business in Ohio has extra fiber capacity to spare.
- Smart Contracts for Trust: Payments happen automatically. No waiting for a check in the mail; the blockchain handles the micro-transactions every time a packet is verified.
- Privacy as the Backbone: The magic of zkp means that while I'm earning tokens from your traffic, I have zero clue what you’re actually doing online.
- Industry Impact: In retail, companies use p2p networks to check how their prices look to customers in different countries without getting blocked by anti-bot software.
As noted in a 2022 study by sCrypt, this is only possible because we can aggregate thousands of these tiny usage proofs into one "master proof." It keeps the blockchain from getting clogged up with billions of tiny payment receipts.
Honestly, it’s a win-win. You pay for your internet by sharing it, and the world gets a more resilient, censorship-resistant web.
DePIN: The New Physical Infrastructure
Ever wonder why we're still relying on massive server farms owned by three-letter corporations to run the entire internet? It feels a bit like we're renting the very air we breathe from a landlord who watches everything we do.
That's where DePIN (Decentralized Physical Infrastructure Networks) comes in to shake things up. Instead of a single company owning the "pipes," the community owns the hardware—your router, your neighbor's storage drive, maybe even a local weather station—and gets paid in tokens to keep it running.
- Hardware without the Hegemony: DePIN turns regular devices into "nodes" that act as the routers and servers of a new, global web. You aren't just a consumer anymore; you're part of the infrastructure.
- Censorship Resistance: Because there's no central "off" switch, it's incredibly hard for any government or isp to shut down a p2p network.
- The Efficiency Play: According to Jiaheng Zhang's research at UC Berkeley, protocols like deVirgo allow these distributed networks to scale by letting multiple machines handle proof generation in parallel, making the whole system "optimal" in terms of speed.
The real challenge with depin is proving that all these random nodes are actually doing what they say. If I'm paying you for bandwidth, I need to know you didn't just fabricate the data logs.
Recursive proofs act as the "glue" here. They use IVC (Incrementally Verifiable Computation) to verify state transitions. Basically, IVC is the mathematical process of updating a proof step-by-step as new data is added, so you don't have to restart the proof from scratch every time a new packet moves.
In logistics, this means a network of private sensors could verify that a shipment stayed at the right temperature across ten different delivery trucks without revealing the exact GPS route of those trucks.
Honestly, it's pretty cool seeing this move from theory to actual hardware sitting on people's desks.
Implementing Private Tunneling with Recursive ZKP
Moving from theory to code is where things get messy. To build a recursive zkp tunnel, we have to translate network behavior into arithmetic circuits. Think of these as a series of logic gates that process your data. The "witness" is the secret part of the proof—like your private key or the actual contents of your web traffic—that never gets revealed to the node running the tunnel.
- Arithmetic Circuits: We define the tunnel's rules using math. Instead of a server checking your logs, the circuit verifies that the packet followed the right path and wasn't tampered with.
- Handling the Witness: We use "masking polynomials" to hide the witness. As previously discussed in research by Jiaheng Zhang, these small masks ensure that even if a node sees the proof, they can't reverse-engineer your data.
- Millisecond Verification: Because the proofs are recursive, the verifier only checks the last proof in the chain. This happens in milliseconds, allowing for a smooth 4K stream or a lag-free gaming session.
Honestly, it's not all sunshine and rainbows. Developers face some serious hurdles when building these systems for real-world use. One big issue is bilinear pairings. These are math operations used to verify proofs, but they're computationally expensive. If you aren't careful, they'll eat your phone's battery for breakfast.
Choosing the right finite fields is also a bit of a headache. You need a field that supports the fast Fourier transforms (fft) required for the math to stay quick. I've seen devs struggle with this—if you pick the wrong field, your prover time goes from "instant" to "I'm going to grab a coffee while this loads."
A 2020 study on the Virgo protocol showed that using extension fields of Mersenne primes can make modular multiplications significantly faster, which is a total game-changer for mobile battery life.
In healthcare, these optimized tunnels allow a clinic to send an MRI to a specialist. The recursive proof ensures the data hasn't been touched, but the node owner—who might just be some guy with a router in his basement—never sees the patient's name or medical history.
The Future of Web3 Privacy Tools
Think about the last time you used a "free" service and realized your data was the actual currency. It feels a bit like we've been living in a digital fishbowl, right? But the tools we've explored—those recursive proofs and p2p tunnels—are finally smashing the glass.
We’re moving away from the days where you had to trust a single vpn company not to sell your browsing history. With Web3 tools, the "trust" isn't in a ceo's promise; it’s in the math. As we've seen, recursive proofs let us verify entire networks without slowing down to a crawl.
- FHE meets zkp: Imagine a world where a server can process your data without ever "seeing" it. Fully Homomorphic Encryption (fhe) is starting to blend with zero-knowledge tech. While zkp proves the computation was valid, fhe keeps the data itself encrypted during that computation. It's the ultimate privacy combo.
- AI-Driven Routes: Future dvpns won't just move packets; they'll use ai to optimize routes across depin nodes. This means your connection finds the fastest, most secure path through the p2p mesh automatically.
- The End of Metadata Leaks: Standard vpns hide your IP, but they often leak when and how much you’re communicating. Recursive proofs can aggregate these patterns, making your digital footprint look like background noise to anyone watching.
I've seen tech-savvy small businesses already moving their internal comms to these p2p tunnels to avoid industrial espionage. In real estate, it’s becoming a way to share sensitive contract details across a distributed network without exposing the buyer's identity to every node in the chain.
At the end of the day, privacy shouldn't be a premium feature you pay $9.99 a month for. It’s a basic right. By moving to decentralized, token-incentivized networks, we're building an internet that’s actually owned by the people who use it.
The tech is messy and the math is hard, but the result is a web that’s finally, truly free. Stay curious, keep your keys safe, and don't stop questioning who owns your data.