Proof of Bandwidth (PoB) Consensus Mechanisms

TL;DR
What is Proof of Bandwidth actually about?
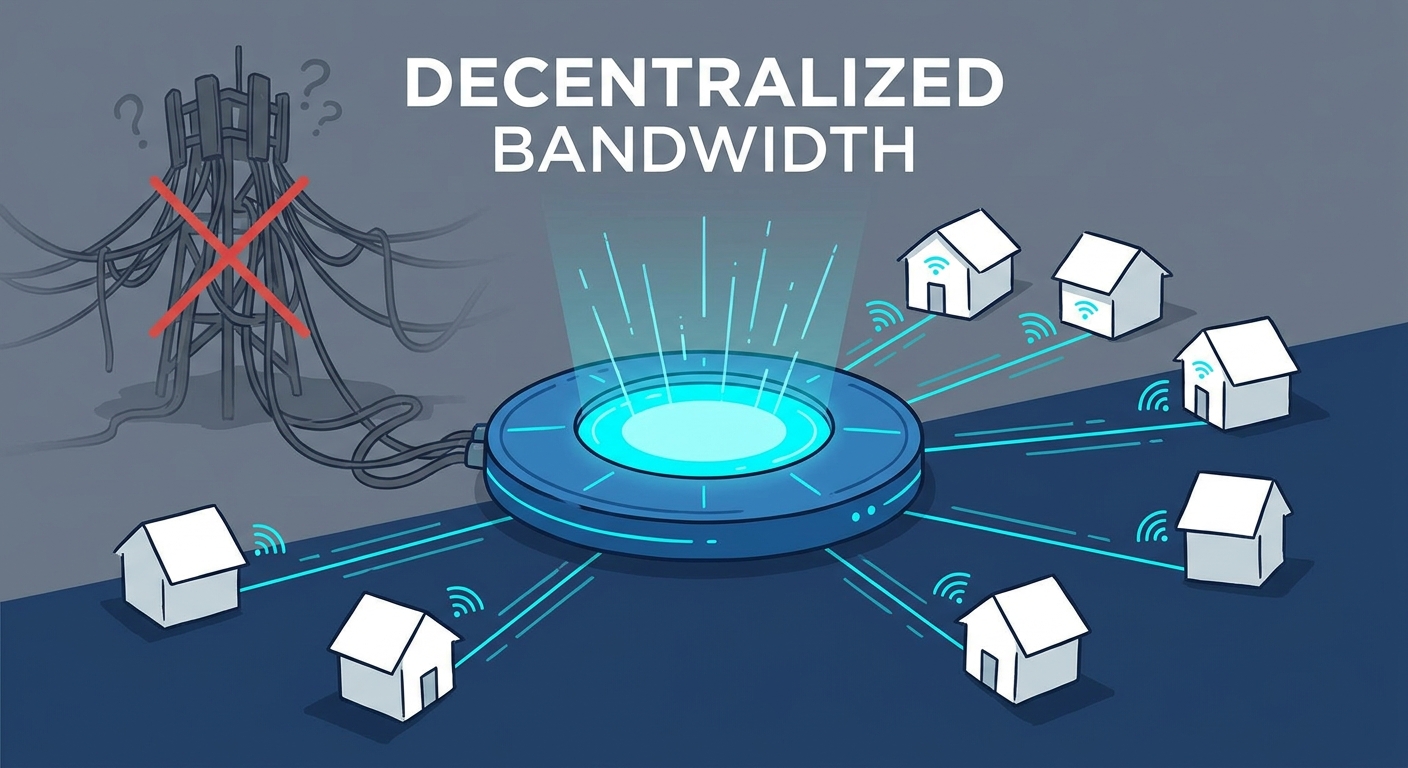
Ever wondered why your home internet sits idle while you're at work, even though you’re still paying the ISP for every megabit? Proof of Bandwidth (PoB) is basically the tech that turns that wasted pipe into a digital currency.
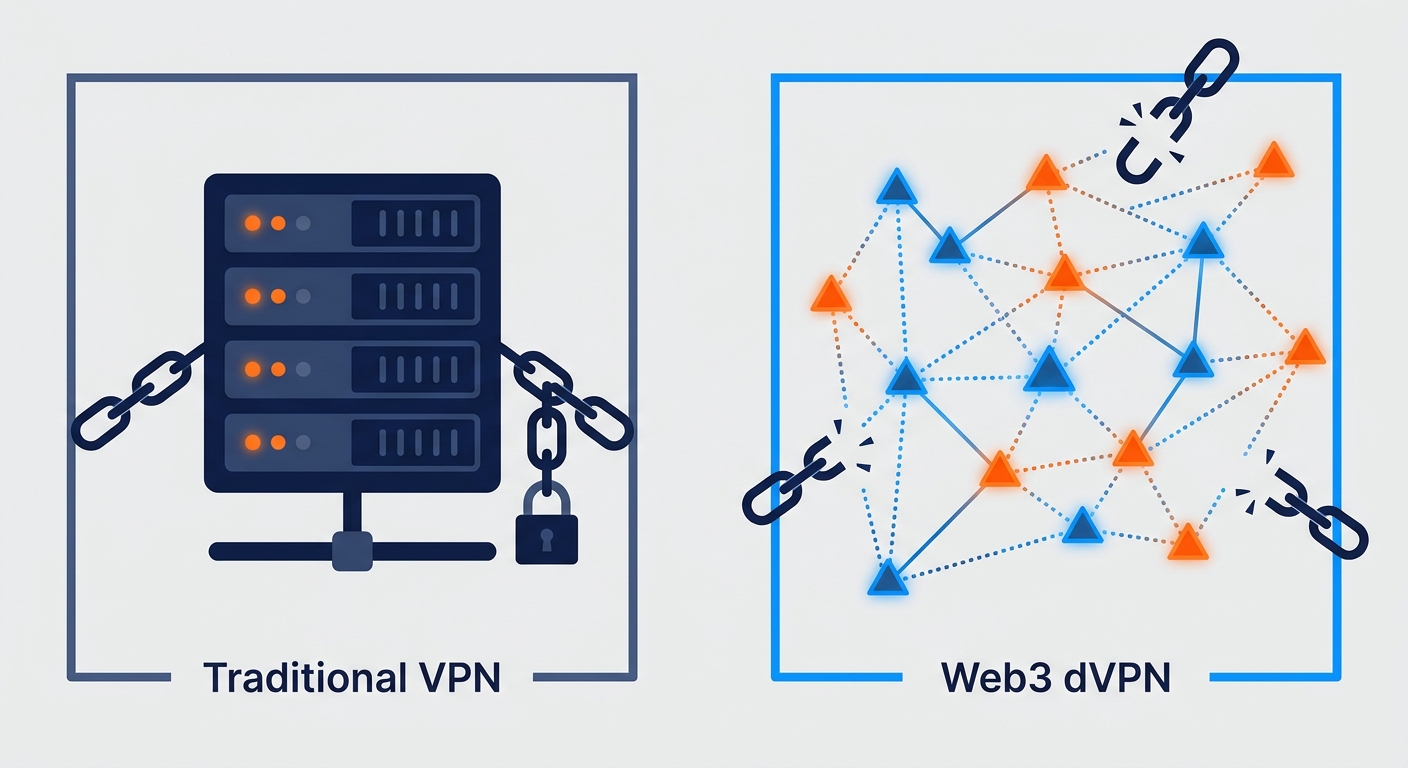
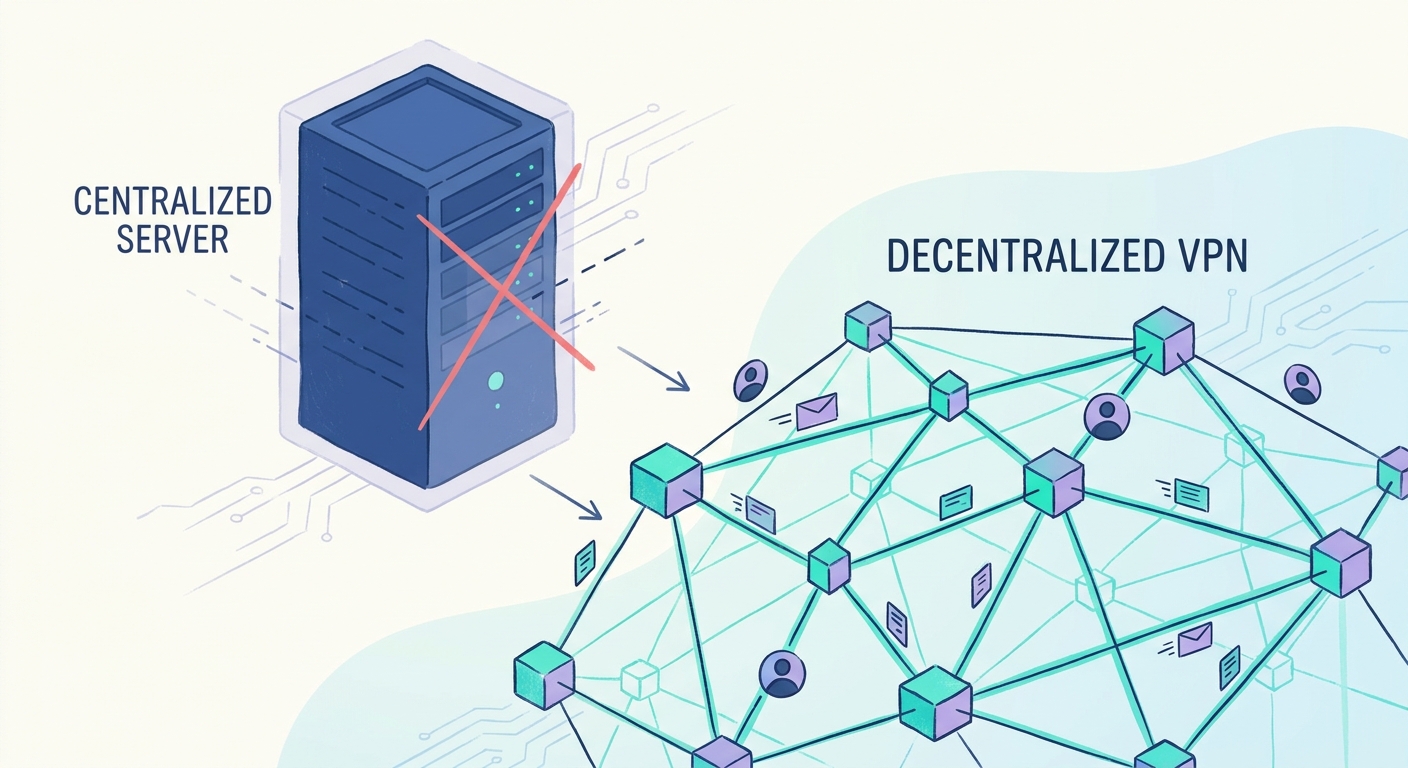
In a standard VPN, you just trust a big company server, but decentralized networks (dVPNs) need a way to prove a node actually provided the speed it claimed. PoB is the "receipt" for that data transfer.
- Bandwidth as a tokenized resource: Think of it like a marketplace where your spare upload speed is a commodity, similar to how solar panels sell excess power back to the grid.
- Why we need consensus: Unlike a corporate VPN, a dVPN has no boss; PoB uses cryptographic checks to make sure a node isn't faking its traffic logs to earn rewards.
- The role of nodes: Regular people run software that shares their connection. To make sure these nodes stay honest, they usually have to "stake" or lock up some tokens as collateral. If they try to cheat the system, they lose that deposit.
This setup is especially popular for a retail shop or a small cafe. These places usually have high-capacity commercial lines that sit totally idle after hours or during slow shifts, making them the perfect "power plants" for a PoB network compared to a regular house.
According to research by Deloitte (2023), the shift toward decentralized infrastructure is accelerating as organizations look for more resilient network alternatives. (Can US infrastructure keep up with the AI economy? - Deloitte)
It’s a clever way to build an internet that nobody truly owns. Next, let’s look at how the actual verification happens under the hood.
How the mechanism verifies your speed
So, how do you actually prove a node isn't just lying about its speed to farm tokens? It’s not like we can just take their word for it—this is crypto, after all.
The network uses something called challenge-response cycles. Think of it like a digital "ping" but way more aggressive. The protocol sends random, encrypted data packets to a node and measures exactly how long it takes for that node to process and send them back.
It’s about more than just a speed test you’d run on your browser. The system looks at several factors:
- Packet Latency: If a node claims to be in New York but has a 300ms round-trip time to a local tester, something is fishy. It helps detect "sybil attacks" where one person pretends to be fifty different nodes.
- Throughput Verification: The network forces the node to transfer a specific file size. If the node can't maintain the bitrate, its "quality of service" score drops.
- Cryptographic Signatures: Every bit of data sent is signed. This prevents a node from just rerouting traffic through a faster data center and claiming it as its own residential bandwidth.
If you’re providing a stable connection, you get paid. It’s pretty simple math—most protocols use a formula that weighs uptime, bandwidth volume, and node reputation.
A 2024 report by Gartner suggests that decentralized physical infrastructure (depin) is becoming a viable way for small businesses to offset utility costs. By sharing a guest Wi-Fi pipe that's empty at night, a small cafe can actually earn enough tokens to cover part of their monthly ISP bill.
It’s a self-healing system. If a node gets greedy and starts spoofing packets, the consensus mechanism spots the anomaly and cuts off the rewards. Next, we’ll dive into why this setup is actually a nightmare for government censors.
Why DePIN and PoB matters for your privacy
It is well known that isps use deep packet inspection (dpi) to throttle users and log every packet header that leaves a router. Most people don't realize that even with a basic VPN, you're just moving the "trust" from your provider to a single data center. That is why staying informed on web3 privacy is huge. When you understand how a decentralized architecture works, you start seeing why the old way is so broken. Following the latest vpn features isn't just for nerds; it’s about knowing which tools actually stop your data from being a commodity.
The magic of depin and PoB is that it turns the internet into an "Airbnb for bandwidth." Instead of a few massive data centers that a government can just block with one firewall rule, you have thousands of residential nodes.
- Residential IP Diversity: Since nodes are hosted by regular people in homes and small cafes, the traffic looks like normal web browsing. It’s nearly impossible for censors to blacklist every home ip in a city.
- No Single Point of Failure: In a p2p network, if one node goes down or gets seized, the PoB protocol just routes you to the next verified provider.
- Encryption by Default: Because the consensus mechanism requires cryptographic signatures for every packet to prove bandwidth was shared, the privacy is baked into the "receipt" itself.
According to a 2023 report by UNCTAD, the concentration of data in a few large platforms creates significant privacy risks, making decentralized alternatives a necessity for digital sovereignty.
It’s a nightmare for anyone trying to control information. Honestly, it’s about time we took the power back from the big pipes. Next, let’s talk about the technical hurdles of actually running one of these nodes.
Challenges in the PoB ecosystem
It sounds great on paper, right? But shoving enterprise-grade traffic through a home router is like trying to fit a fire hose through a straw. Most consumer gear just isn't built for the 24/7 packet forwarding that a robust pob network demands.
The first hurdle is the "brain" of your router—the cpu. When you start tunneling encrypted traffic for multiple users, that little processor hits 100% real quick, causing your Netflix stream to buffer while you're trying to earn tokens.
- Thermal Throttling: Cheap plastic routers sometimes literally melt their internal solder because they weren't designed for constant high-load p2p states.
- Memory Leaks: Many residential firmwares have buggy nat tables. If the pob protocol opens too many concurrent connections, the router just crashes and reboots.
- Energy Costs: Keeping a high-power rig running 24/7 to maximize rewards can sometimes cost more in electricity than the tokens are worth, especially in regions with high utility rates.
Then there is the "flaky neighbor" factor. In a decentralized setup, a node might go offline because someone tripped over a power cord or their isp started a random maintenance window.
- Smart Contract Slashing: If a node drops packets during a verification cycle, the contract might "slash" your staked tokens. Since you had to lock up collateral to join, this penalty hits your wallet directly to ensure you stay reliable.
- Latency Spikes: In retail environments, guest Wi-Fi usage can suddenly spike, leaving the pob node with zero priority and failing its speed tests.
According to a 2023 report by the OECD, the digital divide in upload speeds remains a massive bottleneck for p2p infrastructure growth in rural areas.
The Money Side: How Earnings Work
So, how do these "earnings" actually show up in your digital wallet? The economic model is usually based on supply and demand. When users want to browse the web privately, they pay in the network's native token.
These tokens are then distributed to node operators based on their PoB score. If you have a high-speed fiber connection in a high-demand area—like a city center—you'll likely earn more than someone on a slow DSL line in the woods. Most systems use a "burn and mint" or a reward pool model where a set amount of tokens are released every day to the people providing the most "proven" bandwidth. It's a way to turn your monthly internet bill from an expense into a potential revenue stream.
Wrapping up the future of tokenized network
The internet's changing, and not a moment too soon. We're moving from a few big data centers to a mesh of millions of home nodes.
- ai Marketplaces: PoB ensures the high-speed, verified transfer of massive datasets required for training ai models across decentralized clusters.
- Retail & Healthcare: Hospitals can use p2p for massive, encrypted medical imaging transfers, using PoB to guarantee the bandwidth needed for life-critical data.
- Edge Security: Processing data at the node level reduces the attack surface for ddos, with PoB verifying that security nodes have the capacity to absorb traffic spikes.
As noted earlier by the OECD, closing the digital divide is key. Honestly, it’s just the beginning for depin.
Take back your data.