Multi-Hop Onion Routing in Decentralized Architectures

TL;DR
The basics of onion routing in a p2p world
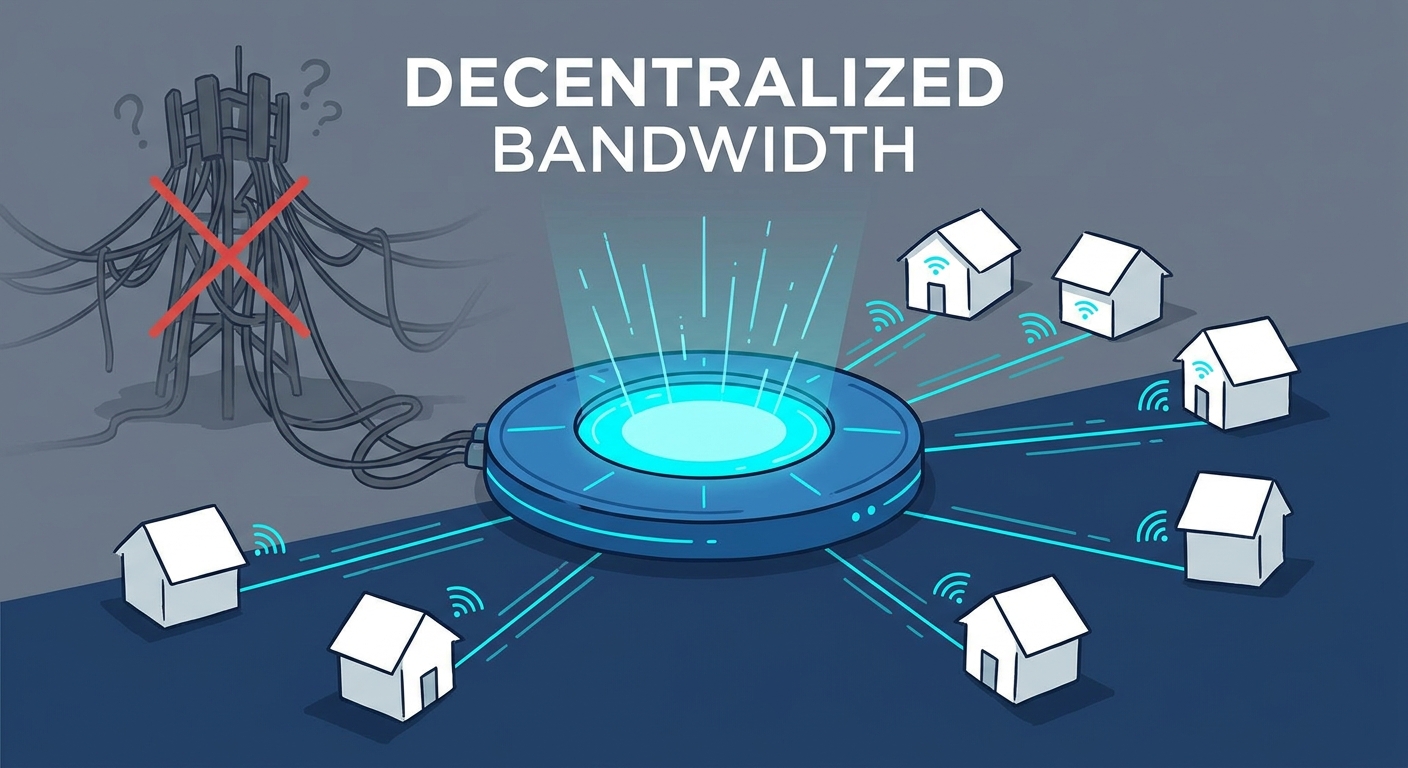
Ever wonder why your "private" VPN feels like a glass house? If you're only using one server, that provider sees everything you do—it's a massive single point of failure. Multi-hop routing fixes this by bouncing your data through several nodes so no one has the full picture.
Basically, instead of a straight line, your traffic takes a zig-zag path. This is common in mesh networks where coverage exceeds a single node's range.
- Layered Encryption: Each node (or hop) only peels back one layer of the "onion," knowing only where the packet came from and where it’s going next.
- No Central Trust: In a p2p setup, you aren't relying on one corporate datacenter; you're using a distributed web of nodes.
- Energy and Efficiency: It’s not just for stealth; sometimes jumping between closer radio nodes is actually more power-efficient than blasting a signal to a distant tower.
I’ve seen folks try to DIY this with nested containers, but decentralized architectures make it native. It’s way harder for anyone to track you when the path changes constantly. This is where DePIN (Decentralized Physical Infrastructure Networks) comes in, basically it's just people sharing their hardware to build real-world networks.
Next, let's look at the crypto side...
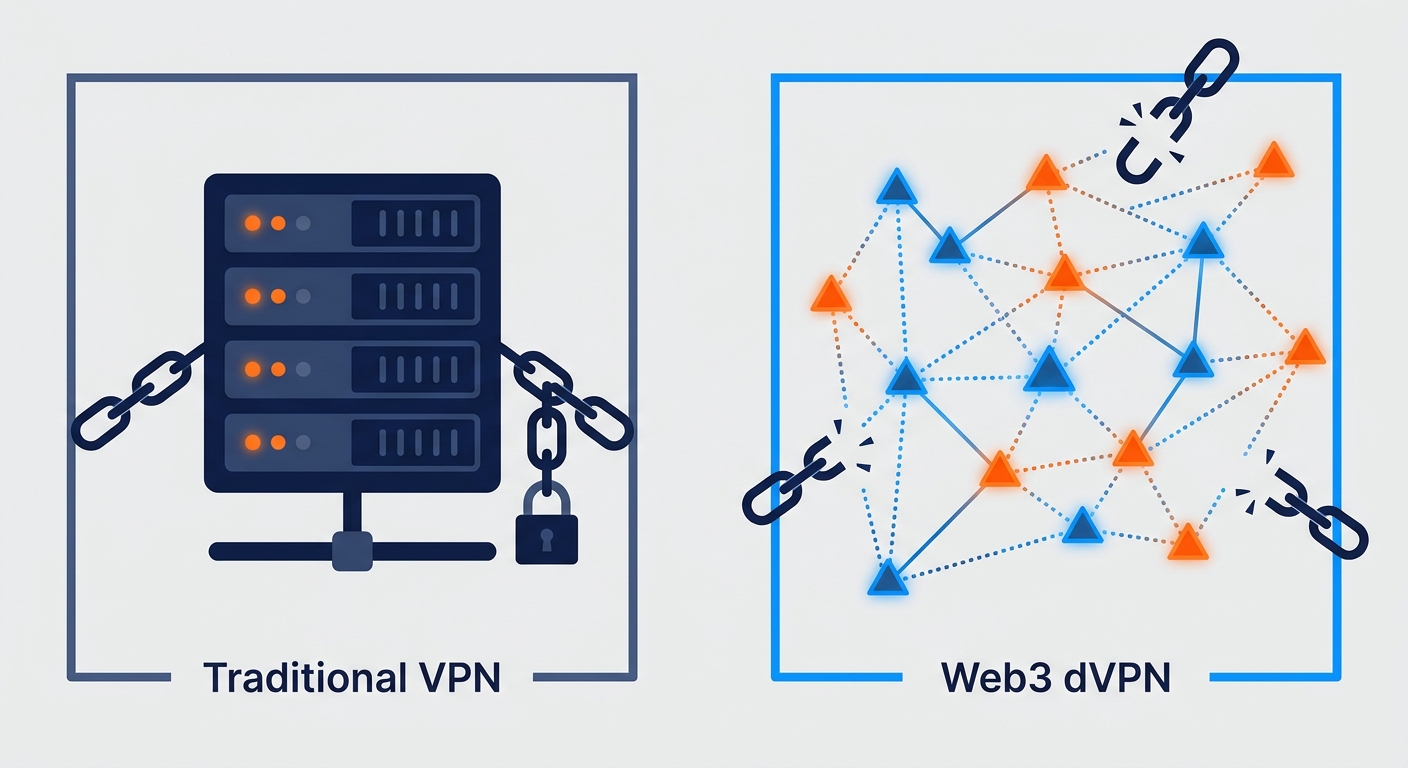
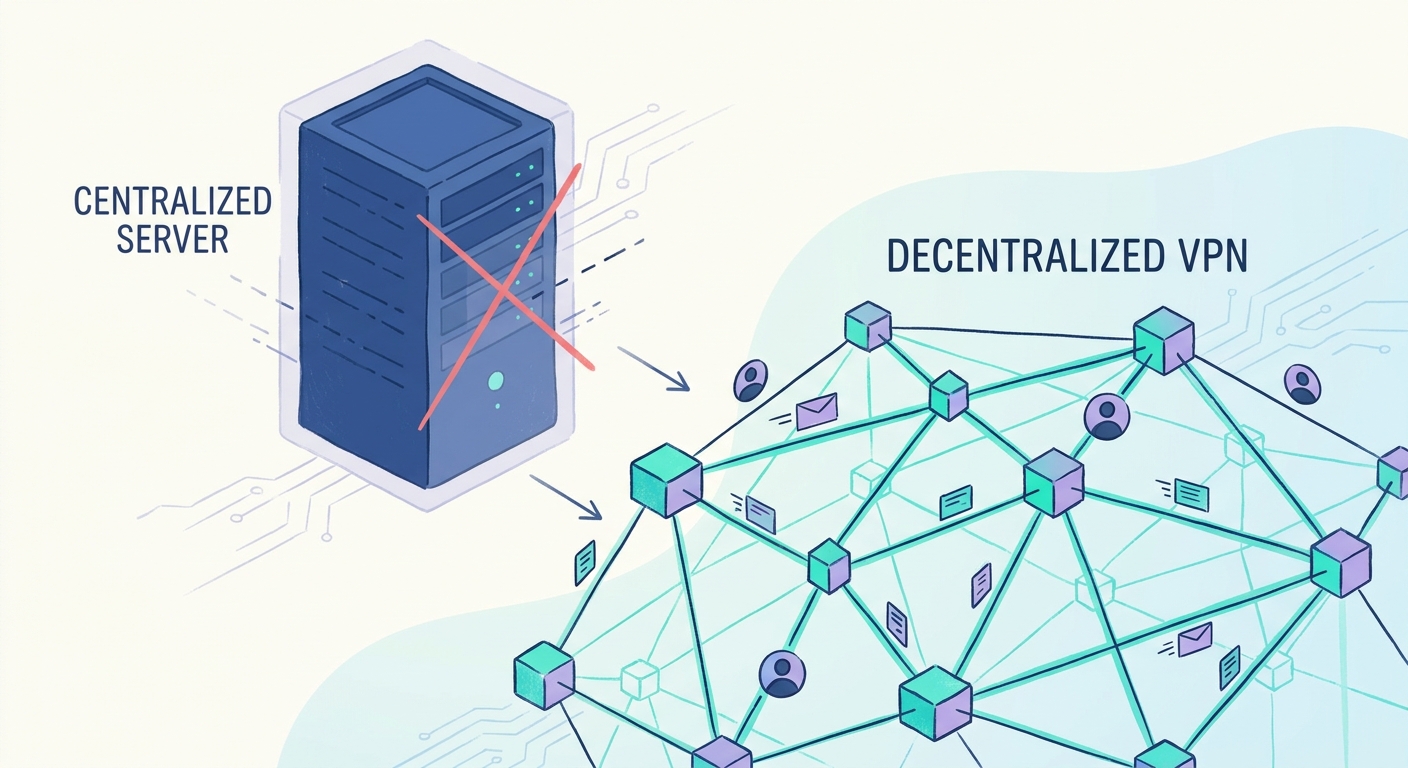
Layered encryption and the decentralized vpn
Think of layered encryption like those russian nesting dolls, but for your data packets. To make this work without trusting anyone, the system uses an asymmetric cryptographic handshake—usually something like an Elliptic Curve Diffie-Hellman (ECDH) exchange. Before any data moves, your client uses the public keys of each node to negotiate a unique "session key" for every hop. This way, your computer wraps the data in three layers of encryption before it even leaves your house. The first node can only unlock the outer layer to see where to send it next, but it can't see the actual message or the final destination.
- Hop-Specific Keys: Your client negotiates separate keys with each relay; the entry node can't see what the exit node is doing.
- Anonymity Sets: By mixing your traffic with thousands of others, individual streams become impossible to distinguish.
- Node Diversity: Since these aren't owned by one company, there is no "master switch" to log your history.
I usually tell people to stick with WireGuard for the speed, though it's important to remember WireGuard is a point-to-point tunnel protocol. It doesn't do multi-hop by itself like Tor does. To get true anonymity, developers have to wrap WireGuard inside a custom framework that handles the onion-routing logic. If you're running a node on a linux box, you can actually see the encrypted blobs passing through without having any clue what's inside.
The space moves fast, especially with blockchain-based bandwidth markets. I usually keep an eye on projects that are open-sourcing their security audits because, honestly, if I can't read the source code, I don't trust the privacy claims.
Next, we're diving into how these nodes actually get paid for their trouble...
Incentivizing the network with tokenized bandwidth
Why would anyone leave their pc running all night just to route someone else's traffic? In the old days, you did it for "the cause," but now we use tokenized bandwidth to make it worth your while. It’s basically the airbnb model for your internet pipe.
- Bandwidth Mining: You run a node, and the network pays you in crypto based on how much data you successfully relay.
- Proof of Bandwidth: Protocols use cryptographic challenges to prove you aren't faking your speeds. This is huge for stopping Sybil attacks, where one guy tries to create 1,000 fake nodes to control the network. By requiring a "stake" or proof of work, it becomes way too expensive for a hacker to fake a bunch of identities.
- Dynamic Pricing: In a decentralized exchange, if a node in a high-censorship region goes offline, the rewards for new nodes there spike.
I’ve seen guys in retail and finance use this to scrape data without getting blocked. Next, we’ll look at the trade-offs and real-world applications.
Trade-offs and applications in depin networks
Look, multi-hop isn't a magic bullet; if you're bouncing traffic through three nodes across the globe, your ping is going to suffer. It's the classic trade-off where you sacrifice raw speed for actual digital sovereignty.
Each extra "hop" adds millisecond delays because of the encryption overhead and physical distance. While WireGuard is fast, it wasn't originally built for onion-style routing. To fix this, next-gen depin projects are optimizing node selection based on proximity or using protocols like Sphinx to keep packet sizes uniform so nobody can guess what's inside based on timing.
Real-world Applications:
- Healthcare: Securely sharing patient records between clinics without a central database leak.
- Retail: Preventing competitors from tracking inventory scraping via distributed ip rotation.
- Finance: High-frequency traders using mesh networks to avoid centralized exchange bottlenecks.
The real win is making the network impossible to kill. Since there's no central ceo or api to subpoena, a decentralized isp alternative stays up even when governments try to pull the plug.
Honestly, we're building a more resilient web here. It's messy, but it's ours.