Incentive Structure Design for Residential Proxy Node Networks

TL;DR
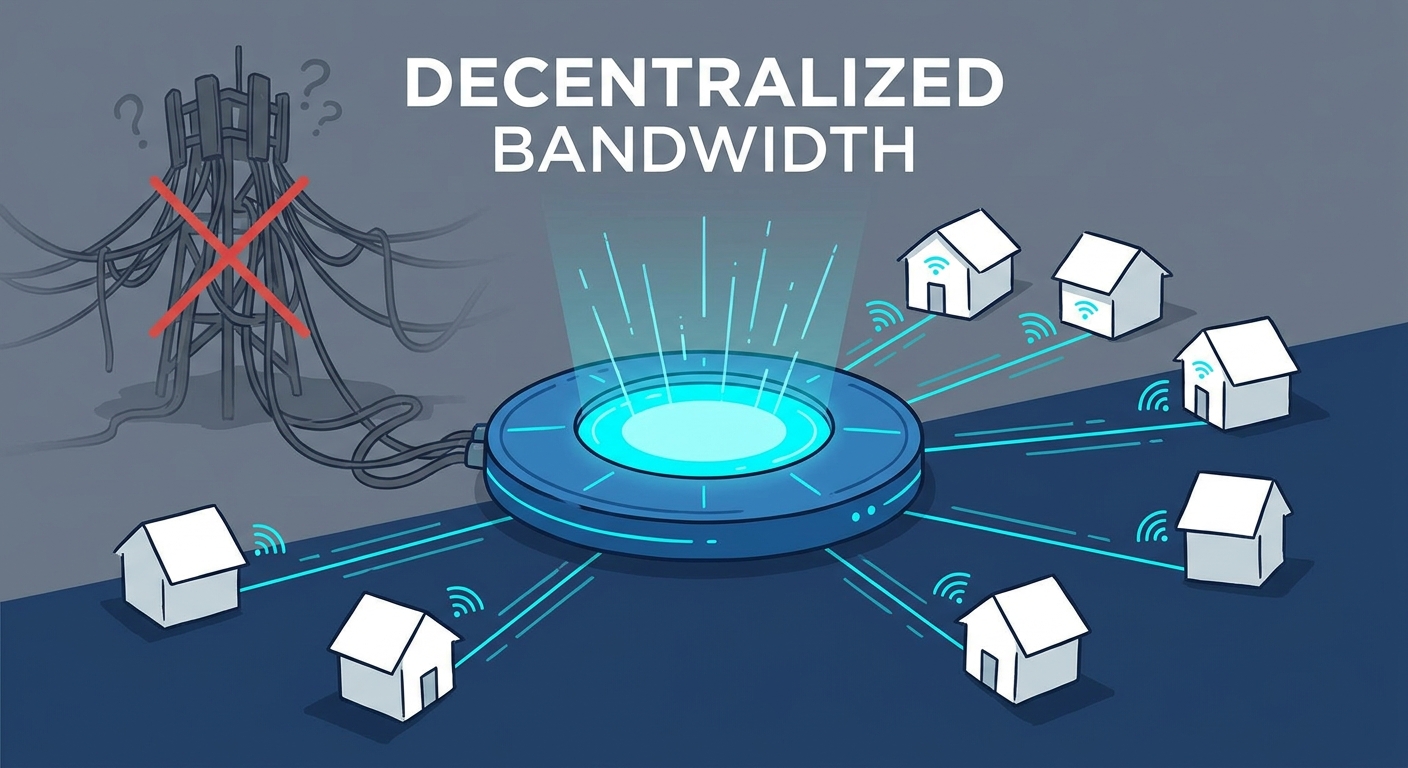
The shift toward residential proxy nodes and depin
Ever wonder why some websites treat you like a criminal just for using a vpn? It’s because big platforms have gotten really good at spotting data center traffic, which is why everyone is moving toward residential nodes and depin.
The main difference comes down to trust. Data center IPs are like wearing a neon sign that says "I am a bot," whereas a residential IP looks like a regular person sitting on their couch in Ohio or London. According to a 2024 report by DataPulse, nearly 72% of modern web scrapers now prioritize residential networks to avoid "403 Forbidden" errors.
- Bypassing geo-blocks: Streaming services or finance apps often blacklist entire server ranges, but they can't easily block a home wifi connection without hitting real customers.
- Authentic traffic: Retailers use these nodes to check if their prices look right to local shoppers, avoiding the "price discrimination" bots often trigger.
- Healthcare & Research: Researchers use residential nodes to access localized medical journals that might be restricted to specific regions.
We're obsessed with how these networks evolve because, honestly, the old way of hiding your IP is dying. At squirrelvpn, we break down these complex depin (Decentralized Physical Infrastructure Networks) trends so you don't have to be a network architect to stay private.
Our mission is simple: making digital freedom actually doable for normal people. Whether it's explaining wireguard or how to earn tokens by sharing spare bandwidth, we're here to help you take back control.
Next, let's look at how these networks actually convince people to share their home internet in the first place.
Core components of a tokenized bandwidth economy
So, you’ve decided to turn your old router into a little crypto-earning machine. It sounds like magic, but the "glue" holding this whole decentralized mess together is a solid incentive structure. If the rewards aren't right, nobody shares their bandwidth; if the verification is weak, the whole network gets flooded with fake traffic.
Think of proof-of-bandwidth as the digital version of a receipt. In a depin setup, the network needs to be 100% sure you actually provided the speed you claimed. We use something called "heartbeat checks" where the system pings your node at random times. If you're offline or your late with a response, you lose out on rewards.
The biggest headache here is node spoofing. Some "clever" users try to trick the system by running virtual machines that pretend to be fifty different residential houses. To stop this, modern protocols like those discussed by iotex use hardware-based identities to make sure a node is a real physical device and not just a script running in a data center.
Now, how do you actually get paid? Most networks use a mix of inflationary and deflationary models. In the beginning, they hand out tokens like candy to get people to join (inflation). But as the network matures, they might "burn" tokens every time a business buys bandwidth, which keeps the price from crashing.
- Staking requirements: Often, you have to lock up a bit of the network's native token to start a node. This "skin in the game" keeps people from acting like jerks or providing laggy service.
- Early adopter bonuses: If you were one of the first 100 people in a city to set up a node, you'll likely earn way more than someone joining three years later.
- Quality of Service (QoS): In retail price monitoring, a node in London is worth way more than one in a tiny village because that's where the data is needed.
A 2023 analysis by Messari on the depin sector suggests that "supply-side" incentives are the make-or-break factor for these protocols, as users won't stay if the token value doesn't cover their electricity and hardware wear.
Next up, we’re gonna dive into how these networks actually keep your personal data safe while all this sharing is happening.
Designing for fairness and network health
Getting a network of thousands of strangers to play nice is basically like herding cats, except the cats are trying to hack your incentive model for extra profit. If you don't design for fairness from day one, the "whales" with massive server farms will just bully the regular home users out of the ecosystem.
Why does a node in Manhattan earn three times more than one in a rural village? It’s not about being elitist; it's about supply and demand. Businesses—like retail giants checking local pricing or travel sites verifying flight costs—need data from where the customers actually are.
- Demand-based multipliers: Most depin protocols use a "heat map" to boost rewards in high-traffic zones. If everyone in South Korea is trying to access US-based streaming, those US residential nodes get a "surge" bonus.
- Congestion control: Just like Uber, if too many people start hosting nodes in one apartment building, the rewards drop. This forces the network to spread out, ensuring better global health.
- Balancing the scales: To keep the network from becoming just a "big city" tool, some protocols offer a "baseline" reward for staying online, even if nobody is using your data right that second.
If your node is constantly lagging or dropping packets during a sensitive finance transaction, you’re hurting the whole brand. That’s where slashing comes in—basically a "fine" taken from your staked tokens if you don't meet the quality of service (qos) standards.
According to a 2023 report by Messari (as discussed earlier regarding supply-side incentives), reputation-based routing is becoming the standard for ensuring decentralized networks can actually compete with centralized providers on speed.
We use trust scores to rank nodes. If you’ve been online for six months with 99% uptime, you get priority for the high-paying "premium" traffic. It’s a simple way to reward the reliable folks and ignore the ones running their nodes on a potato.
Next, we're diving into the absolute "must-haves" for keeping your personal identity private while your router is busy earning you lunch money.
Technical implementation and security risks
Let's be real—letting a stranger route their internet traffic through your home wifi sounds like a digital nightmare. If you don't set up the technical "walls" correctly, you're basically leaving your front door wide open for someone to do something illegal using your IP address.
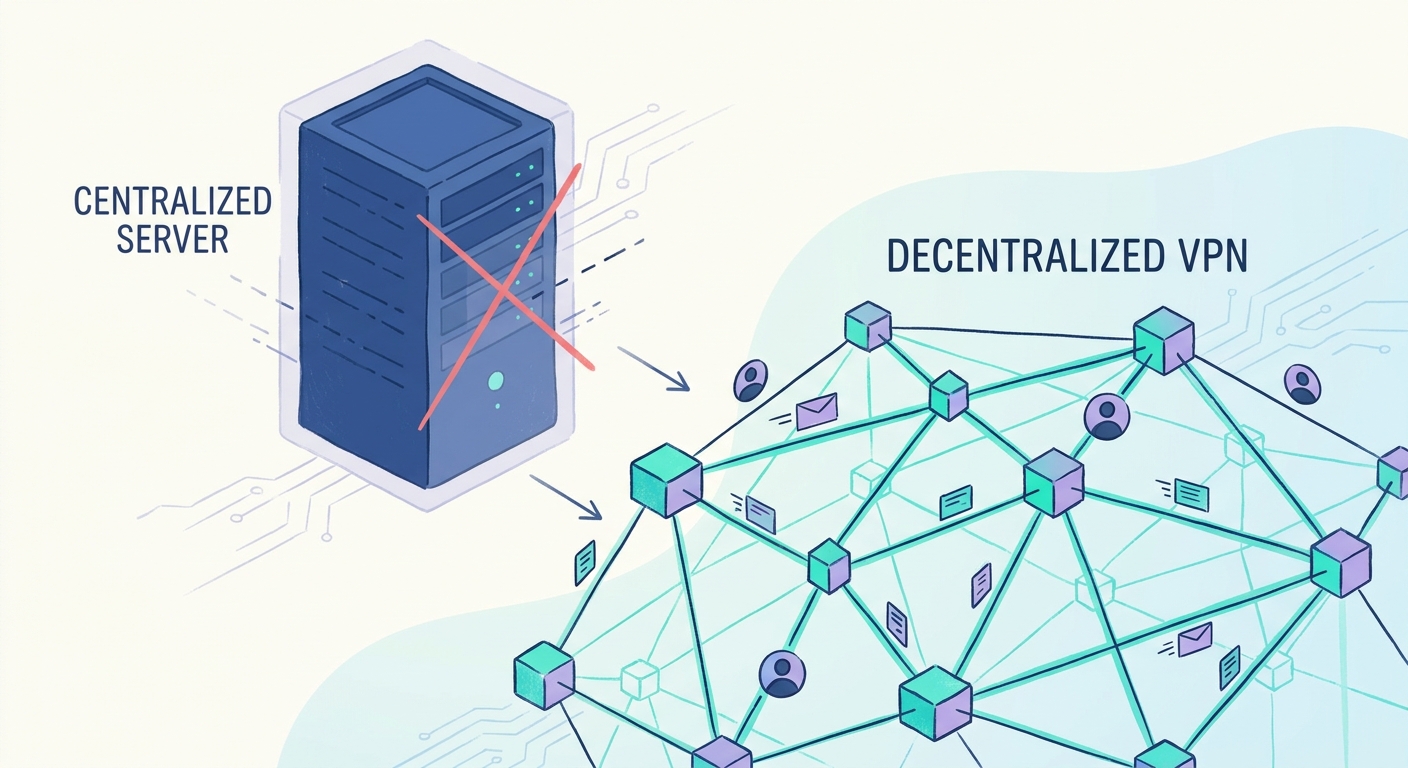
To keep things safe, we use encapsulation. Think of it like putting your data in a specialized armored truck before it hits the highway. Most modern depin projects use protocols like wireguard to create an encrypted tunnel between the user and the node provider. This ensures that the person hosting the node can't actually see what's inside the data packets passing through their router.
- Namespace Isolation: On the provider side, the proxy software should run in a "sandbox" (like a Docker container). This prevents a malicious user from jumping out of the proxy and into your personal photos or bank logins.
- Traffic Filtering: Good networks block "high-risk" ports by default (like those used for email spam or torrenting). This stops your IP from getting blacklisted by your ISP because someone else was being a jerk.
- End-to-End Encryption: Even if the node is decentralized, the data stays encrypted from the consumer's device all the way to the target website.
Nobody wants to chase down a company for five bucks worth of earned tokens. That’s why we use smart contracts to handle the money. Since sending tiny payments on the main ethereum network would cost more in fees than the actual reward, most platforms use "Layer 2" solutions like Polygon or Arbitrum to keep gas costs near zero.
According to a 2024 tech deep-dive by the block - which tracks how infrastructure tokens are moving - these micro-payments are becoming the backbone of the "machine-to-machine" economy. If a node provides 1GB of data, the contract automatically releases the payment. No human managers, no "check is in the mail" excuses.
It’s not just about getting paid, though; it’s about dispute resolution. If a consumer claims the node was slow but the node proves it sent the data, the smart contract acts as a neutral judge to settle the score based on the "heartbeat" logs we talked about earlier.
So, once the plumbing is secure and the money is flowing, how do we actually make sure this whole thing respects your privacy? Next, we're looking at the big "privacy-first" features that keep your identity under wraps.
Future outlook for airbnb for bandwidth models
So, are we actually looking at the end of big corporate isps controlling how we browse? Honestly, it feels like we’re finally moving toward a "Lego-style" internet where you own the bricks and the blueprints.
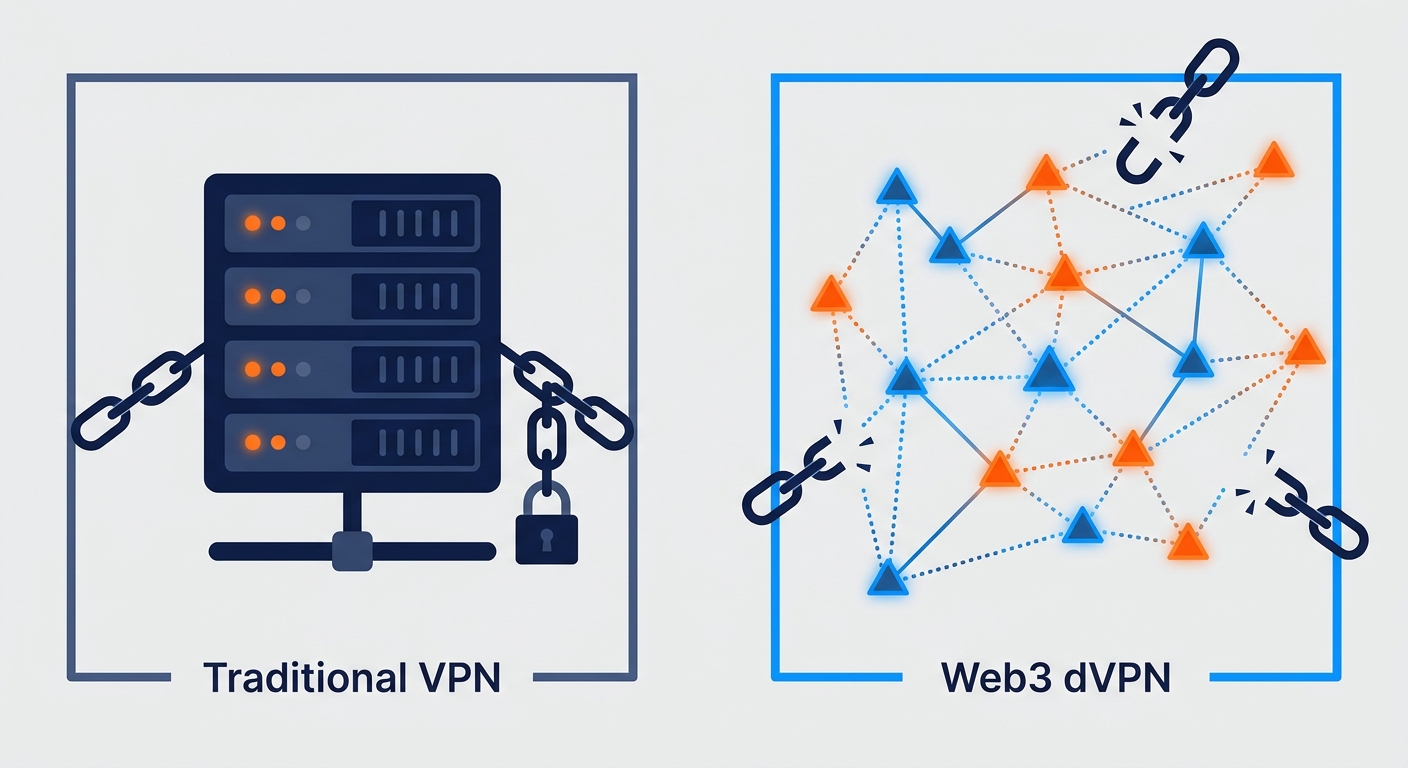
The shift toward dVPN tech isn't just a hobby for crypto nerds anymore; it’s becoming a necessity for censorship-resistant access. When a government decides to flip a switch and block an app, centralized servers are easy targets, but a million home routers? That's a different story.
- Global scaling: Unlike traditional providers that need to lay cables, depin grows wherever there's a power outlet and a wifi signal.
- Micro-economies: We’re seeing a future where your smart fridge might literally pay for its own electricity by selling its idle bandwidth.
- True Privacy: By stripping away the middleman, you aren't just a customer anymore—you're a stakeholder in a tokenized network economy.
As mentioned earlier when we looked at the block and their data on infrastructure tokens, the money is already moving into these "airbnb for bandwidth" models. It’s a messy, exciting transition, but it’s how we take the web back. Stay safe out there.