Top 7 Web3 VPNs for 2026: The Best Tools for Censorship-Resistant Browsing
If you’re still clinging to a traditional VPN in 2026, you’re just swapping one corporate gatekeeper for another. That "no-logs" badge on their website? It’s a fairy tale. You’re trusting a company’s internal culture, their server security, and whatever legal jurisdiction they happen to be hiding in.
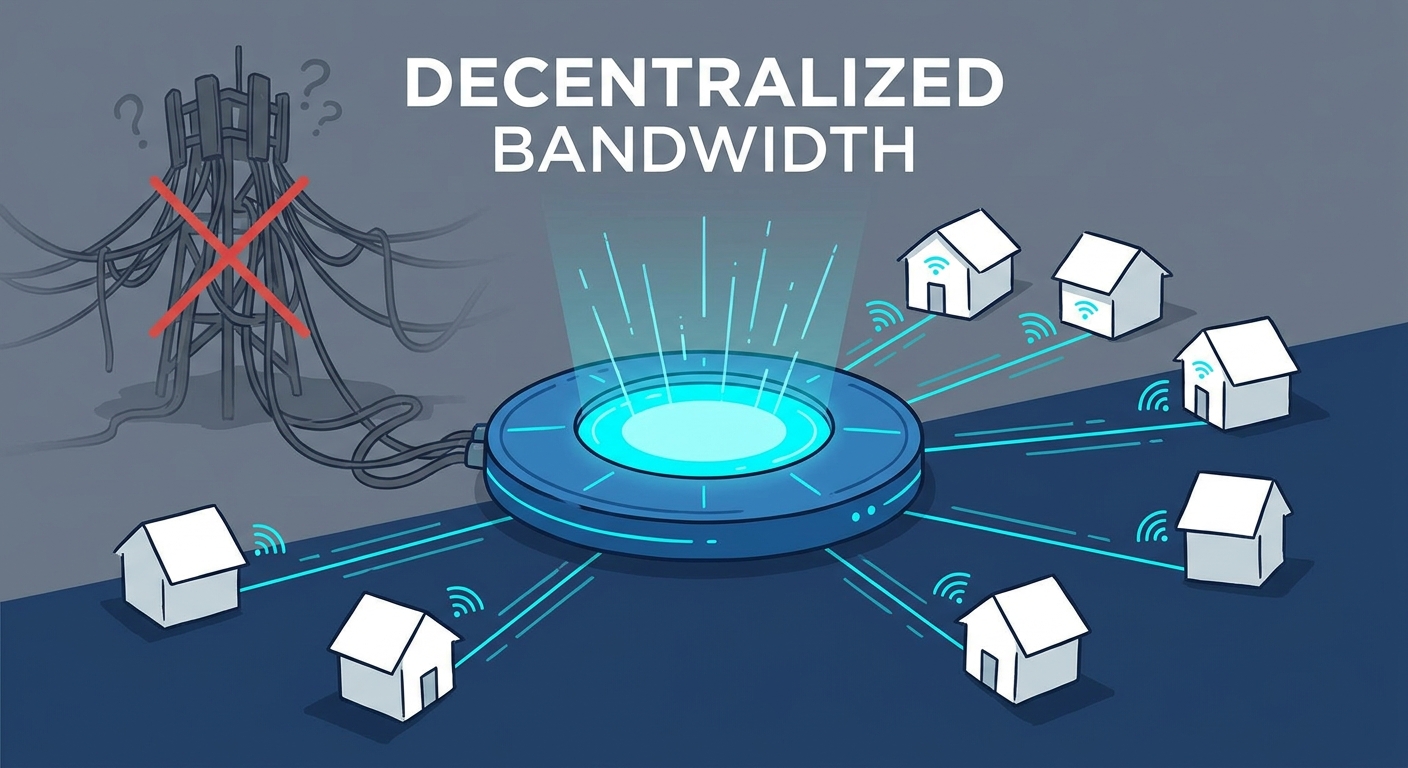
Decentralized VPNs (dVPNs) don't play that game. They shift the burden of trust from a boardroom to a protocol. By leveraging DePIN—Decentralized Physical Infrastructure Networks—these tools let you tap into a global, peer-to-peer marketplace of bandwidth. The result? A connection that’s not just private, but mathematically impossible for a single entity to flip the kill switch on.
Why the Traditional VPN Model is Toast
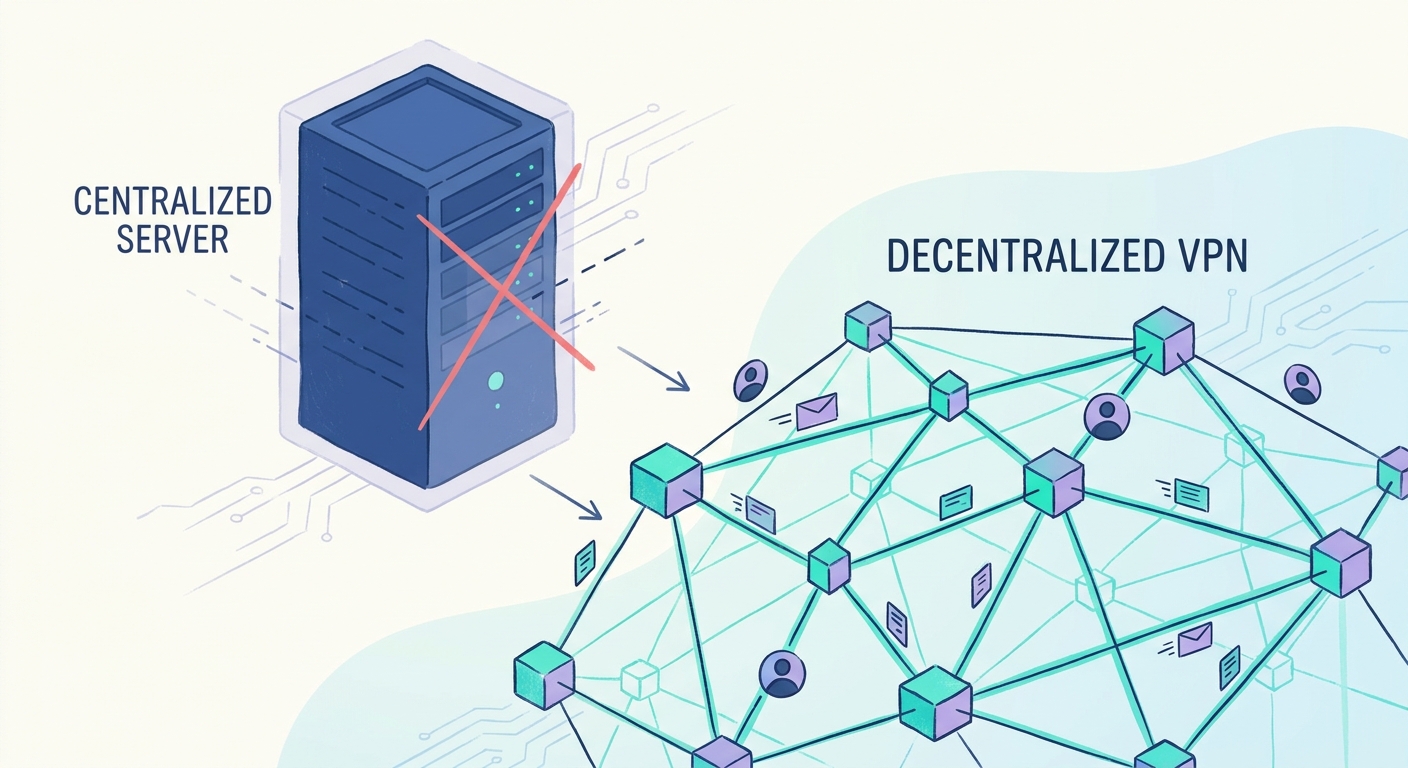
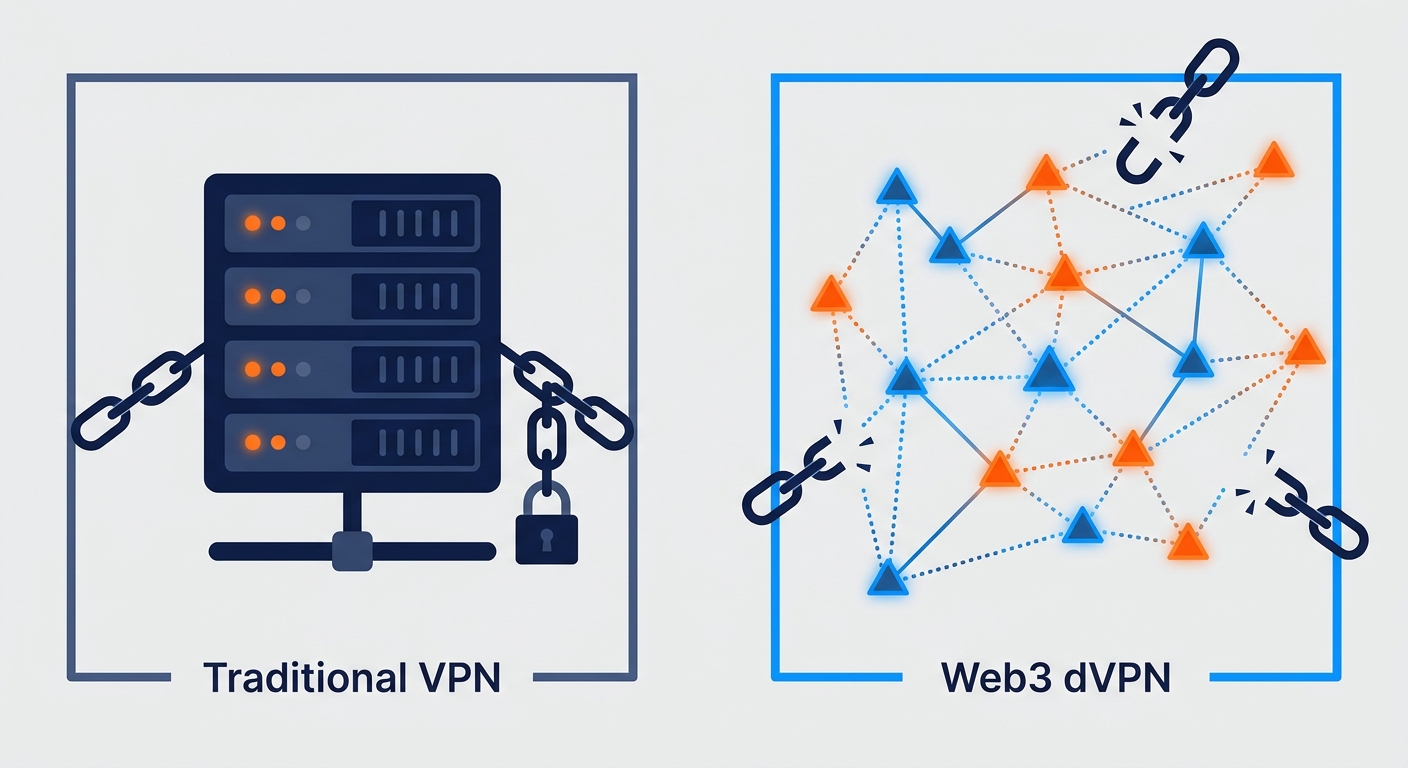
The old-school VPN model is a relic. It’s built on a "hub-and-spoke" architecture: all your data gets funneled through a static, corporate-owned data center. If a government wants to black out the web, they don’t need to hack a complex network—they just send a subpoena to the provider or blacklist their IP ranges. It’s that simple.
This is a massive privacy hole. When you use a legacy VPN, you’re betting your digital life on a single corporation’s integrity. If they get coerced, compromised, or just decide to sell your data to boost their quarterly earnings, your privacy evaporates. That’s why we’re seeing a mass exodus toward trustless architecture. In this world, the transparency of open-source code replaces the empty promises of a corporate privacy policy.
What Exactly is a dVPN?
Think of a dVPN as an Airbnb for internet bandwidth. Instead of connecting to a server owned by some anonymous company, your software links up to nodes run by individuals or small, independent operators across the globe. These nodes are dynamic, constantly rotating, and geographically scattered.
Because your traffic hops through these nodes, the final "exit node"—where your data hits the open internet—has no idea who you are. Your ISP? They’re just as clueless. It’s a mesh of connections that makes state-level firewalls look like they're trying to play whack-a-mole in the dark.
How We Picked the Winners
We ignored the marketing fluff and focused on blockchain privacy principles. Here’s the rubric we used:
- Open-Source Code: If the client isn’t fully auditable, it’s not Web3. Period.
- Node Distribution: The network needs a massive, global footprint. If all the nodes are in one country, it’s not censorship-resistant.
- Wallet-Integration: We wanted dApps that play nice with non-custodial wallets like Rabby or MetaMask.
- Censorship Resilience: How well does it handle packet obfuscation? Can it actually slip past deep packet inspection (DPI)?
Top 7 Web3 VPNs for 2026
1. Mysterium (Best for Global Coverage)
Mysterium arguably has the most mature network in the game. It’s a true P2P marketplace where anyone can turn their spare bandwidth into an exit node. This creates a massive, chaotic, and diverse pool of IPs that geo-blocking filters absolutely hate.
- Pros: Massive node count, polished user experience.
- Cons: Speed depends on the specific node you choose.
- dApp: mysterium.network
2. Sentinel (Best for Power Users)
Built on the Cosmos SDK, Sentinel is built like a tank. It’s modular, robust, and designed for people who actually care about the architecture beneath the hood. It’s the platform of choice for developers building their own privacy tools.
- Pros: Incredibly secure, strong community governance.
- Cons: If you aren't tech-savvy, the learning curve is a bit of a climb.
- dApp: sentinel.co
3. Orchid (Best for Micro-payments)
Orchid’s "probabilistic nanopayment" system is genius. Forget monthly subscriptions—you pay for exactly what you use, in tiny increments, via OXT tokens or stablecoins. It’s pay-as-you-go, just like electricity.
- Pros: No subscription trap; hyper-efficient costs.
- Cons: You need to keep a wallet balance topped up.
- dApp: orchid.com
4. Deedee (Best for Mobile-First)
Deedee is for those of us who live on our phones. It hides all the complex "Web3" stuff behind a one-tap interface. It feels like a standard app, but underneath, it’s routing your traffic through a decentralized mesh.
- Pros: Simple, clean, and fast for mobile browsing.
- Cons: Less manual control over node selection.
5. VPN.io (Best for Onboarding)
VPN.io is the bridge. They use account abstraction to let you sign up with an email and handle gas fees in the background. It feels like a Web2 service, but it runs on Web3 rails.
- Pros: The easiest way to get started; feels familiar.
- Cons: A bit more centralized than the "pure-play" dVPNs.
6. Akash-powered Mesh (Best for Performance)
By tapping into the Akash Network’s decentralized cloud compute, this solution uses high-end server hardware for exit nodes. The result? Much lower latency and speeds that actually hold up for streaming.
- Pros: Reliable, fast, and stable.
- Cons: You’ll pay a premium for that hardware.
7. PrivateNet (Best for Heavy Censorship)
PrivateNet is the heavy-duty option for journalists and activists. It focuses entirely on stealth and obfuscation, using proprietary routing to hide the fact that you’re using a VPN at all.
- Pros: Unmatched stealth in high-risk environments.
- Cons: Intended for niche use; higher latency due to heavy encryption.
How to Set Up Your First Web3 VPN
- Get Your Wallet Ready: Install a browser wallet like Rabby or MetaMask. Toss a few bucks of the native token or a stablecoin in there for gas.
- Pick Your Node: Open the dashboard. It’s like picking a server in an old-school multiplayer game—check the location, price, and latency.
- Connect: Click the button. The dApp handles the handshake. Pro tip: while you're at it, secure your digital footprint by disabling WebRTC and location services in your browser.
The "Exit Node" Elephant in the Room
People often worry: "If I run a node, am I responsible for the traffic passing through it?" It’s a fair question. The good news is that most modern dVPNs use Tor-style cryptographic routing. The exit node operator literally cannot see the content of the traffic or the identity of the user. By tracking the state of internet censorship, we know these networks are built specifically to shield node operators from liability. Still, it’s always smart to check your local laws before turning your hardware into a public node.
Are We There Yet?
The shift from "fiat-to-token" is happening right now. A year ago, using a dVPN was a nightmare of liquidity pools and gas fee calculations. Today? Account abstraction and fiat gateways mean you can pay with a credit card and let the protocol handle the rest.
The "Web3" label is becoming invisible, which is exactly how it should be. Moving to a trustless architecture isn't just for the crypto-obsessed anymore. It’s the only logical step for anyone who values an open, uncensored internet.
Frequently Asked Questions
Is a dVPN faster than a traditional VPN?
It’s a mixed bag. Because dVPNs are P2P, latency can be higher if you pick a node halfway across the planet. However, because you aren't stuck on a single, throttled corporate server, you can often hop to a better node the second you feel your speed dropping.
Can I get in legal trouble for being a node operator?
Most protocols are designed to keep the operator separate from the data. You’re providing infrastructure, not content. That said, the law moves slower than tech. Always do a quick check on your local regulations.
Do I need crypto to use a decentralized VPN?
Not anymore. Many 2026-era dVPNs use account abstraction, letting you pay in fiat currency that gets swapped for tokens behind the scenes.
Are dVPNs actually "no-logs" or is that just more marketing?
In a traditional VPN, "no-logs" is just a pinky-promise. In a dVPN, it’s a technical reality. Since there is no central server, there is no database for a company to turn over, even if they wanted to.
How does a dVPN handle state-level firewalls?
Traditional VPNs use static IPs that get blacklisted in seconds. dVPNs use rotating, dynamic node pools. If the government blocks one node, your client just jumps to the next one. It’s a game of whack-a-mole they can’t win.