Architecture of Censorship-Resistant Mesh Networks for Decentralized Internet Access

TL;DR
The shift from centralized hubs to p2p mesh architecture
Ever tried to load a webpage only to find it's been "vanished" by some government firewall? It is honestly one of the most frustrating things about the modern web, where a few central hubs basically hold the keys to everything we see.
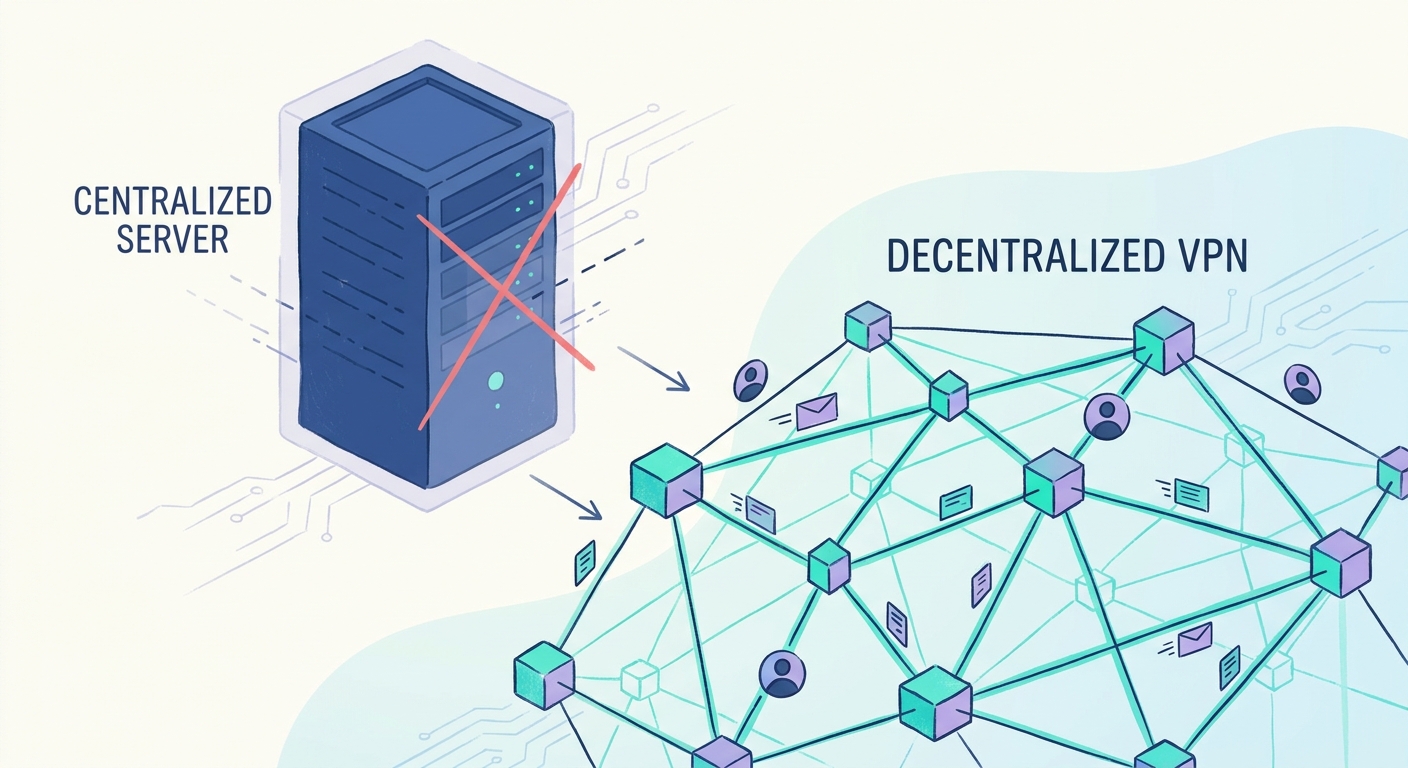
The problem is that our current internet relies on a "hub-and-spoke" model. If a censor—like a government or a massive isp—blocks the central hub, everyone connected to it loses access.
- DNS Hijaking: According to ERIC KIM, countries like turkey have used dns blocks to silence sites like Wikipedia and Twitter by redirecting requests to "dead" servers.
- Single Points of Failure: When you rely on one server, it’s easy for a censor to just "pull the plug" on that specific ip address.
- Big Tech Monopolies: A few companies control the flow of info, meaning they can shadowban or delete content without any real oversight. (Platform Visibility and Content Moderation: Algorithms, Shadow ...)
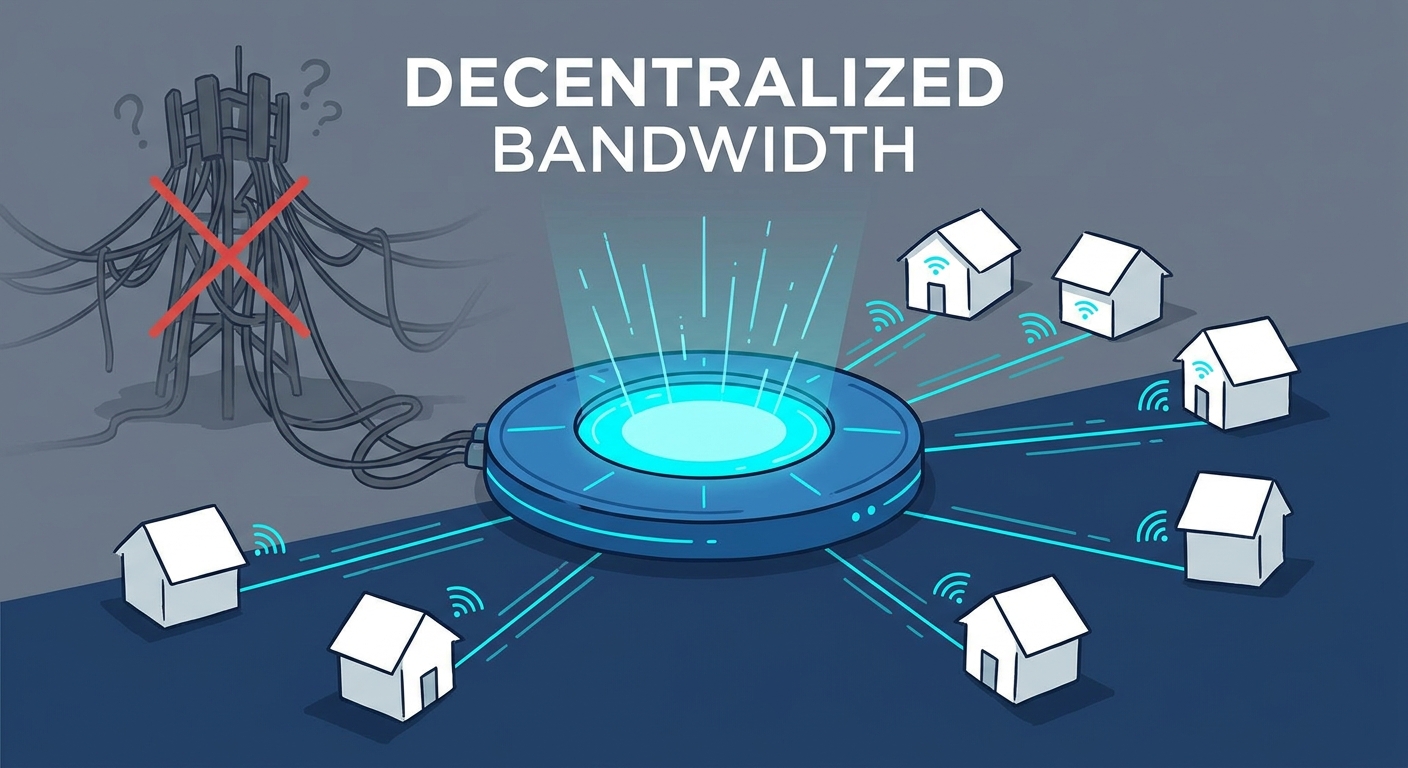
Mesh networks flip this on its head by letting nodes connect directly to each other. Instead of one big server, the "network" is just a bunch of people sharing bandwidth.
- No Middleman: Traffic hops from peer to peer, so there isn't a central isp that can easily monitor or block the whole thing.
- Distributed Hash Tables (dht): These replace old-school indexing, so finding data doesn't require a central "google-style" directory.
- Covert Channels: This is the cool part. Tools like the CRON project use WebRTC to hide data inside normal-looking video calls. To a censor, it just looks like you're chatting on zoom, but you're actually moving forbidden data through the "noise" of the video stream.
In practice, this means if one node gets blocked, the data just routes around it through another friend. It’s like a digital game of "telephone" that never ends. To make this work though, we need a solid stack of tech layers so the whole thing don't collapse.
Layered design of a decentralized internet
Think of the decentralized internet like a high-tech layer cake. It isn't just one big blob of code; it’s a stack of different technologies working together so that if a government tries to cut one wire, the data just finds a different path. We can break it down into four main parts:
- Layer 1: The Infrastructure/Mesh Layer: This is the physical connection. Instead of relying on a big ISP cable, nodes use radio, bluetooth, or local wifi to talk directly to neighbors.
- Layer 2: The Routing/Onion Layer: This is where the actual bits and bytes move privately. We use "onion routing" (like the tor network) where each piece of data is wrapped in layers of encryption. A node only knows where the data just came from and where it’s going next—never the full path.
- Layer 3: The Storage Layer: We use content-addressable storage via systems like ipfs. Instead of asking for a file by its "location" (like a URL that a censor can block), you ask for it by its unique cryptographic fingerprint. According to a Georgetown University presentation, building general-purpose systems that provide "cover traffic" is a key way to stop adversaries from just shutting down the whole network.
- Layer 4: The Economic Layer: Why would someone run a node for you? By using the btc lightning network, we can do tiny micropayments—literally fractions of a cent—to pay people for sharing their bandwidth. It’s basically an "Airbnb for bandwidth."
A 2025 report by Liberty Street Economics noted that while some actors might cooperate with sanctions, the system stays resilient because large players value "censorship resistance as a primitive feature."
This setup means you can earn "sats" just by letting your router help someone else bypass a firewall. It turns privacy into a marketplace. But even with a good stack, there is still some massive technical hurdles to jump over.
Technical challenges in censorship resistance
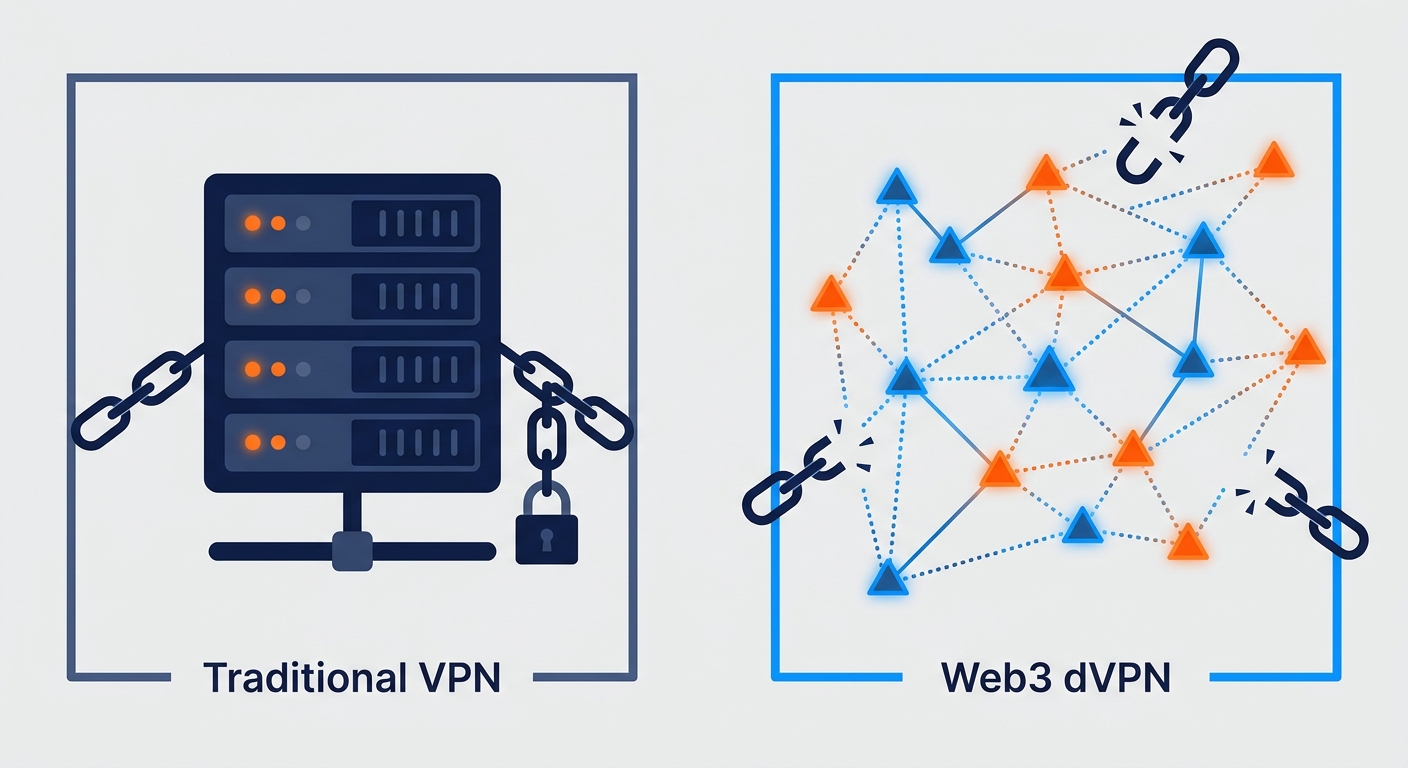
It’s one thing to build a mesh network, but keeping it alive when a nation-state is actively trying to kill it? That’s the real "boss level" of networking. Censors aren't just blocking IPs anymore; they’re using ai to sniff out patterns in your encrypted data.
Even if your data is scrambled, the shape of the traffic gives it away. If you’re sending bursts of data that look like a vpn, you’re toast.
- Traffic Analysis: Censors use machine learning to spot the "heartbeat" of encrypted protocols. This is why those Covert Channels we mentioned earlier (like CRON) are so important—they make the traffic look like a boring video call.
- Steganography: You can actually embed bits into video frames. If the censor tries to inspect the "video" feed, they just see pixels, not the forbidden data hidden inside.
- Sybil Attacks: A big challenge is when the censor joins the network themselves. They can run thousands of fake nodes to map out who is talking to who. To fight this, some systems use "Social Trust" models where you only route through people your direct contacts actually know.
Staying ahead of these threats requires constant updates. If you want to keep up, you should check out the Privacy Guides forum or follow the Nym Technologies blog. GitHub repos for projects like I2P or Loki are also great places to see how devs are fighting back against ai-driven sniffing.
Identity and discovery without a master server
So, how do we find friends in a mesh without a big boss watching? It’s all about owning your keys.
Forget icann and the traditional dns system where a government can just "delete" your domain name. We use systems like Handshake or ENS (Ethereum Name Service) to handle names. These use blockchain ledgers to store domain records. Because the ledger is distributed across thousands of computers, there is no single entity that can "revoke" or seize a domain name once it's registered.
Your identity is just a cryptographic keypair—no passwords to steal.
- Public Keys: These act as your permanent id.
- nostr Protocol: It uses relays to pass signed messages, as mentioned earlier by Eric Kim.
Here is how a basic nostr event looks in json:
{
"pubkey": "32e18...",
"kind": 1,
"content": "Hello mesh world!",
"sig": "a8f0..."
}
When you combine these decentralized identities with a layered mesh architecture, you get a web that doesn't have a "kill switch." The mesh provides the physical path, the onion routing provides the privacy, and blockchain-based naming ensures you can always find your destination. It’s a lot of moving parts, but for the first time, the tech is actually fast enough to work in the real world. Anyway, decentralized tech is finally ready. Stay safe out there.