Top 7 Web3 VPNs for Censorship-Resistant Internet Access in 2026
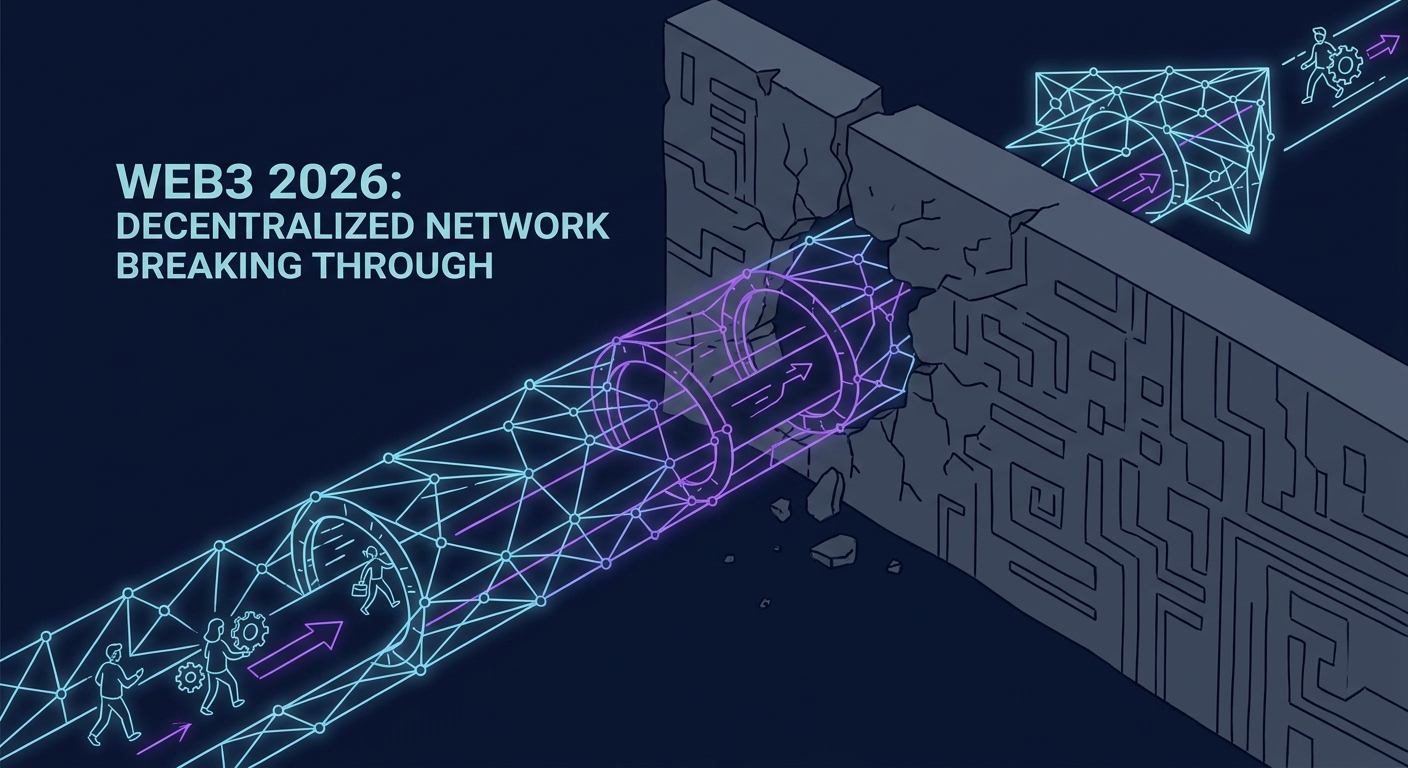
By 2026, the digital border isn't just a concept—it’s a wall of silicon and code. If you’re still relying on a traditional, centralized VPN to dodge firewalls or corporate censorship, you’re basically knocking on the front door of the very people trying to lock you out.
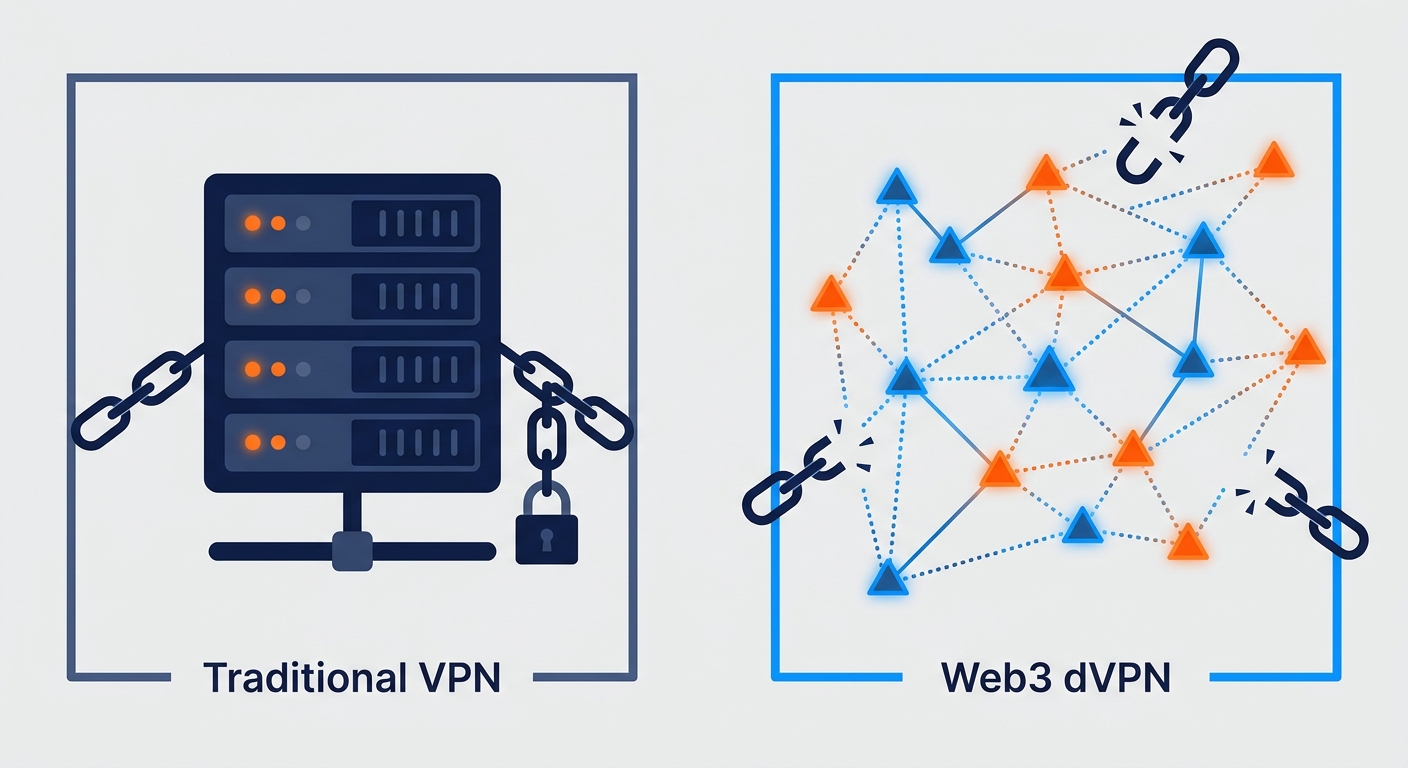
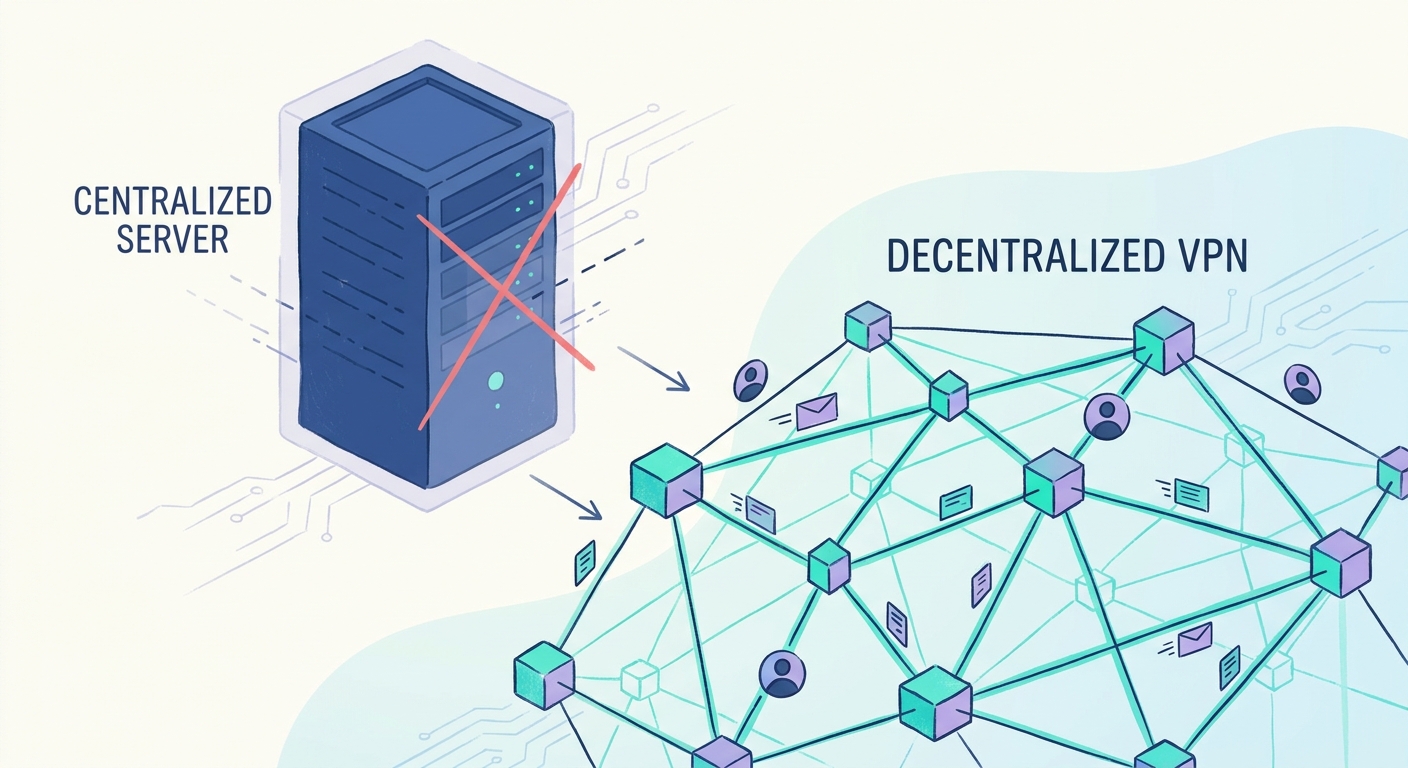
When you route your life through a static, identifiable server farm, you’re handing censors a single point of failure. They don’t even have to work hard; they just blacklist the IP, throttle the connection, and wait for you to give up. If you want to reclaim your internet, you have to stop playing by their rules. You need to go decentralized.
Why Are Traditional VPNs Failing in 2026?
The "Big VPN" era is dead on its feet. Most mainstream providers rely on massive, centralized data centers. These are just giant, static targets. Think about it: a server farm has a fixed IP address. It’s trivial for a government or ISP to identify, flag, and throttle.
When you connect to one of these services, your traffic leaves a distinctive, predictable cryptographic fingerprint. Modern Deep Packet Inspection (DPI) tools can sniff this out in milliseconds. Once the ISP identifies your protocol, they don’t necessarily block you outright—they just degrade your connection until the internet becomes a laggy, unusable mess.
This game of cat and mouse is rigged because the censor holds all the cards. Understanding why privacy matters in 2026 is the first step toward realizing that the solution can't come from a company that keeps logs, maintains centralized hardware, and answers to subpoenas.
What Exactly is a Decentralized VPN (dVPN)?
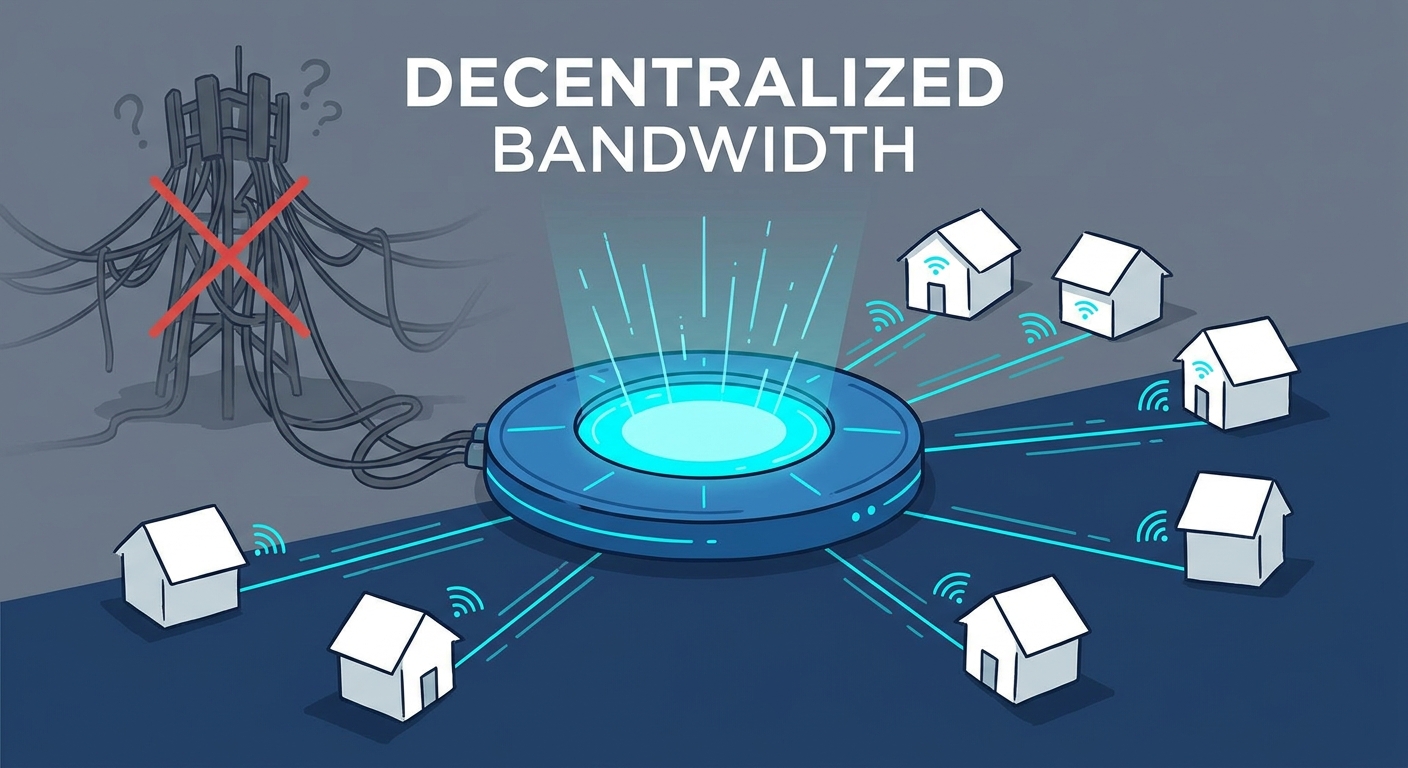
A dVPN isn't a company. It’s a protocol. By leveraging DePIN—or Decentralized Physical Infrastructure Networks—these platforms turn the internet into a massive, peer-to-peer marketplace.
Instead of routing through a corporate-owned server, your data hops through a global network of independent, residential nodes run by real people. It’s essentially an "Airbnb for bandwidth." Because every hop is a residential connection, there is no "master IP list" for a censor to block. If one node drops off the map, the network simply reroutes you through another. It’s fluid, it’s resilient, and it’s remarkably hard to kill.
How Do We Evaluate dVPNs for This List?
Forget the marketing fluff. To find the tools that actually work in 2026, we looked at the tech, not the hype. Here’s the rubric:
- DPI Resilience: Can the traffic camouflage itself as standard HTTPS or just background noise?
- Node Diversity: Is the network truly peer-to-peer, or is it just a decentralized skin on a single company’s hardware?
- Zero-Knowledge Proofs (ZK-Proofs): Can the system verify your access rights without ever knowing who you are or what you’re looking at?
- Token Utility: Is the native currency actually securing the network, or is it just a speculative casino chip?
The Top 7 dVPNs for Unrestricted Access
1. Nym: The Gold Standard
Nym is the heavy hitter for multi-hop obfuscation. It uses a "mixnet" architecture that doesn't just encrypt your data—it scatters it. By injecting "decoy" traffic, Nym makes it mathematically impossible for an observer to correlate the person entering the network with the person leaving it. According to Nym’s latest research, this traffic-pattern masking is the only real way to defeat the AI-driven surveillance state.
2. Mysterium: The User-Friendly Pick
Tired of juggling complex crypto-wallets and command-line interfaces? Mysterium is for you. They’ve managed to abstract away the blockchain nightmare, giving you a plug-and-play experience. You get the benefits of a massive, global P2P network, but it feels like a standard subscription service. It’s the easiest bridge from the "old" internet to the new one.
3. Sentinel: The Incentive Engine
Built on the Cosmos SDK, Sentinel nails the node-operator incentive model. By rewarding operators based on the quality and uptime of their service, they’ve created a hyper-competitive ecosystem. If you want a network that is constantly optimizing itself for speed and reliability, this is it. It’s robust, it’s fast, and it’s built to scale.
4. Orchid: The Mobile Masterpiece
Orchid’s "probabilistic nanopayment" system is a genuine work of engineering art. You pay for bandwidth in tiny, fraction-of-a-cent increments as you go. This makes it incredibly efficient for mobile users who want to jump between nodes without signing up for a monthly bill. It’s pay-as-you-go privacy at its finest.
5. Akash Network: The Enterprise Powerhouse
While Akash is primarily a decentralized cloud computing platform, its ability to spin up private VPN nodes on-demand is a game-changer. If you need a dedicated, private exit node that only you use, Akash lets you rent the hardware yourself. You become your own VPN provider. It’s not for the casual user, but for those who need maximum control, it’s unbeatable.
6. Bantu VPN: For the Speed Freaks
Decentralized doesn't have to mean slow. Bantu focuses heavily on regional node clusters, keeping latency lower than almost any other dVPN on the market. It’s optimized for streaming and real-time comms, proving that you don't have to sacrifice speed to get privacy.
7. PrivaNode: For the Anonymous Purist
PrivaNode takes the "no-KYC" mandate to the extreme. They’ve integrated privacy-focused coins directly into the connection handshake. The act of paying for the service is just as anonymous as your browsing history. They leave absolutely no financial trail for censors to follow.
How Do You Choose the Right dVPN for Your Needs?
Choosing a dVPN is a balancing act between speed, budget, and your specific threat model.
Are you just trying to watch a show from another country? Look for protocols with high node density in your target region. Are you an activist working in a high-risk environment? Forget speed; prioritize multi-hop obfuscation and ZK-proofs above all else.
Whatever you choose, take a moment to learn how to secure your connection to avoid rookie mistakes like DNS leaks or browser fingerprinting. The best tool in the world won't save you if you’re leaking your identity at the browser level.
Frequently Asked Questions
Are dVPNs legal to use for bypassing censorship?
The legality depends on where you live. While the tech itself is a neutral tool for privacy, some regions have draconian laws regarding the bypass of state-controlled internet. Always do your homework on your local regulations before committing.
Are dVPNs slower than traditional VPNs?
Historically, they were. In 2026, the gap has closed significantly. Because dVPNs use a distributed P2P node network, you can often pick a node that is physically closer to your actual location than a centralized server farm. Sometimes, they’re even faster.
Do I need crypto to use a dVPN?
Not necessarily. Many modern dVPNs, like Mysterium, have built "fiat-to-crypto" bridges. They hide the complexity of wallets and tokens, letting you pay via traditional methods while still tapping into the decentralized backbone.
Can my ISP see that I'm using a dVPN?
Advanced dVPNs use obfuscation layers to make your traffic look like standard HTTPS or TLS traffic. While an ISP can see that you’re connected to something encrypted, the top protocols make it statistically impossible for them to distinguish your traffic from someone just reading the news. It renders DPI effectively useless.
For more information on the landscape of decentralized privacy, check out the Decentralized VPNs Overview.