Airbnb for Bandwidth: How Blockchain Bandwidth Monetization is Disrupting Traditional ISPs
You’re paying an "ISP Tax" every single month. It’s a bill for a service that treats you like a captive audience with no other options. You shell out cash for a gigabit connection that sits there, doing absolutely nothing, while you’re out living your life or sleeping. In exchange, your provider throttles your speed, keeps a ledger of every site you visit, and sells that data to whoever writes the biggest check.
But the tide is shifting. We’re watching the birth of a decentralized bandwidth economy—a movement often called "Airbnb for bandwidth." It’s a total power move. We’re taking the ability to manage, share, and monetize connectivity away from the corporate gatekeepers and putting it back in the users' hands. By understanding the decentralized bandwidth economy, you stop being a passive consumer and start participating in a peer-to-peer, tokenized infrastructure that actually gives you back some digital sovereignty.
What is "Airbnb for Bandwidth"?
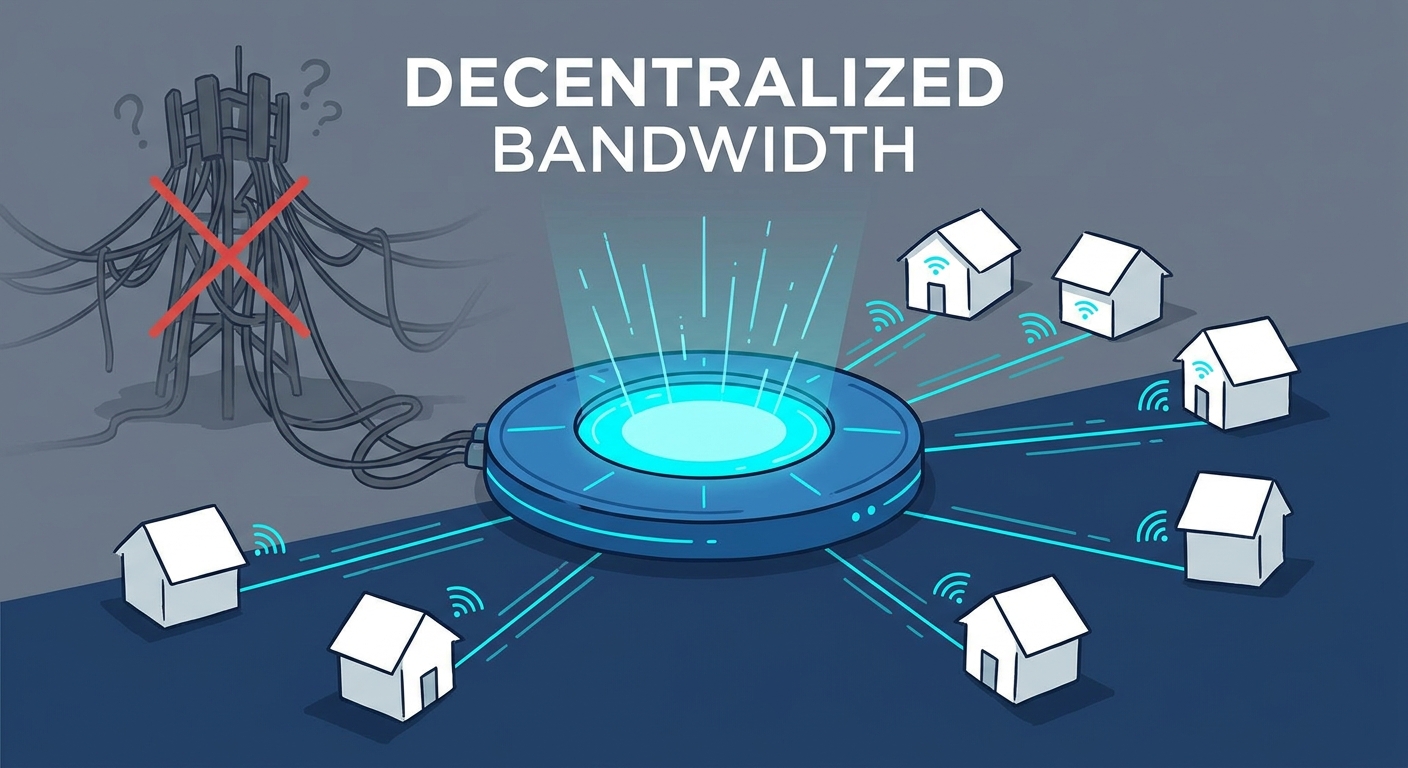
Think of it as the practical application of Decentralized Physical Infrastructure Networks—or DePIN, if you want to use the industry shorthand. Just as Airbnb turned your spare bedroom into a revenue stream, these protocols turn your spare internet bandwidth into a digital asset.
If you have a high-speed fiber connection that’s just idling for 20 hours a day, you’re sitting on untapped value. DePIN platforms let you lease that unused capacity to a global network of users, researchers, and companies who need secure, localized routing.
This is the jump from "consumer" to "prosumer." You aren’t just the end of the pipe anymore; you’re a vital node in a global mesh. By providing resources to the network, you earn native tokens. Suddenly, that monthly utility bill isn't just a cost—it’s a foundation for a passive income stream. For a deeper look at the broader implications of these systems, this guide on DePIN explains how this decentralized shift is reshaping the physical world. You aren't just making money here; you’re helping build a censorship-resistant internet that no single CEO can flip a switch on.
How Does the Architecture Shift Work?
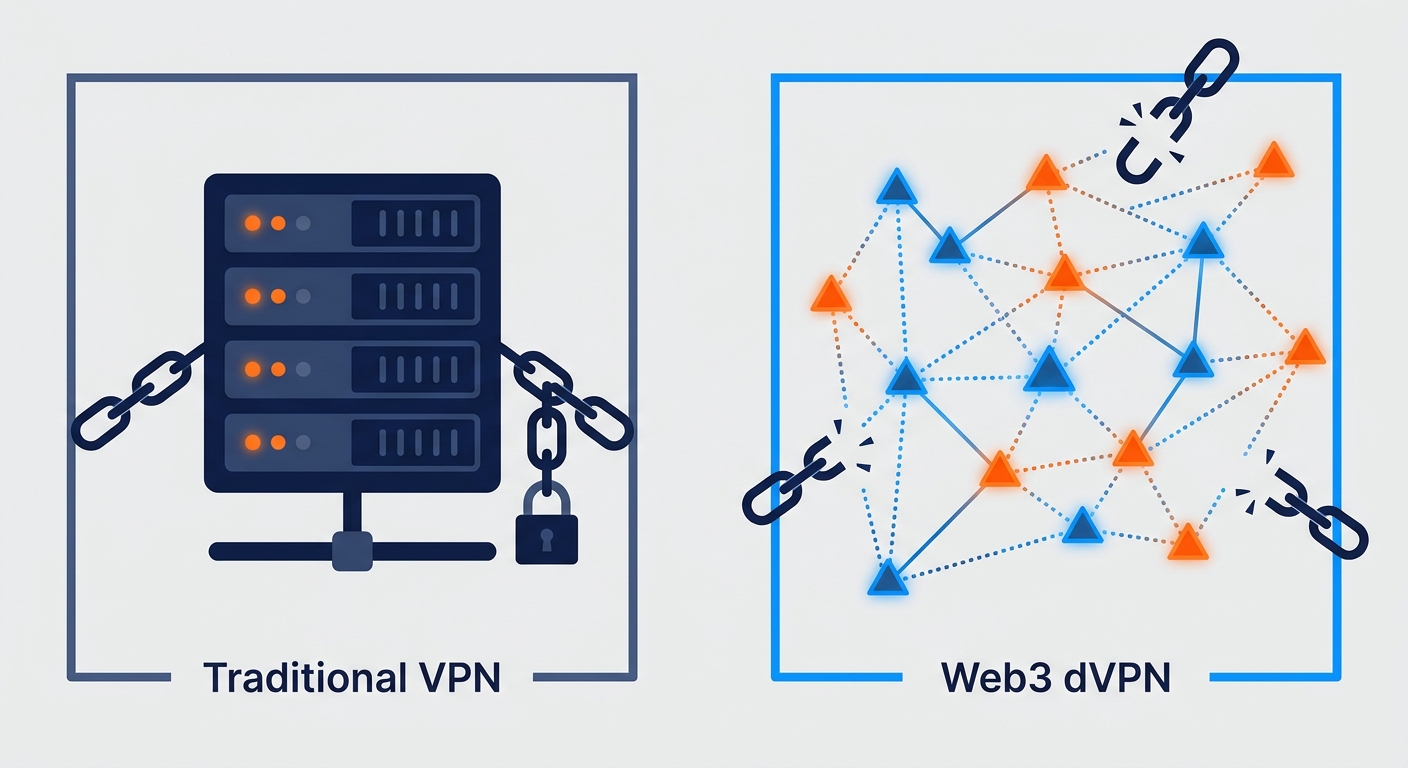
Your traditional ISP is stuck in the past. They use a "Hub-and-Spoke" model. Your data hits a central server they own, and then it’s routed to its destination. It’s a massive single point of failure. It’s also a chokehold for censorship. If your ISP wants to throttle your connection or block a specific site, you’re powerless.
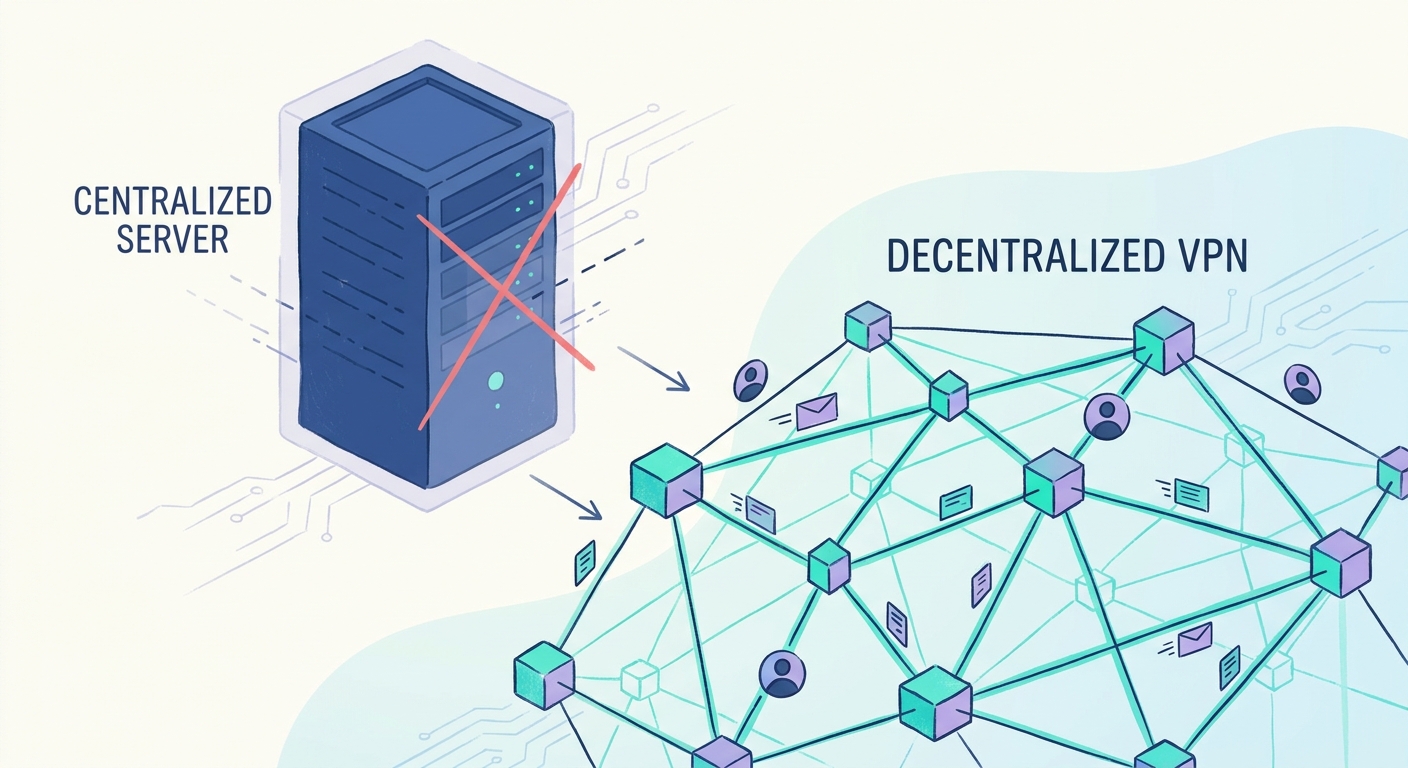
The DePIN model flips the script by using a mesh network architecture. There is no central authority. Traffic is routed through a distributed web of individual nodes. If one path gets blocked, the network just finds another.
This redundancy is the death knell for regional throttling. When you’re part of a decentralized network, your connection isn't tied to the whims of a local ISP’s traffic policies. You’re part of a global, resilient fabric that forces net neutrality through code, not corporate promises.
Why Are Users Abandoning Traditional ISPs?
It’s not just about the crypto earnings. It’s about a desperate, growing need for privacy and freedom. Traditional ISPs are notorious for double-dipping: they charge you to access the web, then they monetize the data they track on that same connection.
Decentralized VPNs (dVPNs) offer a clean break. As highlighted in this analysis of decentralized VPNs, these networks remove the middleman. Your traffic is encrypted and routed through nodes that have zero incentive to log your data.
Censorship resistance is the other big win. Whether it’s a government blocking social media or an ISP throttling your streaming just to force you into their expensive cable bundles, the decentralized model lets you bypass those barriers. Because your traffic is distributed across multiple nodes, it is mathematically difficult for any central entity to identify or block what you’re doing. You’re effectively "routing around" the censorship. This is a direct challenge to the black-box nature of legacy infrastructure. When you use a decentralized network, the rules are governed by open-source smart contracts, not some hidden Terms of Service agreement that allows the provider to change the game whenever it suits their bottom line.
Is Your Internet Connection Ready for Web3?
Becoming a node provider sounds like a job for a network engineer, but the barrier to entry today is surprisingly low. Modern "Proof-of-Bandwidth" protocols are designed to run on low-power devices, from small-form-factor PCs to simple software containers running on hardware you already own. These protocols measure your contribution—latency, uptime, and throughput—and reward you for it.
This is the birth of edge computing at the household level. Your node isn't just relaying packets; it’s becoming a localized content delivery center. By hosting data closer to the user, these networks reduce lag and make the entire global internet faster. Understanding how blockchain throughput functions is key here. As these networks scale, the ability to handle high-speed data transfers becomes the primary metric of a node's value. We’re moving toward a world where your internet connection is a productive participant in a global compute market, not just a passive utility.
What Are the Real Risks and Challenges?
Let’s be honest about the risks. The "elephant in the room" is legal liability. If you’re an exit node for a decentralized network, traffic from other users is leaving the internet through your IP address. While most providers use strong encryption and strict routing policies to ensure you’re a "blind relay"—meaning you can’t see the content of the traffic—the legal landscape is still catching up.
Then there’s the inevitable regulatory pushback. Legacy ISPs aren't going to just roll over and let their monopoly get dismantled without a fight. Expect to see more restrictive "Acceptable Use Policies" that try to classify bandwidth sharing as a contract violation. But because these networks are decentralized, they're inherently resistant to a "kill switch." If one node goes down, a hundred more pop up to replace it. Security-wise, you’re acting as a firewall. You need to keep your node software updated and stick to reputable, audited protocols to prevent bad actors from exploiting your hardware.
How to Become a Bandwidth Provider
Getting started is easier than you think. Most providers just need a stable connection and a compatible device. You download the node client, link your digital wallet, and set your bandwidth limits.
Keep your expectations in check: this isn't a "get rich quick" scheme. Token yields fluctuate with demand, and market saturation can shift your earnings. For those ready to dive into the technical setup and optimize their passive income, this guide on bandwidth monetization offers a solid roadmap for 2026 and beyond.
Conclusion: The Future of Connectivity
The shift toward a decentralized internet isn't an "if," it’s a "when." We’re heading for an era where connectivity is a commodity, traded on open markets by the very people who consume it. The legacy giants will fight to hold onto their control, but the efficiency and privacy benefits of DePIN are too great to ignore. As the world goes decentralized, make sure your privacy keeps pace. If you’re ready to take control of your digital presence, secure your connection with SquirrelVPN and join the movement toward a truly open network.
Frequently Asked Questions
Is it legal to monetize my internet bandwidth?
In most jurisdictions, you have the right to utilize your property as you see fit. While ISPs may include clauses in their Terms of Service (TOS) prohibiting commercial use, decentralized networks operate as private, encrypted tunnels. You are generally acting as a participant in a peer-to-peer network, which is a protected form of digital infrastructure.
Does sharing my bandwidth slow down my own connection?
Most protocols include Quality of Service (QoS) settings. You can cap the bandwidth you contribute, ensuring that your own browsing, gaming, or streaming remains entirely unaffected. You are in total control of how much "spare" capacity you offer to the network.
What are the security risks of becoming a bandwidth node?
Node operators act as "blind relays." Because the traffic is encrypted end-to-end, you cannot see or log the content passing through your node. Reputable protocols also employ strict exit policies to protect node operators, ensuring you are not responsible for the data being transmitted.
How much can I realistically earn in 2026?
Earnings depend on your geographic location, your uptime, and the current demand for bandwidth in your region. It is best viewed as a way to offset the cost of your monthly internet bill rather than a full-time salary. Consistency and reliable, high-speed hardware are the keys to maximizing your token yield.